- 快召唤伙伴们来围观吧
- 微博 QQ QQ空间 贴吧
- 文档嵌入链接
- 复制
- 微信扫一扫分享
- 已成功复制到剪贴板
13computer and network security---Internet Security
展开查看详情
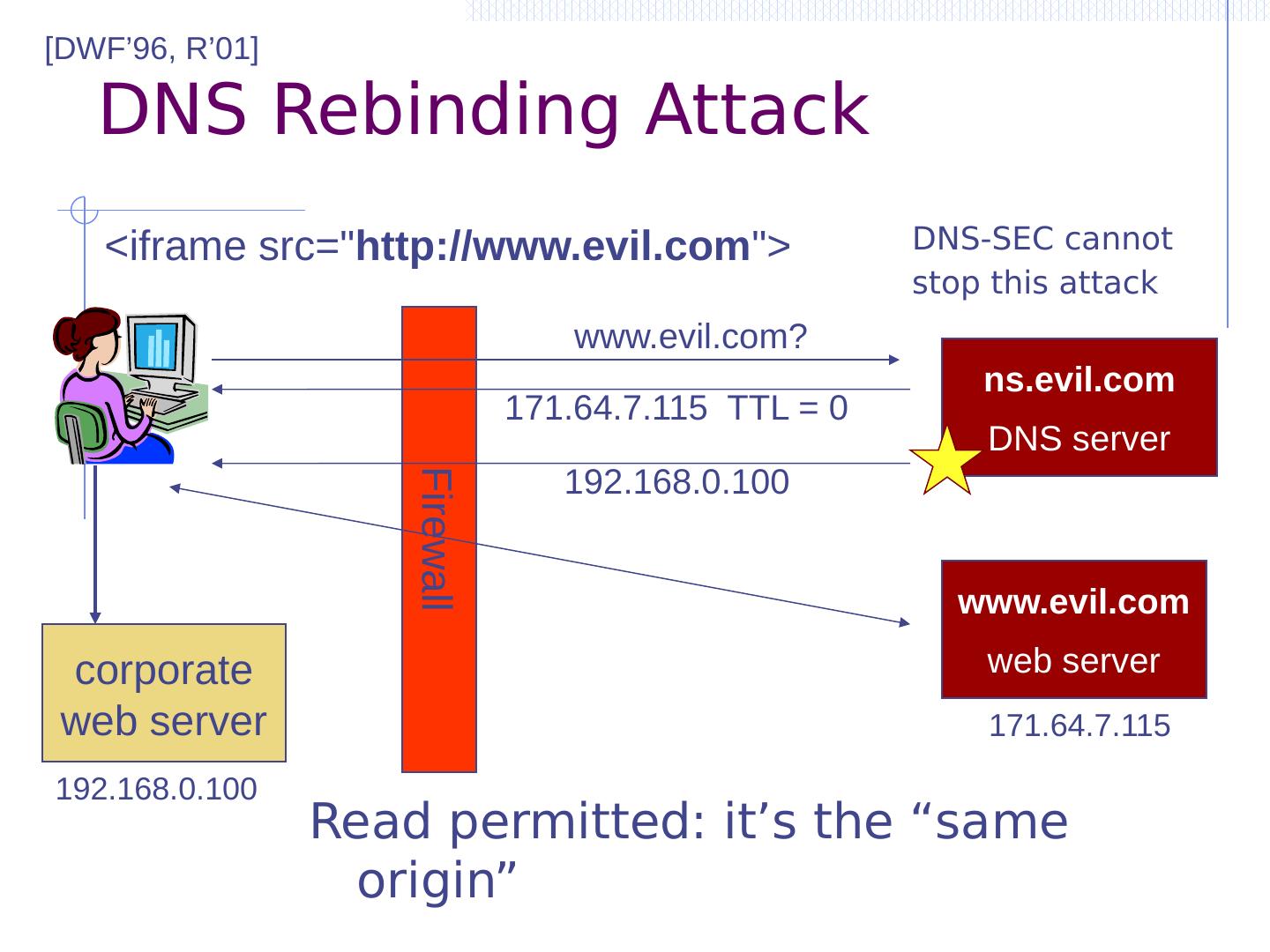
1 .Internet Security: How the Internet works and some basic vulnerabilities Dan Boneh CS 155
2 .Backbone ISP ISP Internet Infrastructure Local and interdomain routing TCP/IP for routing and messaging BGP for routing announcements Domain Name System Find IP address from symbolic name ( www.cs.stanford.edu )
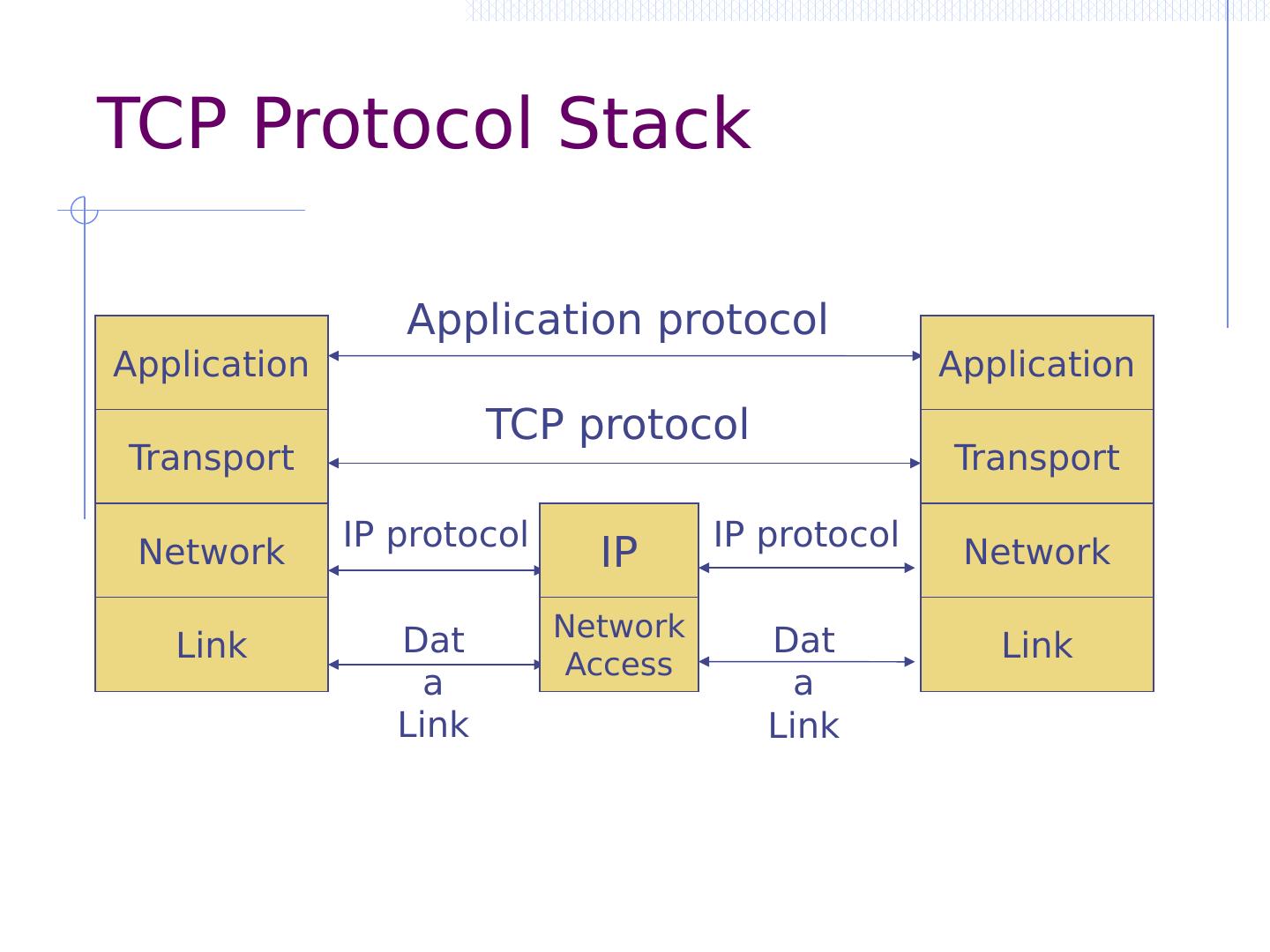
3 .TCP Protocol Stack Application Transport Network Link Application protocol TCP protocol IP protocol Data Link IP Network Access IP protocol Data Link Application Transport Network Link
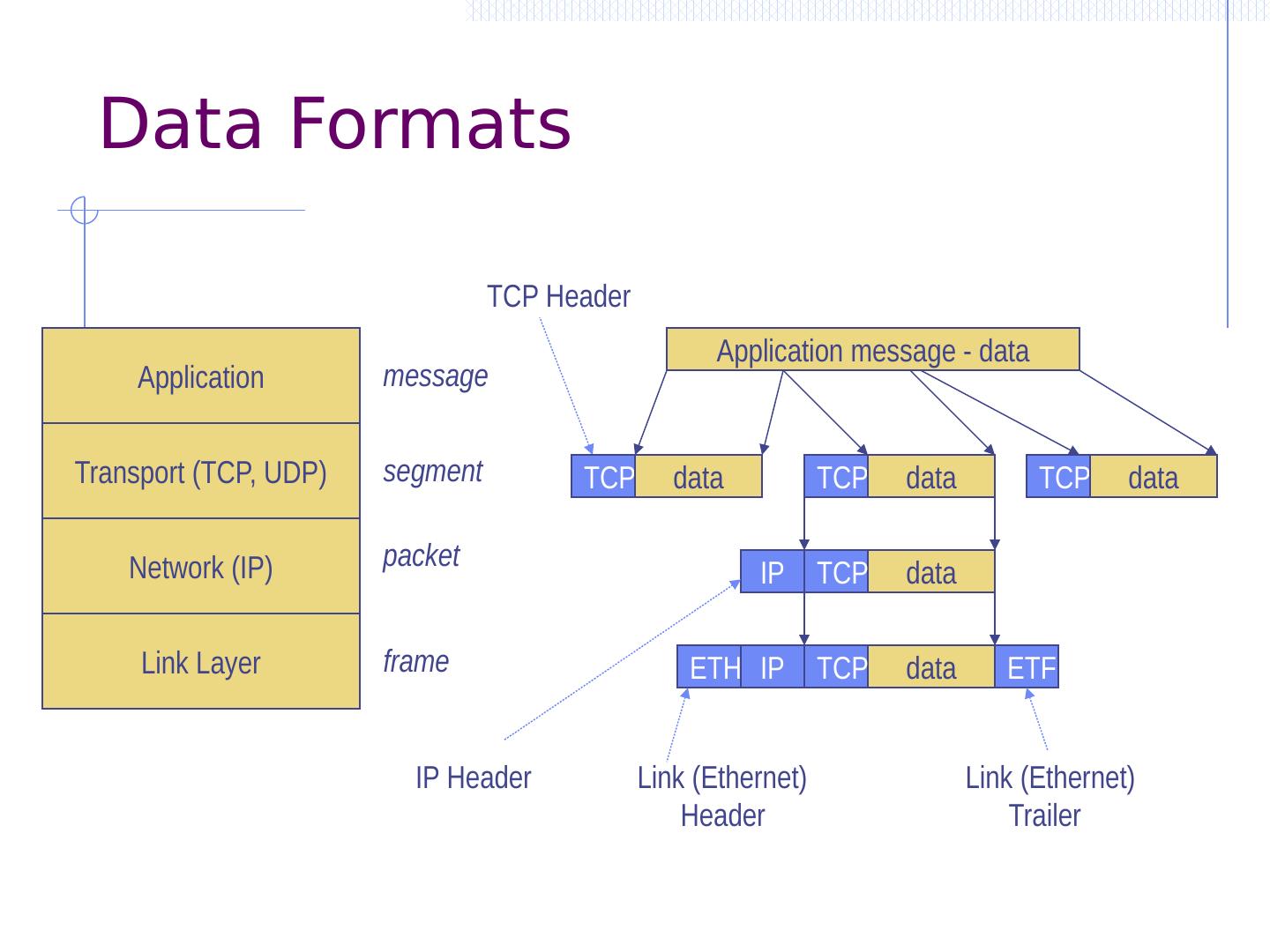
4 .Data Formats Application Transport (TCP, UDP) Network (IP) Link Layer Application message - data TCP data TCP data TCP data TCP Header data TCP IP IP Header data TCP IP ETH ETF Link (Ethernet) Header Link (Ethernet) Trailer segment packet frame message
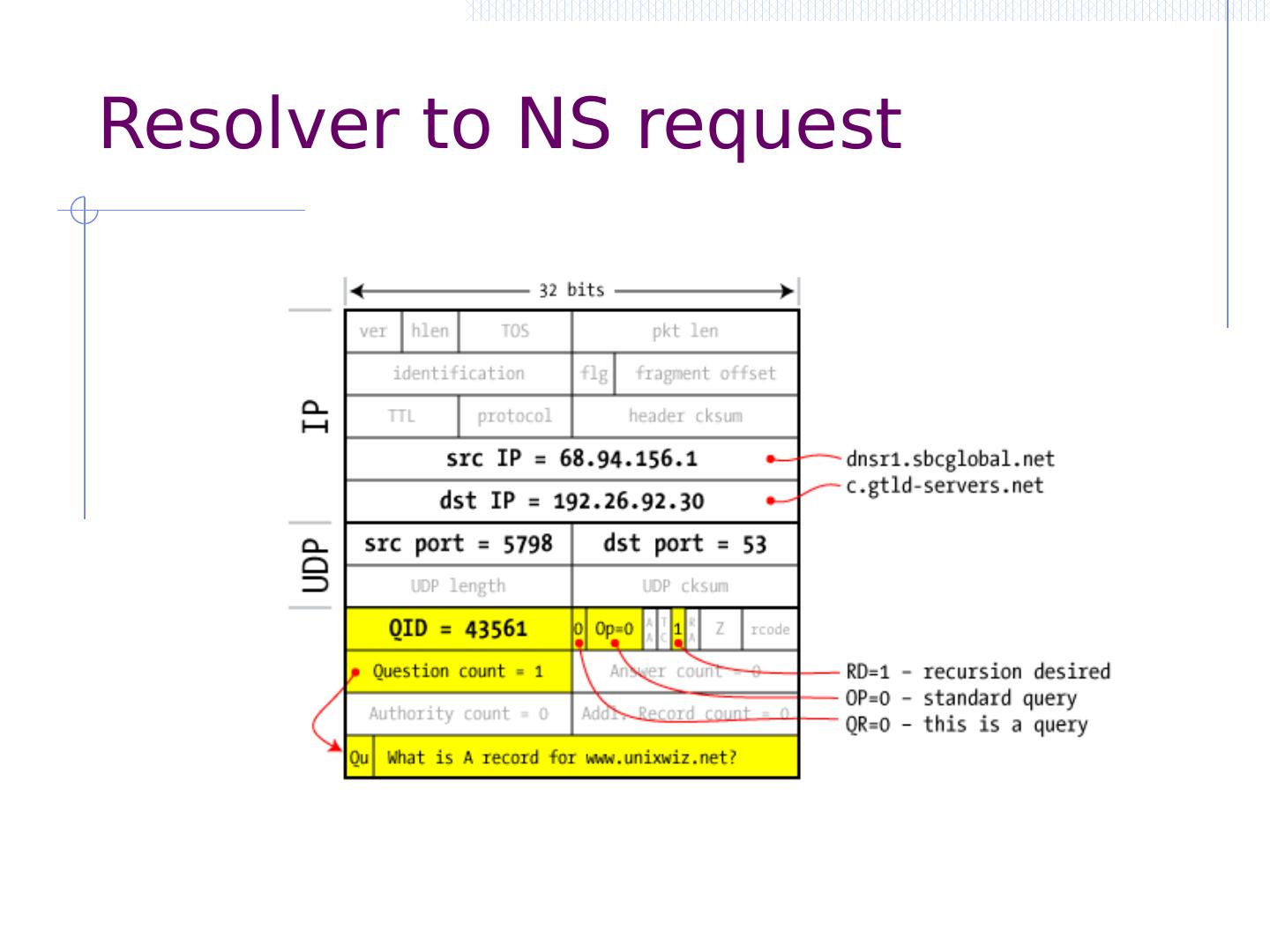
5 .Internet Protocol Connectionless Unreliable Best effort Notes: src and dest ports not parts of IP hdr IP Version Header Length Type of Service Total Length Identification Flags Time to Live Protocol Header Checksum Source Address of Originating Host Destination Address of Target Host Options Padding IP Data Fragment Offset
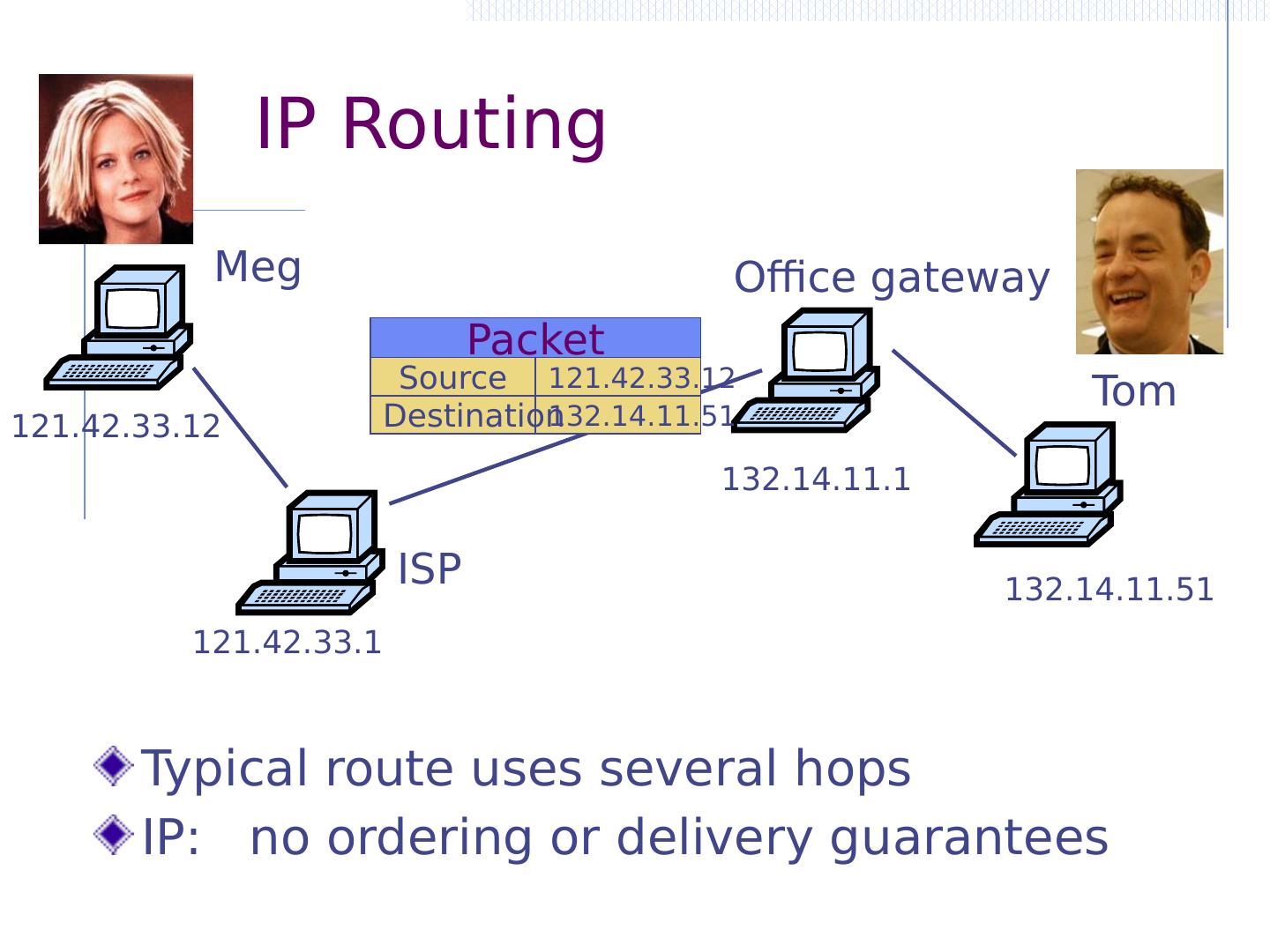
6 . IP Routing Typical route uses several hops IP: no ordering or delivery guarantees Meg Tom ISP Office gateway 121.42.33.12 132.14.11.51 Source Destination Packet 121.42.33.12 121.42.33.1 132.14.11.51 132.14.11.1
7 .IP Protocol Functions (Summary) Routing IP host knows location of router (gateway) IP gateway must know route to other networks Fragmentation and reassembly If max-packet-size less than the user-data-size Error reporting ICMP packet to source if packet is dropped TTL field: decremented after every hop Packet dropped if TTL=0. Prevents infinite loops .
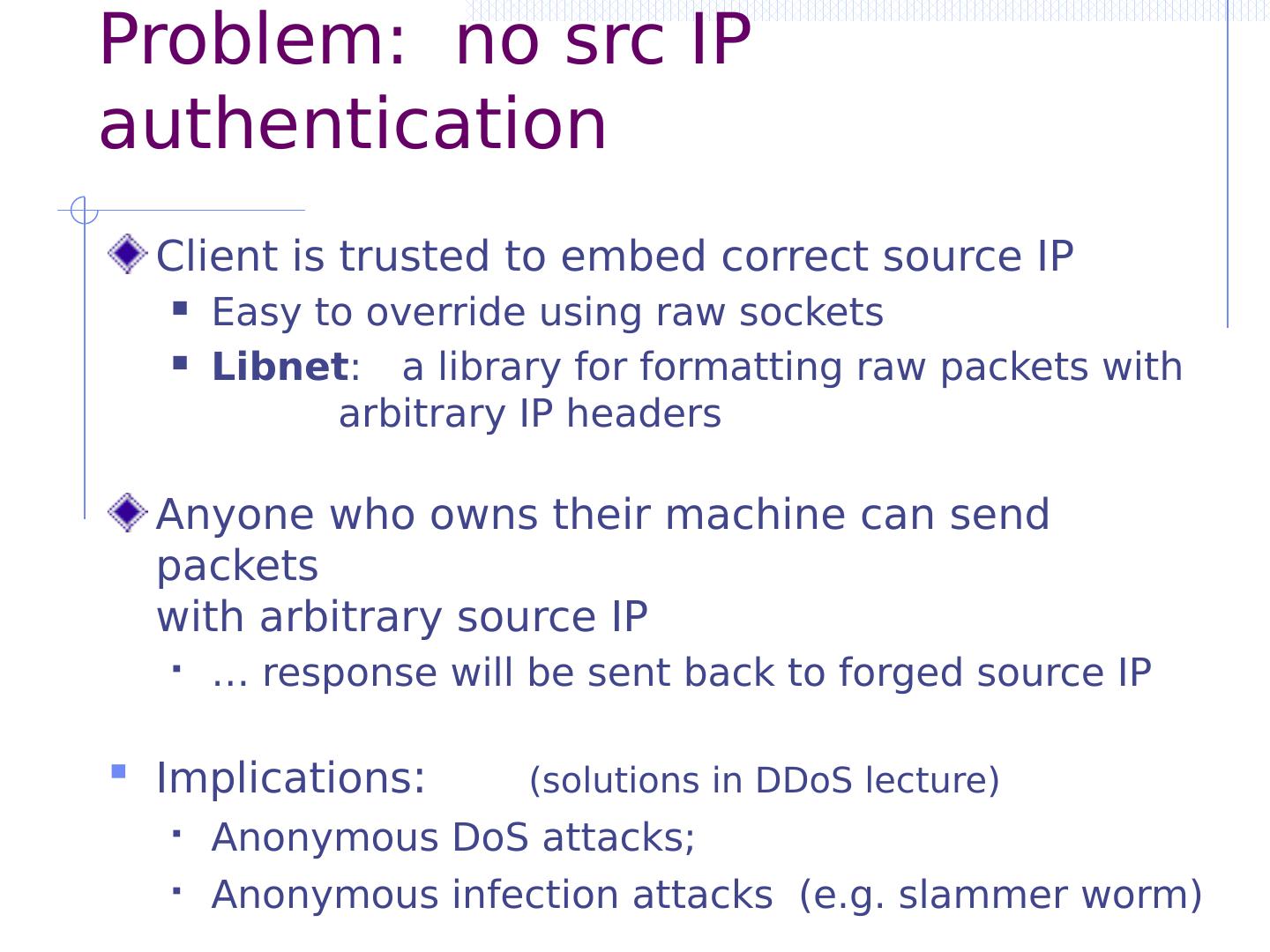
8 .Problem: no src IP authentication Client is trusted to embed correct source IP Easy to override using raw sockets Libnet : a library for formatting raw packets with arbitrary IP headers Anyone who owns their machine can send packets with arbitrary source IP … response will be sent back to forged source IP Implications : (solutions in DDoS lecture) Anonymous DoS attacks; Anonymous infection attacks (e.g. slammer worm)
9 .Transmission Control Protocol Connection-oriented, preserves order Sender Break data into packets Attach packet numbers Receiver Acknowledge receipt; lost packets are resent Reassemble packets in correct order TCP Book Mail each page Reassemble book 19 5 1 1 1
10 .TCP Header (protocol=6) Source Port Dest port SEQ Number ACK Number Other stuff U R G P S R A C K P S H S Y N F I N TCP Header
11 .Review: TCP Handshake C S SYN : SYN/ACK : ACK : Listening Store SN C , SN S Wait Established SN C ⟵ rand C AN C ⟵ 0 SN S ⟵ rand S AN S ⟵ SN C SN ⟵ SN C +1 AN ⟵ SN S Received packets with SN too far out of window are dropped
12 .Basic Security Problems 1. Network packets pass by untrusted hosts Eavesdropping, packet sniffing Especially easy when attacker controls a machine close to victim (e.g. WiFi routers) 2. TCP state easily obtained by eavesdropping Enables spoofing and session hijacking 3. Denial of Service ( DoS ) vulnerabilities DDoS lecture
13 .Why random initial sequence numbers? Suppose initial seq. numbers ( SN C , SN S ) are predictable: Attacker can create TCP session on behalf of forged source IP Breaks IP-based authentication (e.g. SPF, / etc /hosts ) R andom seq. num. do not prevent attack, but make it harder Victim Server SYN/ACK dstIP=victim SN=server SN S ACK srcIP=victim AN=predicted SN S command server thinks command is from victim IP addr attacker TCP SYN srcIP=victim
14 .Example DoS vulnerability: Reset Attacker sends a Reset packet to an open socket If correct SN S then connection will close ⇒ DoS Naively , success prob. is 1/2 32 (32-bit seq. # ’ s). … but, many systems allow for a large window of acceptable seq. # ‘ s. Much higher success probability. Attacker can flood with RST packets until one works M ost effective against long lived connections , e.g. BGP
15 .Routing Security ARP, OSPF, BGP
16 .Interdomain Routing connected group of one or more Internet Protocol prefixes under a single routing policy (aka domain) OSPF BGP Autonomous System earthlink.net Stanford.edu (AS#4355) (AS#32)
17 .Routing Protocols ARP ( addr resolution protocol): IP addr ⟶ eth addr Security issues: (local network attacks) Node A can confuse gateway into sending it traffic for Node B By proxying traffic, node A can read/inject packets into B ’ s session (e.g. WiFi networks) OSPF: used for routing within an AS BGP: routing between Autonomous Systems Security issues: unauthenticated route updates Anyone can cause entire Internet to send traffic for a victim IP to attacker’s address Example: Youtube -Pakistan mishap (see DDoS lecture ) Anyone can hijack route to victim (next slides)
18 .BGP example [ D. Wetherall ] 3 4 6 5 7 1 8 2 7 7 2 7 2 7 2 7 3 2 7 6 2 7 2 6 5 2 6 5 2 6 5 3 2 6 5 7 2 6 5 6 5 5 5
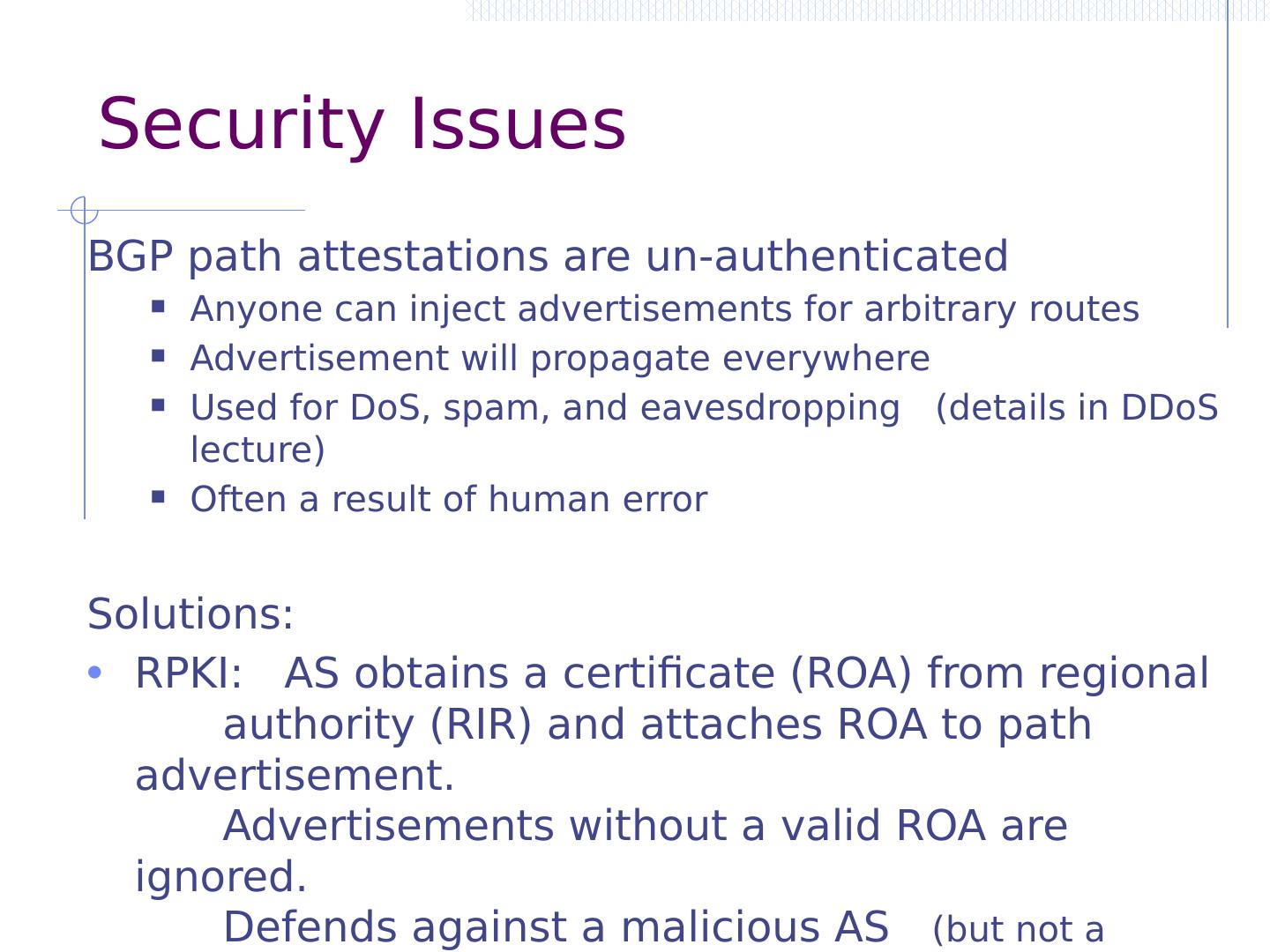
19 .Security Issues BGP path attestations are un-authenticated Anyone can inject advertisements for arbitrary routes Advertisement will propagate everywhere Used for DoS , spam, and eavesdropping (details in DDoS lecture) Often a result of human error Solutions: RPKI: AS obtains a certificate (ROA) from regional authority (RIR) and attaches ROA to path advertisement. Advertisements without a valid ROA are ignored. Defends against a malicious AS (but not a network attacker) SBGP: sign every hop of a path advertisement
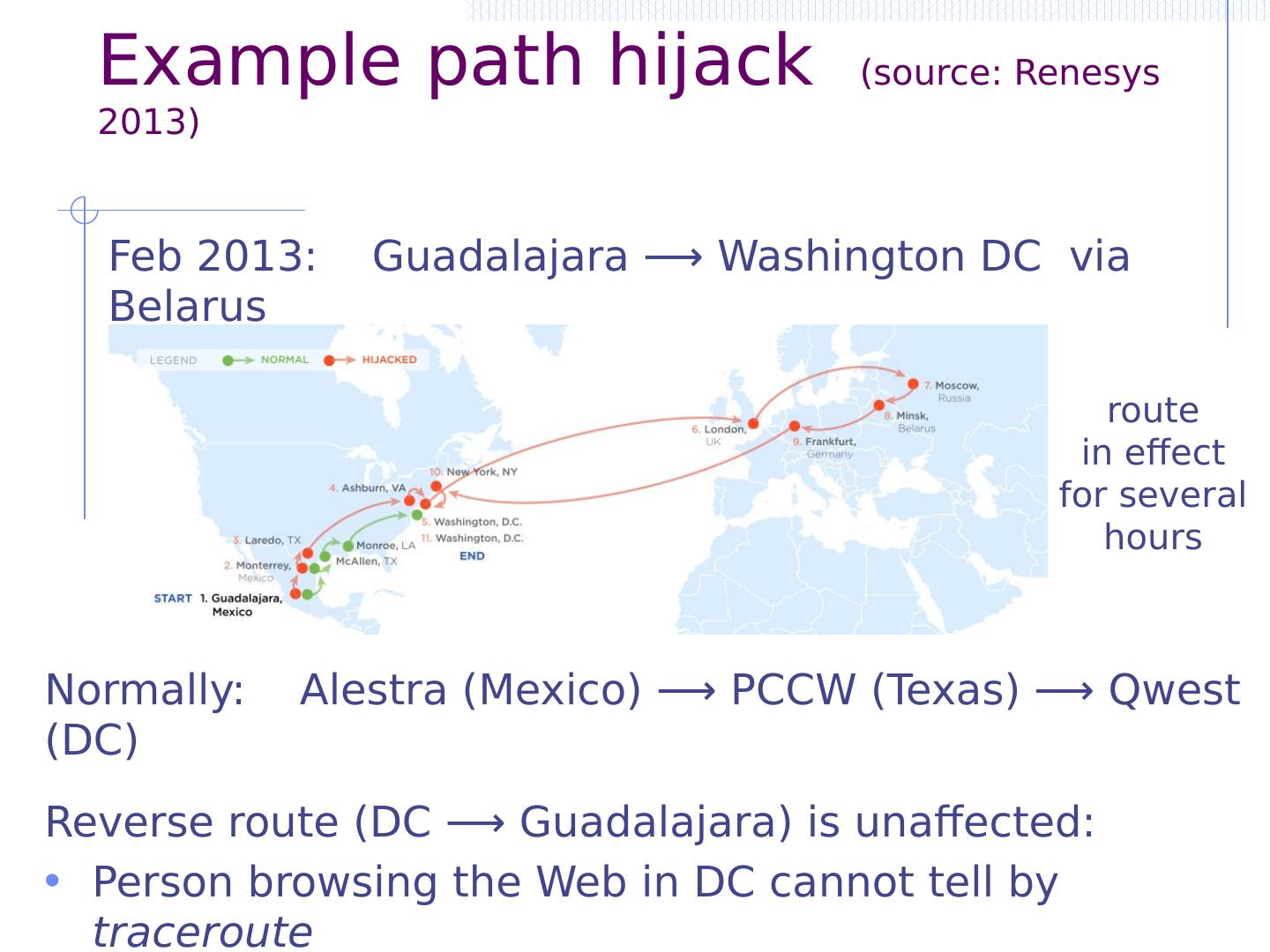
20 .Example path hijack (source: Renesys 2013) Feb 2013: Guadalajara ⟶ Washington DC via Belarus Normally: Alestra (Mexico) ⟶ PCCW (Texas) ⟶ Qwest (DC) Reverse route (DC ⟶ Guadalajara) is unaffected: Person browsing the Web in DC cannot tell by traceroute that HTTP responses are routed through Moscow r oute in effect f or several hours
21 .OSPF: routing inside an AS Link State Advertisements (LSA): Flooded throughout AS so that all routers in the AS have a complete view of the AS topology Transmission: IP datagrams, protocol = 89 Neighbor discovery: Routers dynamically discover direct neighbors on attached links --- sets up an “ adjacenty ” Once setup, they exchange their LSA databases
22 . Ra LSA DB : Rb Rb LSA R3 Ra Rb Net-1 Net-1 Ra LSA Ra Rb Net-1 3 2 2 3 1 1 1 Example: LSA from Ra and Rb
23 .Security features O SPF message integrity (unlike BGP) Every link can have its own shared secret Unfortunately, OSPF uses an insecure MAC: MAC( k,m ) = MD5(data ll key ll pad ll len ) Every LSA is flooded throughout the AS If a single malicious router, valid LSAs may still reach dest . The “fight back” mechanism If a router receives its own LSA with a newer timestamp than the latest it sent, it immediately floods a new LSA Links must be advertised by both ends
24 .Still some attacks possible [NKGB’12] Threat model: single malicious router wants to disrupt all AS traffic Example problem: adjacency setup need no peer feedback LAN Victim (DR) a remote attacker adjacency adjacency False Hello and DBD messages n et 1 phantom router adjacency Result: DoS on net 1
25 .Domain Name System
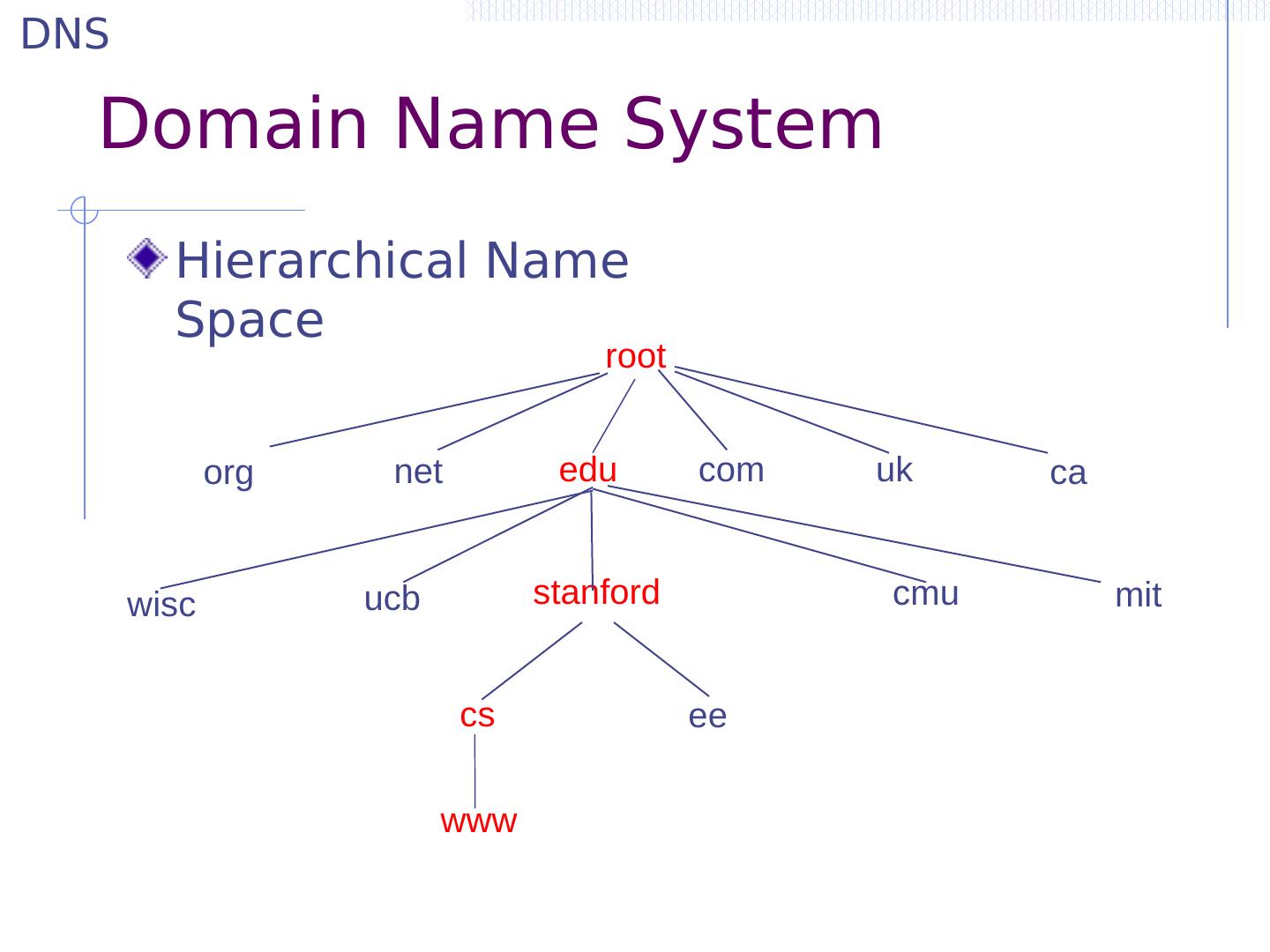
26 .Domain Name System Hierarchical Name Space root edu net org uk com ca wisc ucb stanford cmu mit cs ee www DNS
27 .DNS Root Name Servers Hierarchical service Root name servers for top-level domains Authoritative name servers for subdomains Local name resolvers contact authoritative servers when they do not know a name
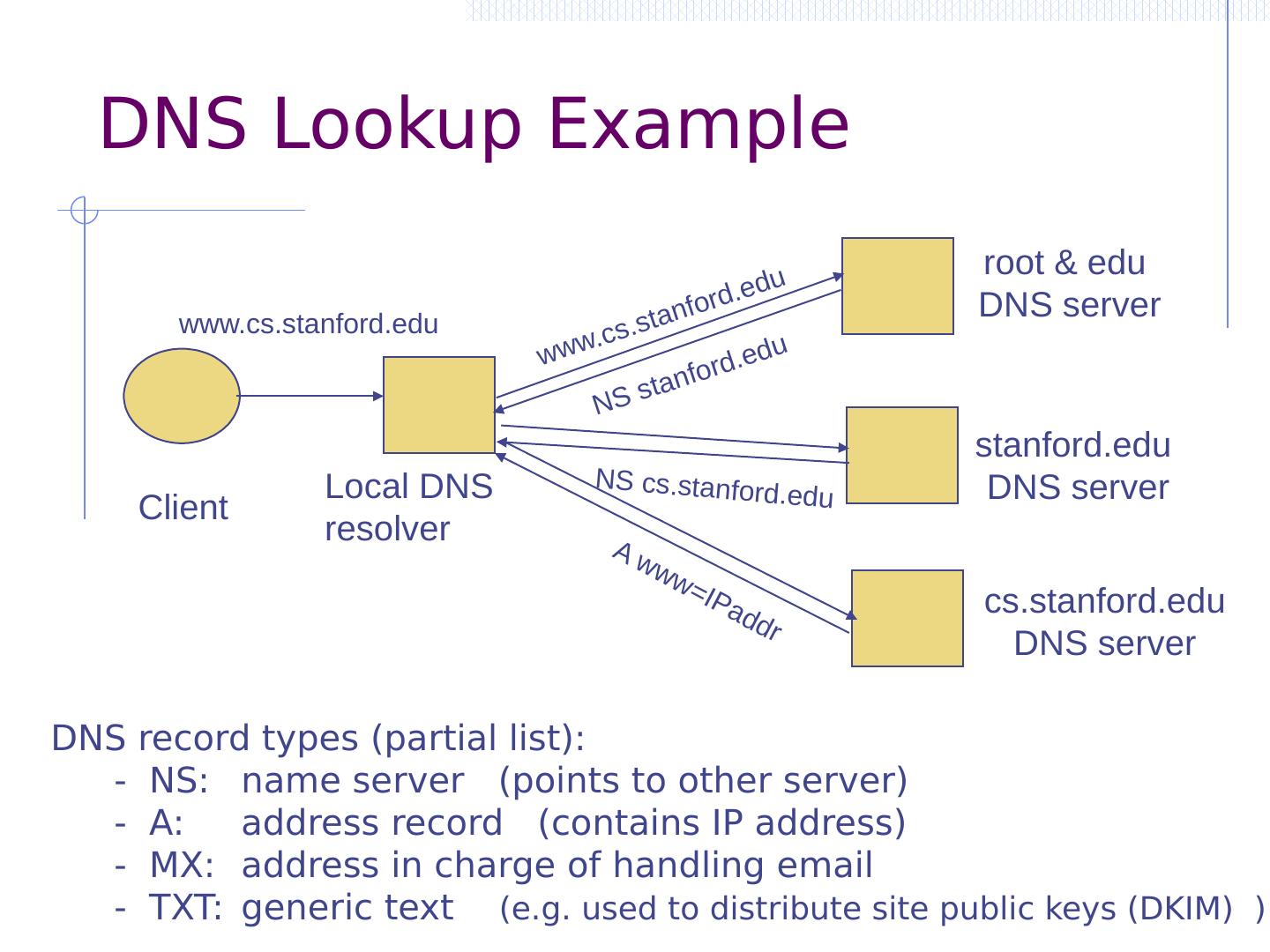
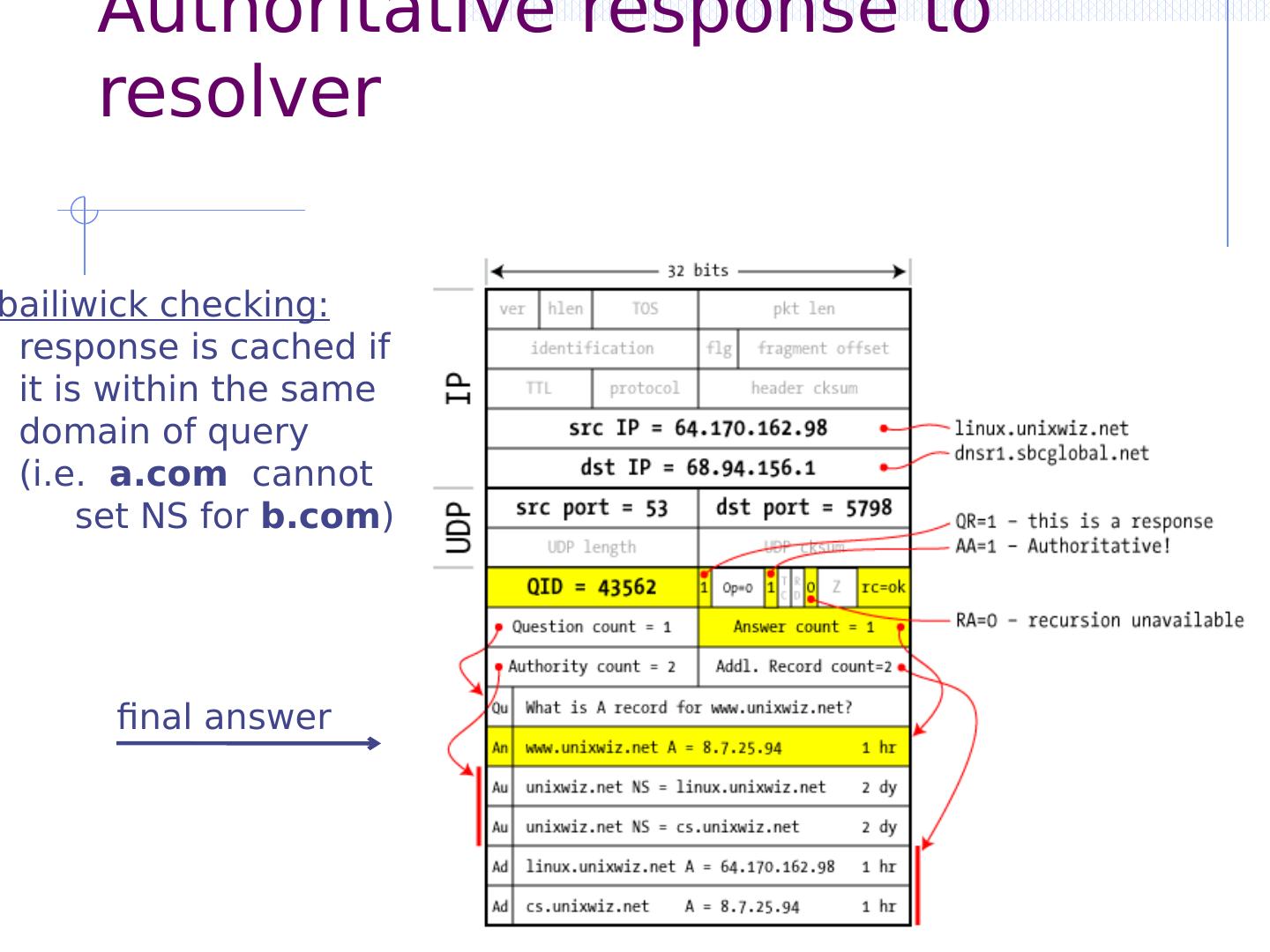
28 .DNS Lookup Example Client Local DNS resolver root & edu DNS server stanford.edu DNS server www.cs.stanford.edu NS stanford.edu www.cs.stanford.edu NS cs.stanford.edu A www=IPaddr cs.stanford.edu DNS server DNS record types (partial list): - NS: name server (points to other server) - A: address record (contains IP address) - MX: address in charge of handling email - TXT: generic text (e.g. used to distribute site public keys (DKIM) )
29 .Caching DNS responses are cached Quick response for repeated translations Note: NS records for domains also cached DNS negative queries are cached Save time for nonexistent sites, e.g. misspelling Cached data periodically times out Lifetime (TTL) of data controlled by owner of data TTL passed with every record