- 快召唤伙伴们来围观吧
- 微博 QQ QQ空间 贴吧
- 文档嵌入链接
- 复制
- 微信扫一扫分享
- 已成功复制到剪贴板
Aligning GDPR Requirements with Today’s Hybrid Cloud Realities
展开查看详情
1 . Aligning GDPR Requirements with Today’s Hybrid Cloud Realities Presented by: Bob Brady, Business Value Consulting, DataStax Mark Royle, Solutions and Partner Marketing, Thales eSecurity September 20, 2018 1 © DataStax, All Rights Reserved.
2 . Key Points to Take Away: • GDPR is Real – and It’s the New Normal The Four Things • Hybrid-Cloud and Multi-Cloud are Real – and To Remember from this Webinar They Are Becoming the New Normal • You Cannot Buy a GDPR “Point Solution” • Partnerships Matter: – Data Platform – Data Security Services 2 © DataStax, All Rights Reserved.
3 . Contents 1 Introduction to DataStax 2 Overview of Hybrid Cloud and Multi Cloud 3 GDPR At-a-Glance 4 GDPR Security Requirements 5 Introduction to Thales eSecurity 6 The Seven Key Security Capabilities for GDPR 7 How Thales & DataStax Can Help 8 Questions? 3
4 . Introduction to DataStax For Techies: • DataStax powers the Right-Now Enterprise with the always-on, distributed cloud database built on Apache Cassandra and designed for hybrid cloud. For Non-Techies: • DataStax is the next-generation database technology, conceived and developed over the past ten years to meet the data & analytics needs that are unique to our time: o The need to handle massive volumes, speeds and varieties of data… o To apply state-of-the-art analytical techniques… o To do all of this instantaneously, securely and globally… o Running inside an on-premises data center, in the cloud, or potentially both… o Without ever going out of service for planned or unplanned maintenance 4 © DataStax, All Rights Reserved.
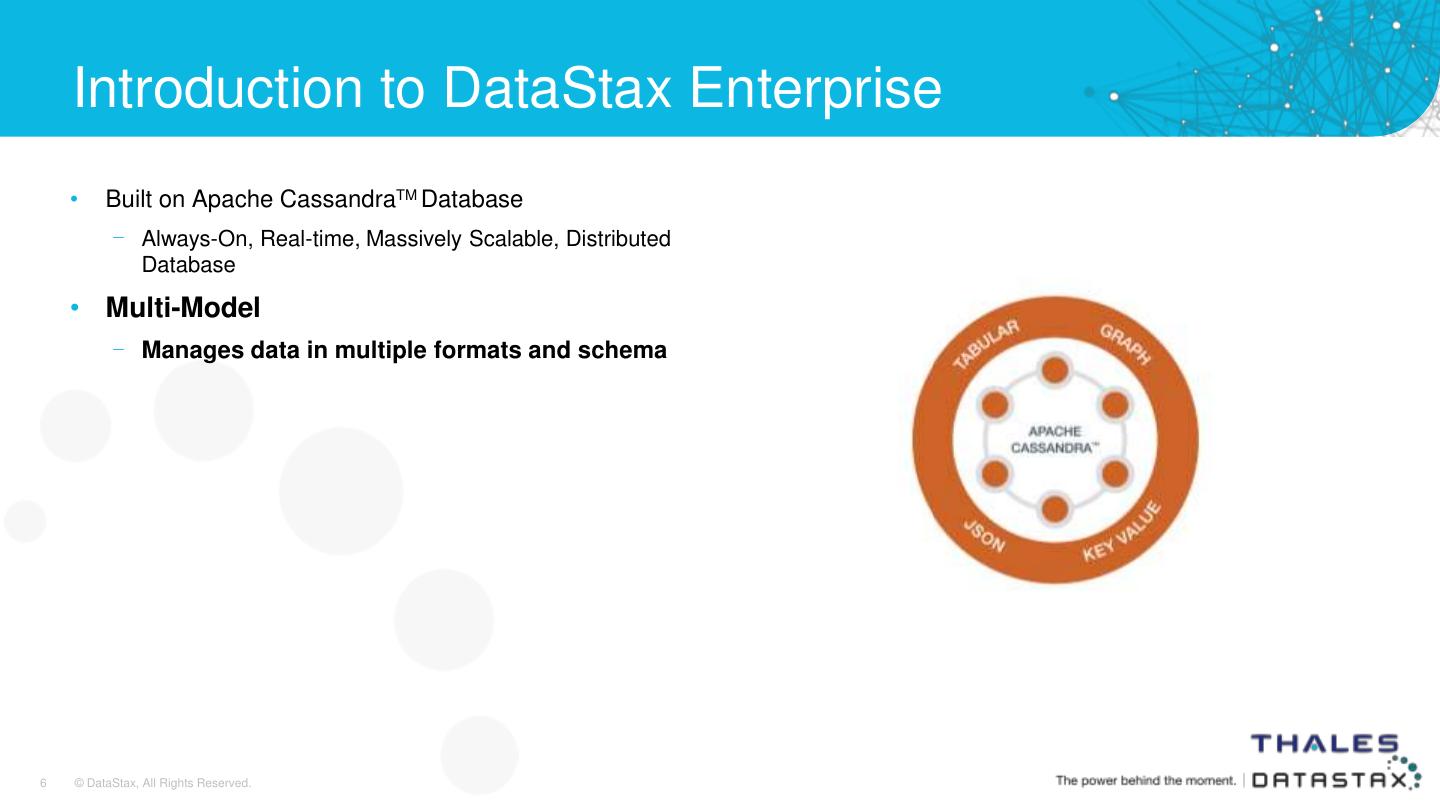
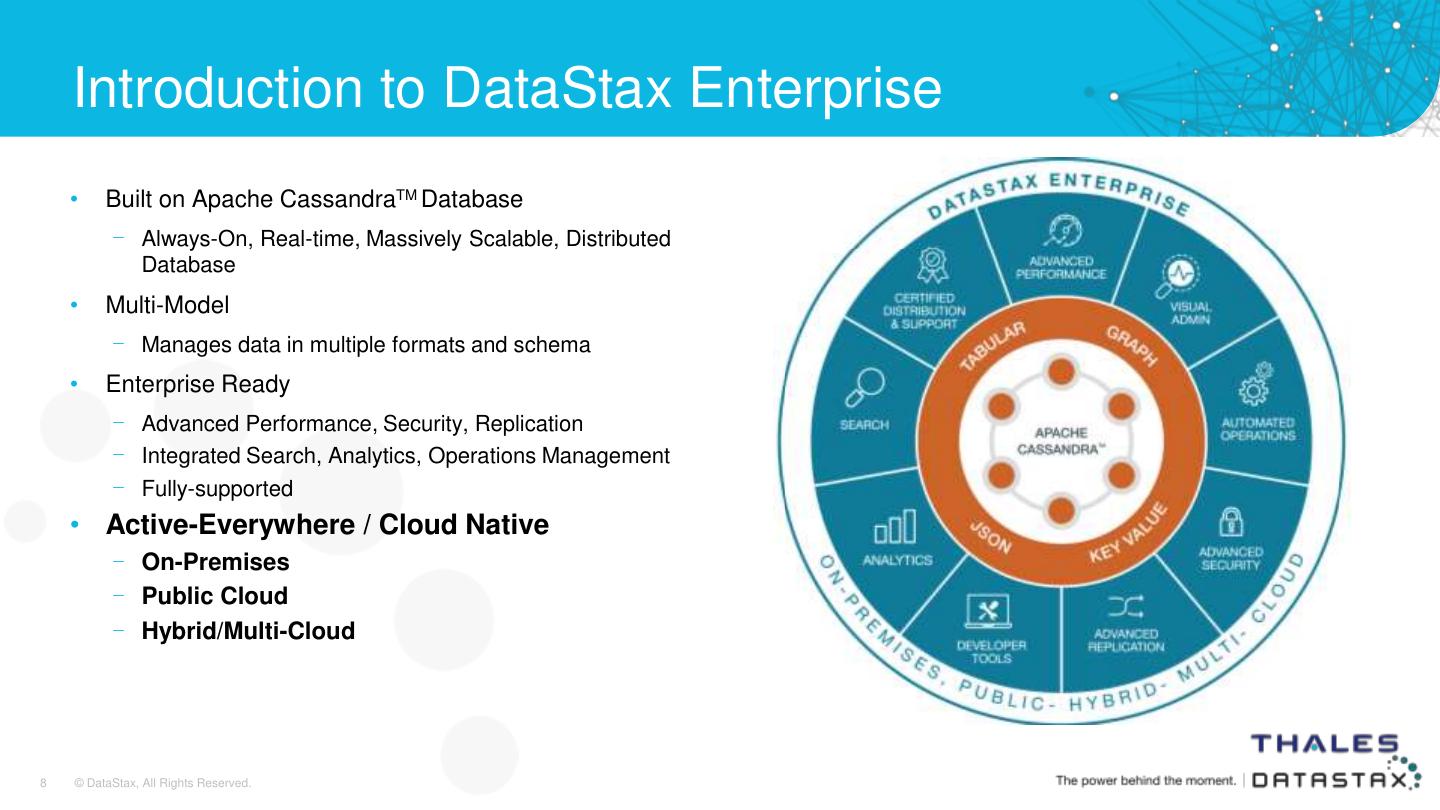
5 . Introduction to DataStax Enterprise • Built on Apache CassandraTM Database – Always-On, Real-time, Massively Scalable, Distributed Database 5 © DataStax, All Rights Reserved.
6 . Introduction to DataStax Enterprise • Built on Apache CassandraTM Database – Always-On, Real-time, Massively Scalable, Distributed Database • Multi-Model – Manages data in multiple formats and schema 6 © DataStax, All Rights Reserved.
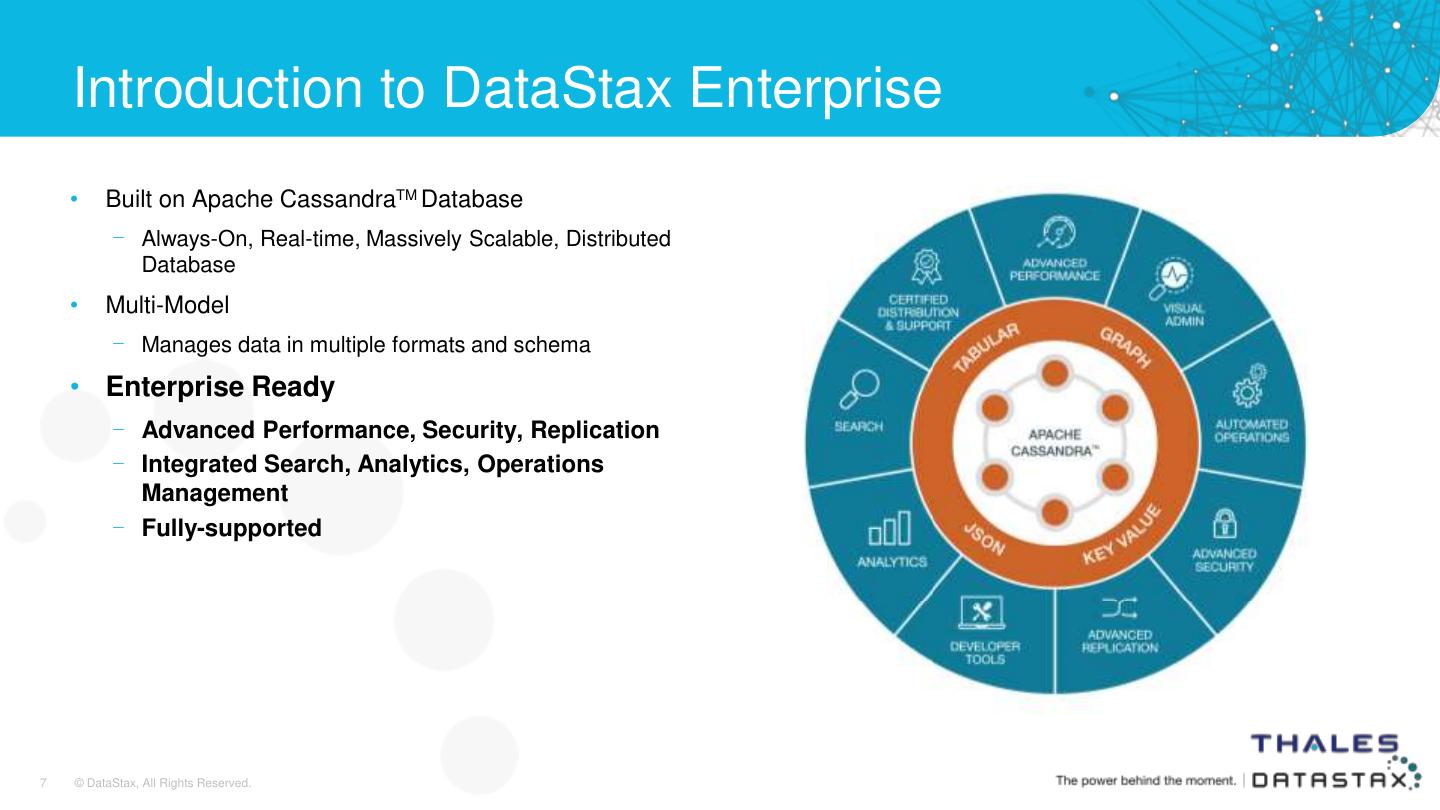
7 . Introduction to DataStax Enterprise • Built on Apache CassandraTM Database – Always-On, Real-time, Massively Scalable, Distributed Database • Multi-Model – Manages data in multiple formats and schema • Enterprise Ready – Advanced Performance, Security, Replication – Integrated Search, Analytics, Operations Management – Fully-supported 7 © DataStax, All Rights Reserved.
8 . Introduction to DataStax Enterprise • Built on Apache CassandraTM Database – Always-On, Real-time, Massively Scalable, Distributed Database • Multi-Model – Manages data in multiple formats and schema • Enterprise Ready – Advanced Performance, Security, Replication – Integrated Search, Analytics, Operations Management – Fully-supported • Active-Everywhere / Cloud Native – On-Premises – Public Cloud – Hybrid/Multi-Cloud 8 © DataStax, All Rights Reserved.
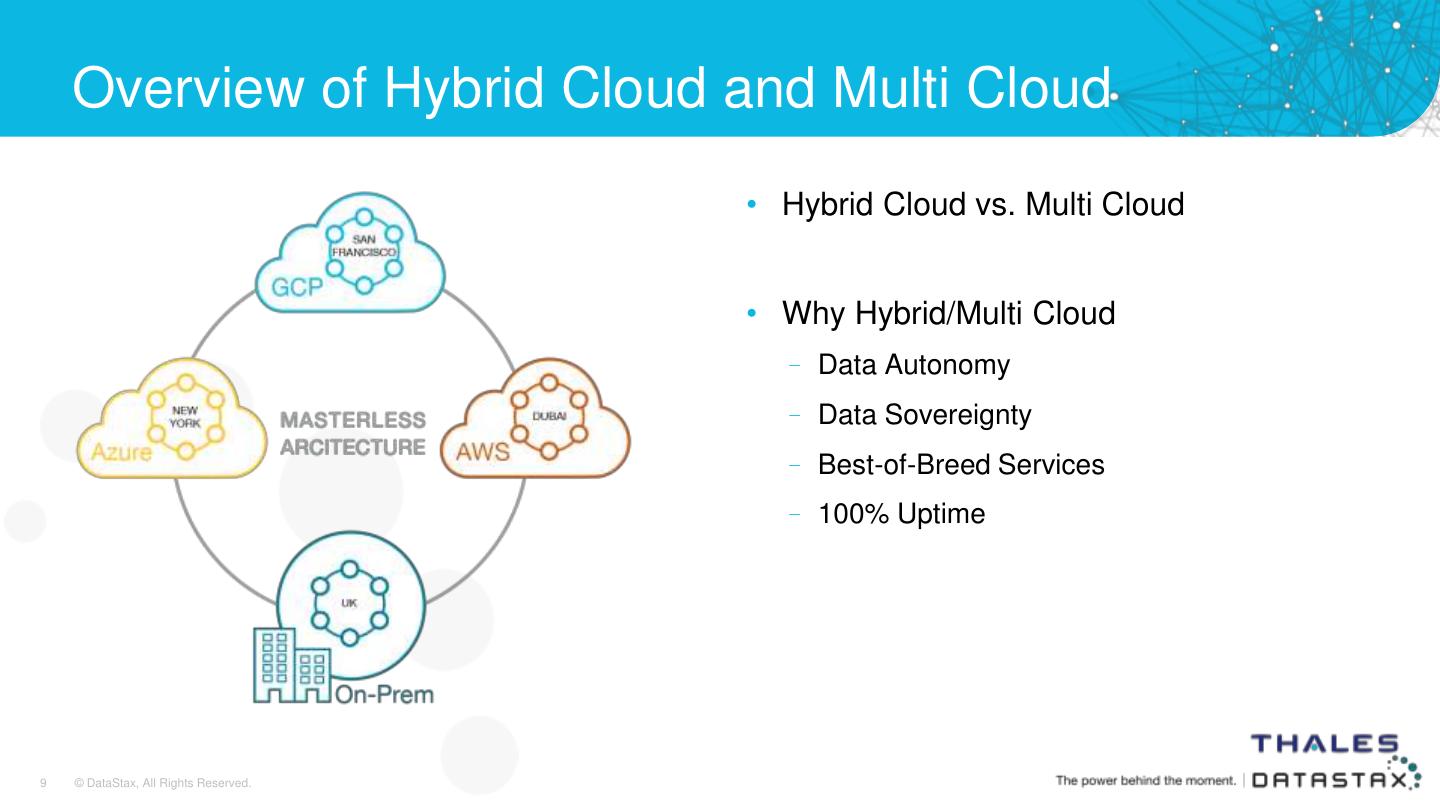
9 . Overview of Hybrid Cloud and Multi Cloud • Hybrid Cloud vs. Multi Cloud • Why Hybrid/Multi Cloud – Data Autonomy – Data Sovereignty – Best-of-Breed Services – 100% Uptime 9 © DataStax, All Rights Reserved.
10 . GDPR At-A-Glance • The General Data Protection Regulation (GDPR) was instituted by the European Union in an attempt to give consumers/citizens “ownership” of their personal data. • Went into full effect on May 25, 2018 • Affects any company that conducts business within the EU – including US multinational companies • Replaces/Supersedes multiple other country-specific privacy rules which were hellacious to manage. • The only thing more burdensome than one big regulation is a bunch of little ones that conflict with each other. 10 © DataStax, All Rights Reserved.
11 . Key Tenets of GDPR • “Affirmative Permission” required to collect personal data • Data must physically reside where the customer lives • Data must be “portable” from one company to another • Customer has the “right to be forgotten” • Penalties for non-compliance can be Enormous (“Dissuasive”) • Data Security is Paramount 11 © DataStax, All Rights Reserved.
12 . Data Security Requirements for GDPR 1. Internal & External Authentication 2. Fine-grained Access Control 3. Encryption for Data In Transit and At Rest 4. Strong Key Management 5. Auditing and Central Visibility across Disparate Environments 6. Simplified Data Deletion 7. Data Autonomy and Data Sovereignty 12 © DataStax, All Rights Reserved.
13 . Introduction to Thales eSecurity Mark Royle www.thales-esecurity.com
14 . Contents 1 Introduction to DataStax 2 Overview of Hybrid Cloud and Multi Cloud 3 GDPR At-a-Glance 4 GDPR Security Requirements 5 Introduction to Thales eSecurity 6 The Seven Key Security Capabilities for GDPR 7 How Thales & DataStax Can Help 8 Questions? 14
15 . Thales Group – global leadership N°1 worldwide Payloads Air traffic management Sonars Security for interbank for telecom satellites transactions N°2 €15 worldwide Rail signalling systems In-flight entertainment Military tactical and connectivity radiocommunications N°3 billion worldwide in revenues Commercial avionics Civil satellites Military surface radars 15 © DataStax, All Rights Reserved.
16 . Thales eSecurity – world leader in data protection Years of securing the Protection of the 40+ world’s most sensitive data 9 Customers of Fortune 10 80% world’s POS transactions Deep expertise and track record in applied cryptography 19 Security for largest banks of the 20 130+ Partnerships with leading technology providers of cloud computing, digital payments and more Long-standing history of industry certifications and Security for4 of the energy companies 5 largest validation 16 © DataStax, All Rights Reserved.
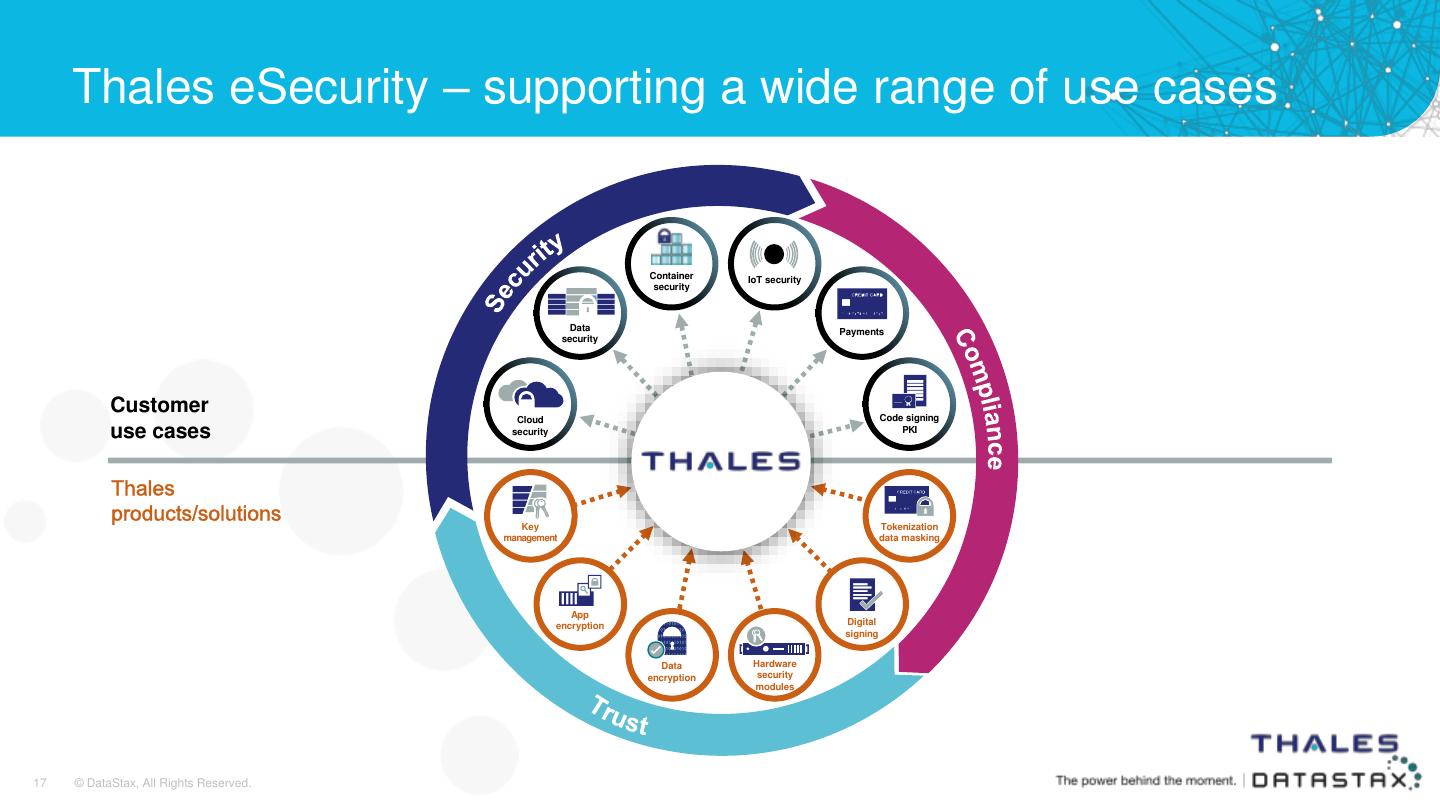
17 . Thales eSecurity – supporting a wide range of use cases Container IoT security security Data Payments security Customer Code signing Cloud use cases security PKI Key Tokenization management data masking App encryption Digital signing Data Hardware encryption security modules 17 © DataStax, All Rights Reserved.
18 . Data Security Requirements for GDPR 1. Internal & External Authentication 2. Fine-grained Access Control 3. Encryption for Data In Transit and At Rest 4. Strong Key Management 5. Auditing and Central Visibility across Disparate Environments 6. Simplified Data Deletion 7. Data Autonomy and Data Sovereignty 18 © DataStax, All Rights Reserved.
19 . #1: Internal/External Authentication • Employees, 3rd party contractors, partners, customers • Supporting a range of protocols • Preserving a positive user experience • Supporting Multiple environments: on-premise, cloud, and hybrid environments 19 © DataStax, All Rights Reserved.
20 . #2: Fine-grained Access Control • Granular access controls, applied uniformly across multiple clouds and data centers • Policies applied down to individual rows of data • Multi-tenant environments, such as public cloud implementations, require strong, persistent controls for user and administrator access to specific data sets 20 © DataStax, All Rights Reserved.
21 . #3: Encryption for Data In Transit and At Rest • Flexible • Mix of mechanisms/levels • Tokenization as an option • Minimize application changes 21 © DataStax, All Rights Reserved.
22 . #4: Strong Key Management • Keys stored compliant with FIPS and Common Criteria • Supports multitude of environments, and BYOK • Supports data mobility 22 © DataStax, All Rights Reserved.
23 . #5: Auditing and Central Visibility Across Disparate Environments • Application-level auditing • Security auditing • Unified view of customer’s data 23 © DataStax, All Rights Reserved.
24 . #6: Simplified Data Management • Customer’s “right-to-be-forgotten” • Efficiently control and schedule removal of data • Central key management • “Time to live” records management 24 © DataStax, All Rights Reserved.
25 . #7: Data Autonomy & Data Sovereignty • Collecting organizations responsible for their data • Establish controls at the schema level • Support multi-cloud and data center environments 25 © DataStax, All Rights Reserved.
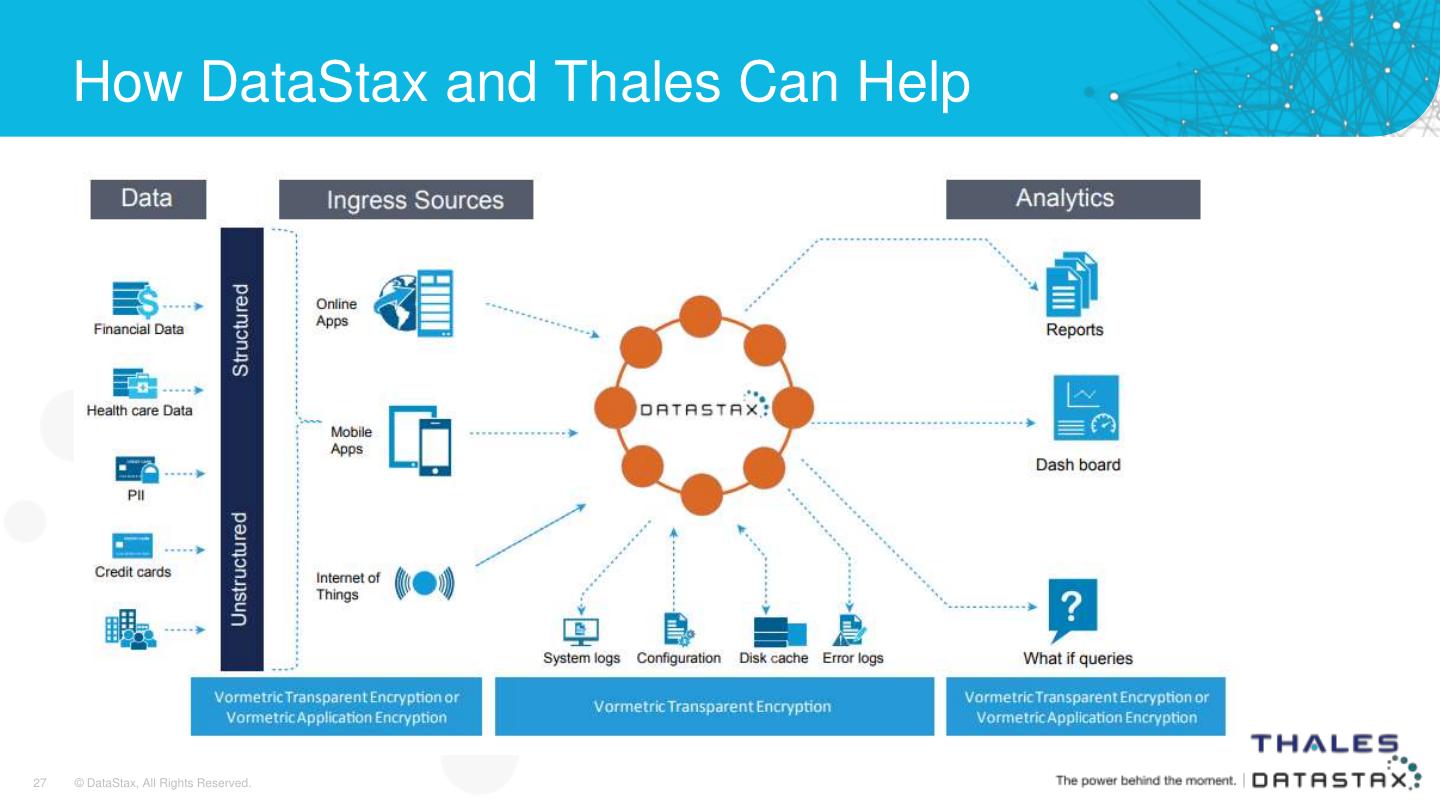
26 . How DataStax and Thales Can Help • Granular Access Controls • Robust Authentication • Advanced Encryption • Audit and Logging Features • Unified Visibility / Customer 360 • Schema Level Controls – Data Sovereignty • Consulting Expertise 26 © DataStax, All Rights Reserved.
27 . How DataStax and Thales Can Help 27 © DataStax, All Rights Reserved.
28 . Key Points to Take Away: • GDPR is Real – and It’s the New Normal The Four Things • Hybrid-Cloud and Multi-Cloud are Real – and To Remember from this Webinar They Are Becoming the New Normal • You Cannot Buy a GDPR “Point Solution” • Partnerships Matter: – Data Platform – Data Security Services 28 © DataStax, All Rights Reserved.
29 . Additional Resources & Key Contacts Additional Resources Aligning GDPR Requirements with Today’s Hybrid Cloud Realities Seven Requirements for Compliance The EU GDPR Pocket Guide Written by Alan Calder, published by DataStax DigitalRights 360: How DataStax Helps Enterprises Comply with the GDPR, by Martin James http://www.dataarchitect.cloud/digitalrights-360-how-datastax-helps- enterprises-comply-with-the-gdpr/ Key Contacts Bob.Brady@DataStax.com Mark.Royle@ThaleseSecurity.com 29 © DataStax, All Rights Reserved.