- 快召唤伙伴们来围观吧
- 微博 QQ QQ空间 贴吧
- 文档嵌入链接
- 复制
- 微信扫一扫分享
- 已成功复制到剪贴板
GDPR: The catalyst for customer 360
展开查看详情
1 .The GDPR: The catalyst for customer 360 5 July 2017
2 . TM Speakers www.itgovernance.co.uk Alan Calder Tim Vincent Founder and Executive Chairman, EMEA Solution Engineer Team IT Governance Ltd Lead DataStax Copyright IT Governance Ltd 2017 – v1.0
3 . TM Introduction www.itgovernance.co.uk • Alan Calder • Founder, IT Governance Ltd • The single source for everything to do with IT governance, cyber risk management and IT compliance • IT Governance: An International Guide to Data Security and ISO27001/ISO27002 (Open University textbook) • www.itgovernance.co.uk Copyright IT Governance Ltd 2017 – v1.0
4 . TM IT Governance Ltd: GRC One-stop shop www.itgovernance.co.uk All verticals, all sectors, all organisational sizes Copyright IT Governance Ltd 2017 – v1.0
5 . TM We will cover: www.itgovernance.co.uk • The GDPR’s impact on businesses • Accountability and governance of data, data storage limitations, breach notifications, data subject rights, and compliance requirements • Unravelling the labyrinthine web of data using DataStax Enterprise Graph to bring legacy systems together and comply with the GDPR, building a 360-degree view of a company’s data subjects • The right to be forgotten and how DataStax Enterprise Graph can help companies comply with the Regulation’s requirements Copyright IT Governance Ltd 2017 – v1.0
6 . TM The GDPR’s impact on businesses www.itgovernance.co.uk • Differentiating between controllers and processors – Critical that entities identify, in respect of their processing, whether they are a controller or a processor: – ‘Controller' means the natural or legal person, public authority, agency or other body which, alone or jointly with others, determines the purposes and means of the processing of personal data. – ‘Processor' means a natural or legal person, public authority, agency or other body which processes personal data on behalf of the controller. – Processors may only process data in line with a contract from a controller. • Child’s consent: – A person under 16 years old may not consent to the processing of personal data in respect of an information age service. • Customer service: – Privacy notices will be more intrusive. – Additional services and options can’t assume consent. – Third party processors will have to be clearly identified. – Big data activities may be restricted. Copyright IT Governance Ltd 2017 – v1.0
7 . TM Material and territorial scope www.itgovernance.co.uk Natural person = a living individual • Natural persons have rights • In material scope: associated with: – Personal data that is – The protection of personal processed wholly or partly by data. automated means. – The protection of the – Personal data that is part of a processing of personal data. filing system, or intended to – The unrestricted movement of be. personal data within the EU. – The Regulation applies to controllers and processors in the EU, irrespective of where processing takes place. The GDPR also applies to controllers not in the EU Copyright IT Governance Ltd 2017 – v1.0
8 . TM Entry into force and application www.itgovernance.co.uk “This Regulation shall be binding in its entirety and directly applicable in all Member States.” KEY DATES • On 8 April 2016, the European Council adopted the Regulation. • On 14 April 2016, the European Parliament adopted the Regulation • On 4 May 2016, the official text of the Regulation was published in the EU Official Journal in all the official languages. • The Regulation entered into force on 24 May 2016, and will apply from 25 May 2018. • http://ec.europa.eu/justice/data-protection/reform/index_en.htm Final text of the Regulation: http://eur-lex.europa.eu/legal-content/en/TXT/?uri=CELEX%3A32016R0679 Copyright IT Governance Ltd 2017 – v1.0
9 . TM Remedies and liabilities www.itgovernance.co.uk Natural persons have rights – Data subjects shall have recourse to judicial remedy where: º In the courts of the Member State where the controller or processor has an establishment. º In the courts of the Member State where the data subject habitually resides. – Any person who has suffered material, or non-material, damage shall have the right to receive compensation from the controller or processor. – The controller involved in processing shall be liable for damage caused by processing. Copyright IT Governance Ltd 2017 – v1.0
10 . TM Penalties www.itgovernance.co.uk Administrative fines – In each case, fines will be effective, proportionate and dissuasive – Fines administrated will take into account technical and organisational measures implemented. – €10,000,000 or, in the case of an undertaking, up to 2% of the total worldwide annual turnover of the preceding financial year. – €20,000,000 or, in case of an undertaking, up to 4% of the total worldwide annual turnover in the preceding financial year. Copyright IT Governance Ltd 2017 – v1.0
11 . TM The Rights of data subjects www.itgovernance.co.uk • “The controller shall take appropriate measures to provide any information relating to processing to the data subject in a concise, transparent, intelligible and easily accessible form, using clear and plain language (Article 11-1).” • The controller shall facilitate the exercise of data subject rights (Article 11-2). – Rights to: º Data portability; º Consent º Withdraw consent at any time; º Access º Lodge a complaint with a supervisory º Rectification authority; º Erasure º Be informed of the existence of automated decision-making, including profiling, as well º Restriction as the anticipated consequences for the º Objection data subject. Copyright IT Governance Ltd 2017 – v1.0
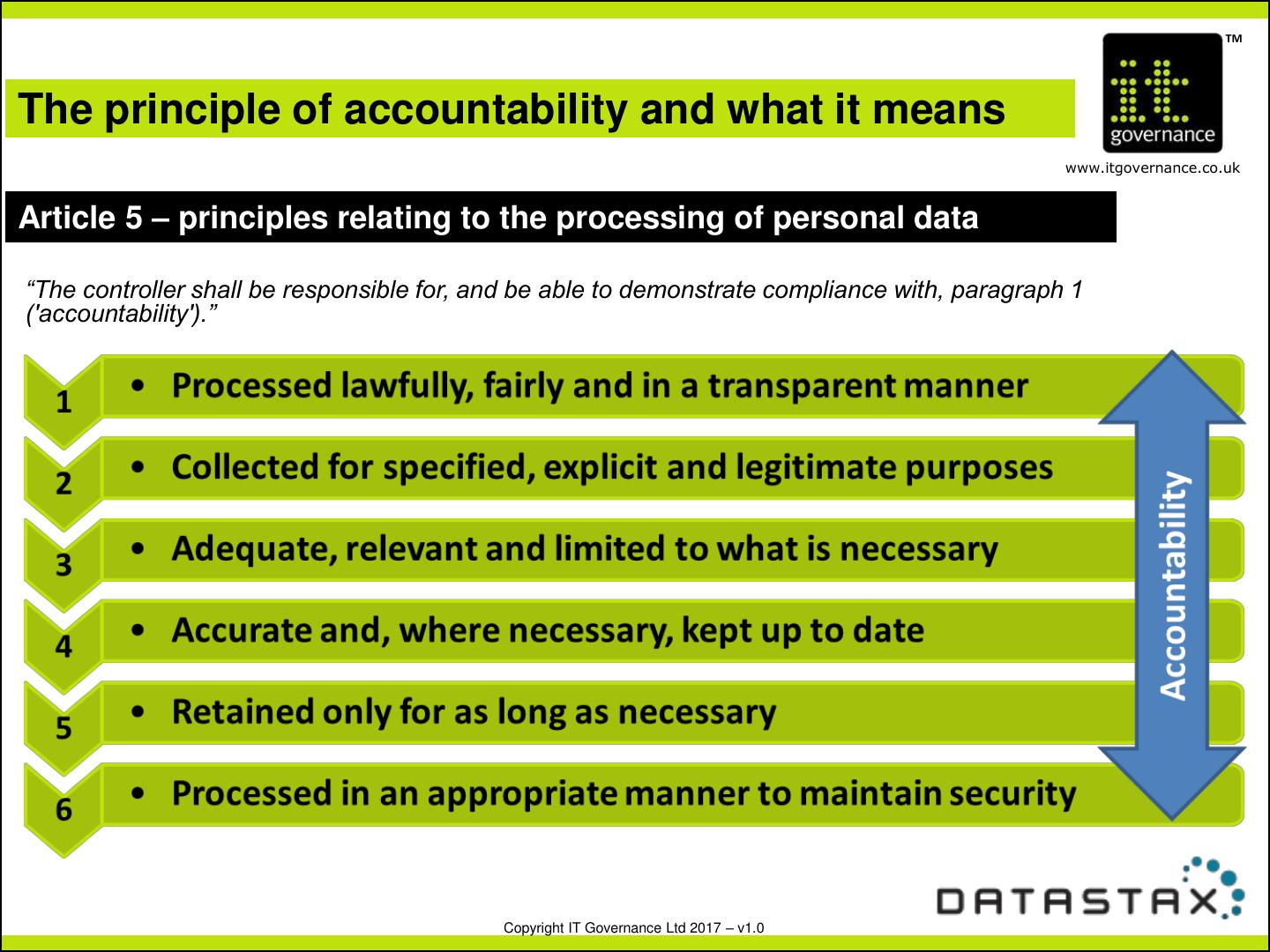
12 . TM The principle of accountability and what it means www.itgovernance.co.uk Article 5 – principles relating to the processing of personal data “The controller shall be responsible for, and be able to demonstrate compliance with, paragraph 1 ('accountability').” Copyright IT Governance Ltd 2017 – v1.0
13 . TM Lawfulness (Art 5 – 6) www.itgovernance.co.uk • Personal data must be secured against accidental loss, destruction or damage • Processing must be lawful – which means, inter alia: – Data subject must give consent for specific purposes – There are specific circumstances where consent is not required º So that the controller can comply with legal obligations, etc. • One month to respond to subject access requests – and no charges • Controllers and processors clearly distinguished – Clearly identified obligations – Controllers responsible for ensuring processors comply with contractual terms for processing information – Processors must operate under a legally binding contract º And note issues around extra-territoriality Copyright IT Governance Ltd 2017 – v1.0
14 . TM Consent (Art. 7-9) www.itgovernance.co.uk • Consent must be clear and affirmative – Must be able to demonstrate that consent was given – Silence or inactivity does not constitute consent – Written consent must be clear, intelligible and easily accessible, or it is not binding – Consent can be withdrawn any time, and it must be as easy to withdraw consent as to give it • Special conditions apply for a child (under 16) giving consent • Explicit consent must be given for processing sensitive personal data – Race, ethnic origin, political beliefs, etc. – Specific circumstances allow non-consensual processing, e.g. to protect vital interests of the data subject • Secure against accidental loss, destruction or damage (article 5) • Consent must be documented. Copyright IT Governance Ltd 2017 – v1.0
15 . TM Transparency (Art. 12-17) www.itgovernance.co.uk • Any communications with a data subject must be concise, transparent and intelligible • The controller must be transparent in providing information about itself and the purposes of the processing • The controller must provide the data subject with information about their rights • There are specific provisions (Article 14) covering data not obtained directly from the data subject • Data subjects have rights to access, rectification, erasure (‘right to be forgotten’), to restriction of processing, and data portability Copyright IT Governance Ltd 2017 – v1.0
16 . TM Privacy by design (Art. 25 et seq. ) www.itgovernance.co.uk • Privacy must now be designed into data processing by default • Data protection impact assessments are mandatory (Article 35) – For technologies and processes that are likely to result in a high risk to rights of data subjects • Documentary evidence is crucial • Data audits – The GDPR applies to existing data, as well as future data – Privacy may have to be designed retrospectively – Organisations need to identify what personal data they hold, where and on what grounds they hold it, and how it is secured in a way that will meet the requirements of the GDPR Copyright IT Governance Ltd 2017 – v1.0
17 . TM Data breaches under the GDPR www.itgovernance.co.uk Definition A 'personal data breach' means a breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorised disclosure of, or access to, personal data transmitted, stored or otherwise processed. Controller obligations Processor obligations • Notify supervisory authority no later than 72 hours after • Notify the data controller of a discovery breach without delay • Must describe the nature of • All data breaches have to be the breach reported (no exemptions) • No requirement to notify if no • European Data Protection risk to rights and freedoms of Board (EDPB) to issue natural persons clarification with regard to • Failure to report within 72 ‘undue delay hours requires explanation Copyright IT Governance Ltd 2017 – v1.0
18 . TM Data Breaches www.itgovernance.co.uk Obligation for data controller to communicate a personal data breach to data subjects • Communicate with data subjects without undue delay if the breach represents a high risk to data subjects' rights • Communication must be in clear, plain language • Supervisory authority may compel communication with data subject Exemptions • Appropriate technical and organisational measures were taken • A high risk to the data subjects will not materialise • Communication with data subjects would involve disproportionate effort Copyright IT Governance Ltd 2017 – v1.0
19 . TM Security of Processing www.itgovernance.co.uk It is a requirement for data controllers and data processors to implement a level of security appropriate to the risk. This includes Security measures taken need to comply with the concept of privacy by design. – Pseudonymisation and encryption of personal data – Measures to ensure the ongoing confidentiality, integrity and availability of systems – A process for regularly testing, assessing and evaluating the effectiveness of security measures Copyright IT Governance Ltd 2017 – v1.0
20 . TM Cyber-security assurance www.itgovernance.co.uk • A GDPR requirement – data controllers must implement “appropriate technical and organisational measures to ensure and to be able to demonstrate that the processing is performed in accordance with this Regulation”. – Must include appropriate data protection policies – Local authorities may use adherence to approved codes of conduct or management system certifications “as an element by which to demonstrate compliance with their obligations” – ICO and BSI are both developing new GDPR-focused standards • ISO 27001 already meets the “appropriate technical and organisational measures” requirement • BS 10012 was developed specifically for the GDPR – It provides assurance to the board that data security is being managed in accordance with the Regulation – It helps manage all information assets and all information security within the organisation – protecting against all threats Copyright IT Governance Ltd 2017 – v1.0
21 . TM Nine Steps to GDPR compliance in the Local Government www.itgovernance.co.uk STEP 1: Establish governance framework • board awareness • risk register • accountability framework • review STEP 2: Appoint and/or train a DPO/SDPO STEP 3: Data inventory • identify processors • identify unlawfully held data STEP 4: Conduct data flow audit Copyright IT Governance Ltd 2017 – v1.0
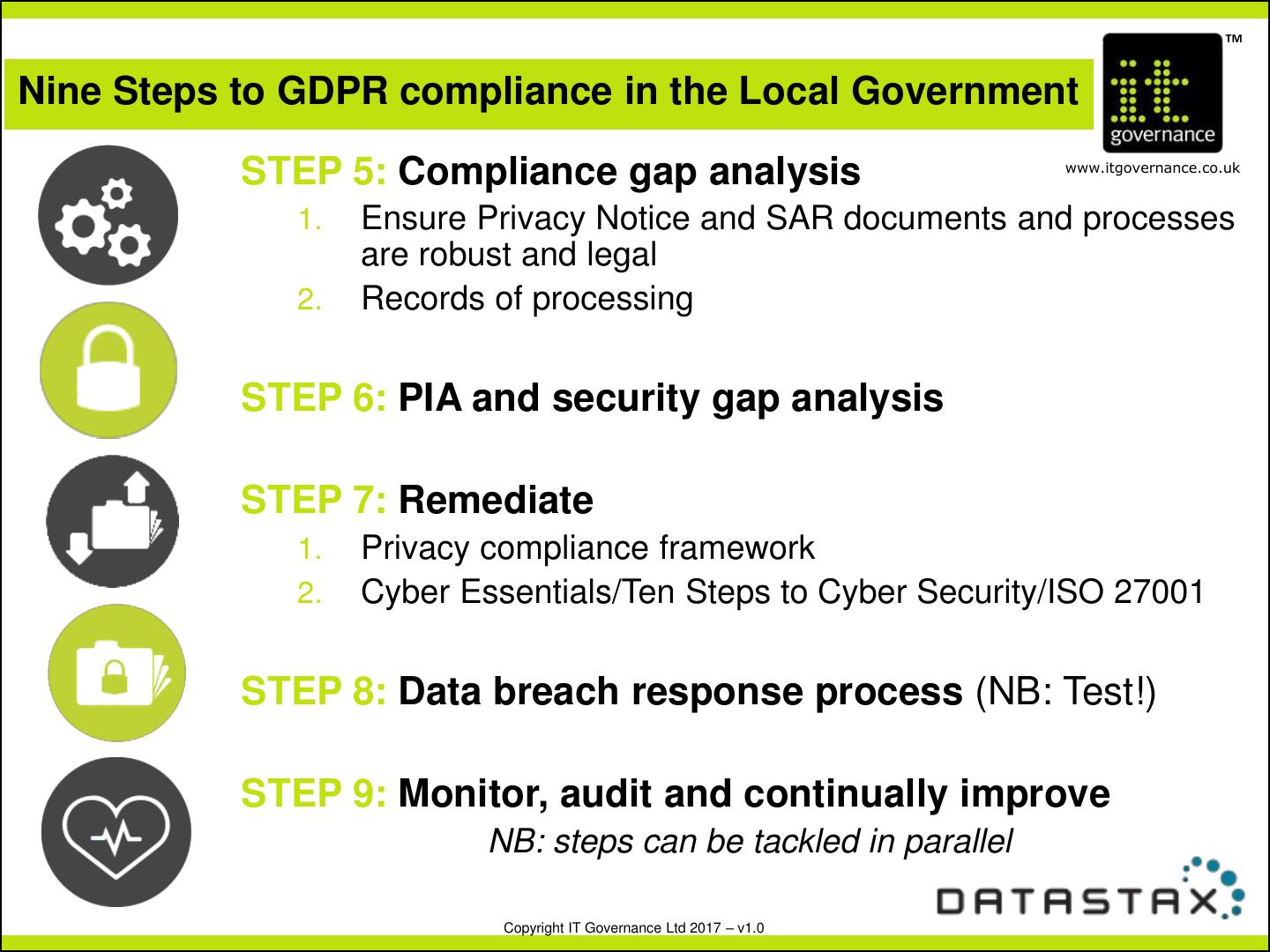
22 . TM Nine Steps to GDPR compliance in the Local Government STEP 5: Compliance gap analysis www.itgovernance.co.uk 1. Ensure Privacy Notice and SAR documents and processes are robust and legal 2. Records of processing STEP 6: PIA and security gap analysis STEP 7: Remediate 1. Privacy compliance framework 2. Cyber Essentials/Ten Steps to Cyber Security/ISO 27001 STEP 8: Data breach response process (NB: Test!) STEP 9: Monitor, audit and continually improve NB: steps can be tackled in parallel Copyright IT Governance Ltd 2017 – v1.0
23 .GDPR: The Catalyst for Customer 360 Tim Vincent EMEA Solution Engineering Manager timothy.vincent@datastax.com
24 . Do you have a Single View of your Customer? Article 20 - How do you present a Data Subject with a view of the data you hold on them? Article 17 - Right to Erasure or Right to be Forgotten, how do you locate all data on a Subject? 24 © DataStax, All Rights Reserved.
25 . Data Exists in Silos House Mortgage Bank Account Life Cover Insurance 25 © DataStax, All Rights Reserved.
26 . MDM is NOT the Answer MDM • Provides a single source of customer record, a golden record • MDM is not a data integration tool https://tinyurl.com/forrester-mdm • A static customer profile view with structured, limited data However, to achieve GDPR data subject access and right to erasure in the digital era, you need a data platform beyond MDM that: • Integrates MDM and other data sources, including real time customer activity data • Delivers contextual customer view in real-time • Operationalizes customer data for instant insights and actions • Guarantees 100% uptime • Allows global data access Customer Reporting Master Analytics C360 Discovery 3rd party data 26
27 . Not Only a Single Customer View Now a Customer 360 View A contextual, Real-time Guaranteed Always-on, connected, customer global access undisrupted single view of information and customer the customer responsiveness experience 27
28 . Now you can so so much more Real-Time Personalization View and manage the data access controls for Data Subjects. Drive engagement by guaranteeing crucial feedback, a tailored experience, and instantly actionable insight. 28 © DataStax, All Rights Reserved.
29 . C360 Application Characteristics Contextual Always-On Real-Time Distributed Scalable 29