- 快召唤伙伴们来围观吧
- 微博 QQ QQ空间 贴吧
- 文档嵌入链接
- 复制
- 微信扫一扫分享
- 已成功复制到剪贴板
分布式系统:分布式共识问题
展开查看详情
1 .Distributed Consensus
2 . Distributed Consensus Reaching agreement is a fundamental problem in distributed computing. Some examples are Leader election / Mutual Exclusion Commit or Abort in distributed transactions Reaching agreement about which process has failed Clock phase synchronization Air traffic control system: all aircrafts must have the same view
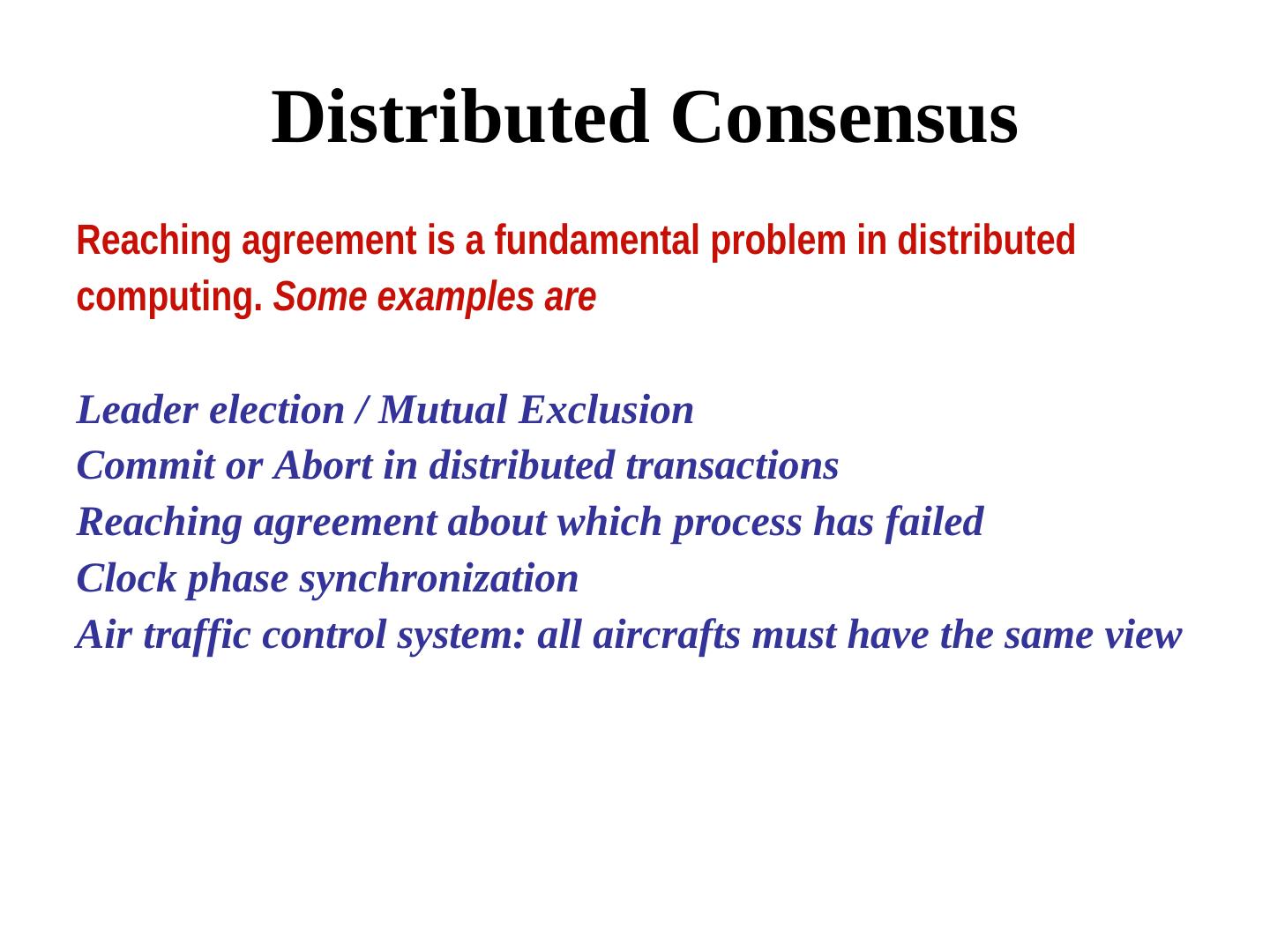
3 . Problem Specification input output p0 u0 v p1 u1 v p2 u2 v p3 u3 v Each process pk has an input value uk. These processes run a program to exchange their inputs, so that finally the outputs of all non-faulty processes become identical, even if one or more processes fail at any time. Furthermore, the output v must be equal to the value of at least one process.
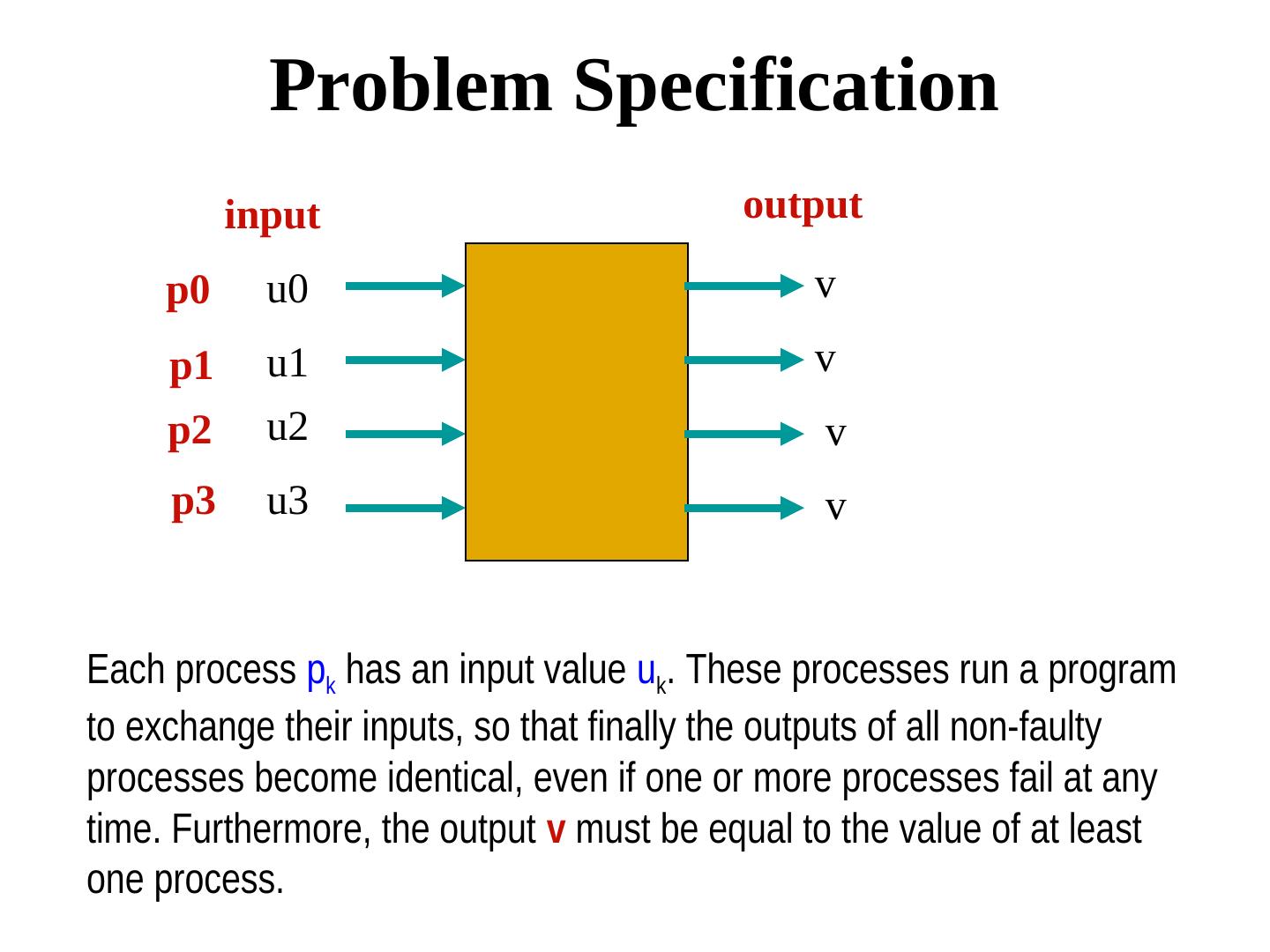
4 . Problem Specification Termination. Every non-faulty process must eventually decide. Agreement. The final decision of every non-faulty process must be identical. Validity. If every non-faulty process begins with the same initial value v, then their final decision must be v.
5 . Observation • If there is no failure, then reaching consensus is trivial. All-to-all broadcast followed by a applying a choice function … • Consensus in presence of failures can however be complex. The complexity depends on the system model and the type of failures
6 . Asynchronous Consensus Seven members of a busy household decided to hire a cook, since they do not have time to prepare their own food. Each member separately interviewed every applicant for the cook’s position. Depending on how it went, each member voted "yes" (means “hire”) or "no" (means “don't hire”). These members will now have to communicate with one another to reach a uniform final decision about whether the applicant will be hired. The process will be repeated with the next applicant, until someone is hired. Consider various modes of communication like shared memory or message passing. Also assume that one process (i.e. a member) may crash at any time.
7 . Asynchronous Consensus Theorem. In a purely asynchronous distributed system, the consensus problem is impossible to solve if even a single process crashes. Result due to Fischer, Lynch, Patterson (commonly known as FLP 85). Received the most influential paper award of ACM PODC in 2001
8 . Proof Bivalent and Univalent states A decision state is bivalent, if starting from that state, there exist two distinct executions leading to two distinct decision values 0 or 1. Otherwise it is univalent. A univalent state may be either 0-valent or 1-valent.
9 . Proof (continued) Lemma. No execution can lead from a 0-valent to a 1-valent state or vice versa. Proof. Follows from the definition of 0-valent and 1-valent states.
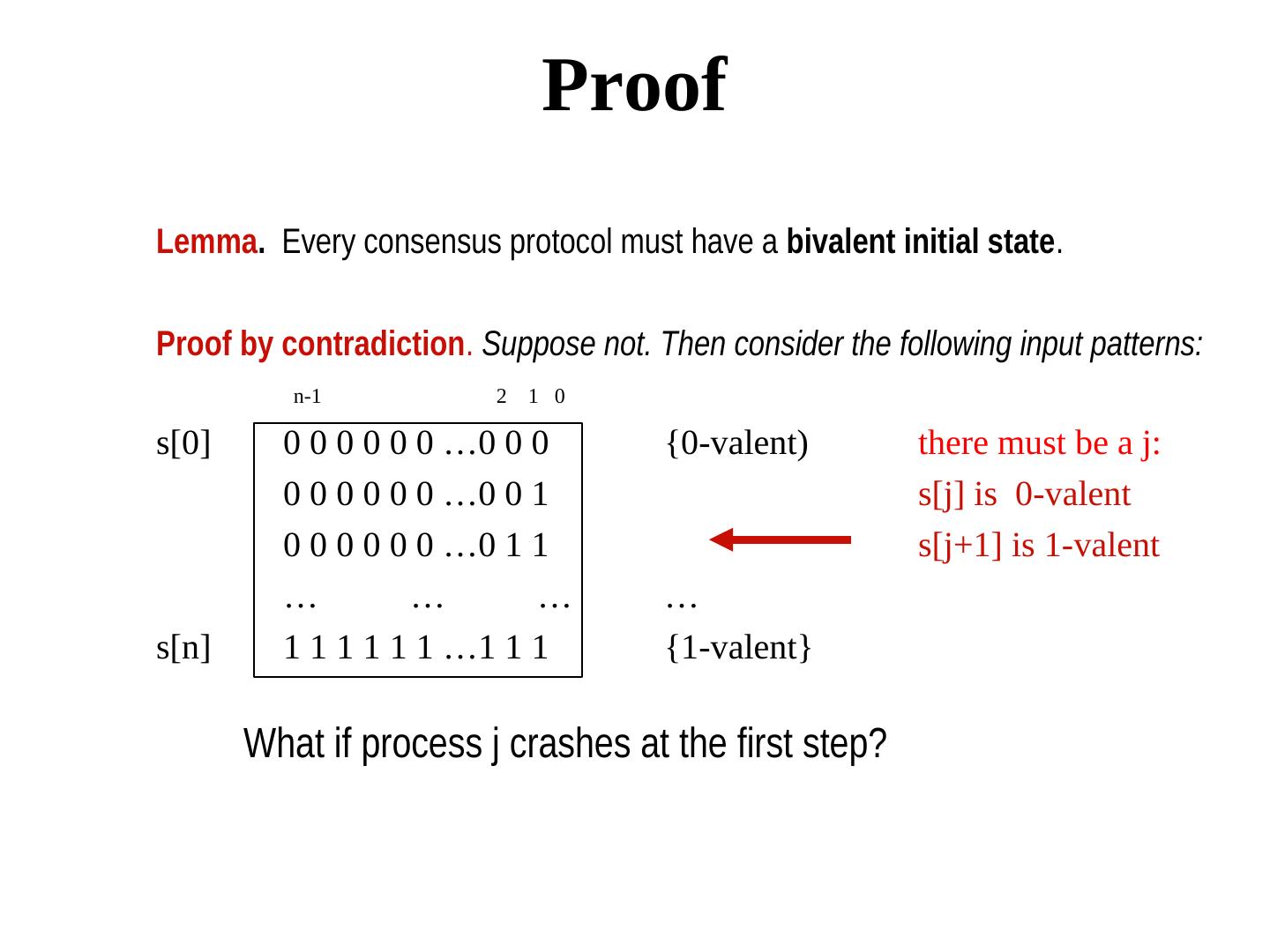
10 . Proof Lemma. Every consensus protocol must have a bivalent initial state. Proof by contradiction. Suppose not. Then consider the following input patterns: n-1 2 1 0 s[0] 0 0 0 0 0 0 …0 0 0 {0-valent) there must be a j: 0 0 0 0 0 0 …0 0 1 s[j] is 0-valent 0 0 0 0 0 0 …0 1 1 s[j+1] is 1-valent … … … … s[n] 1 1 1 1 1 1 …1 1 1 {1-valent} What if process j crashes at the first step?
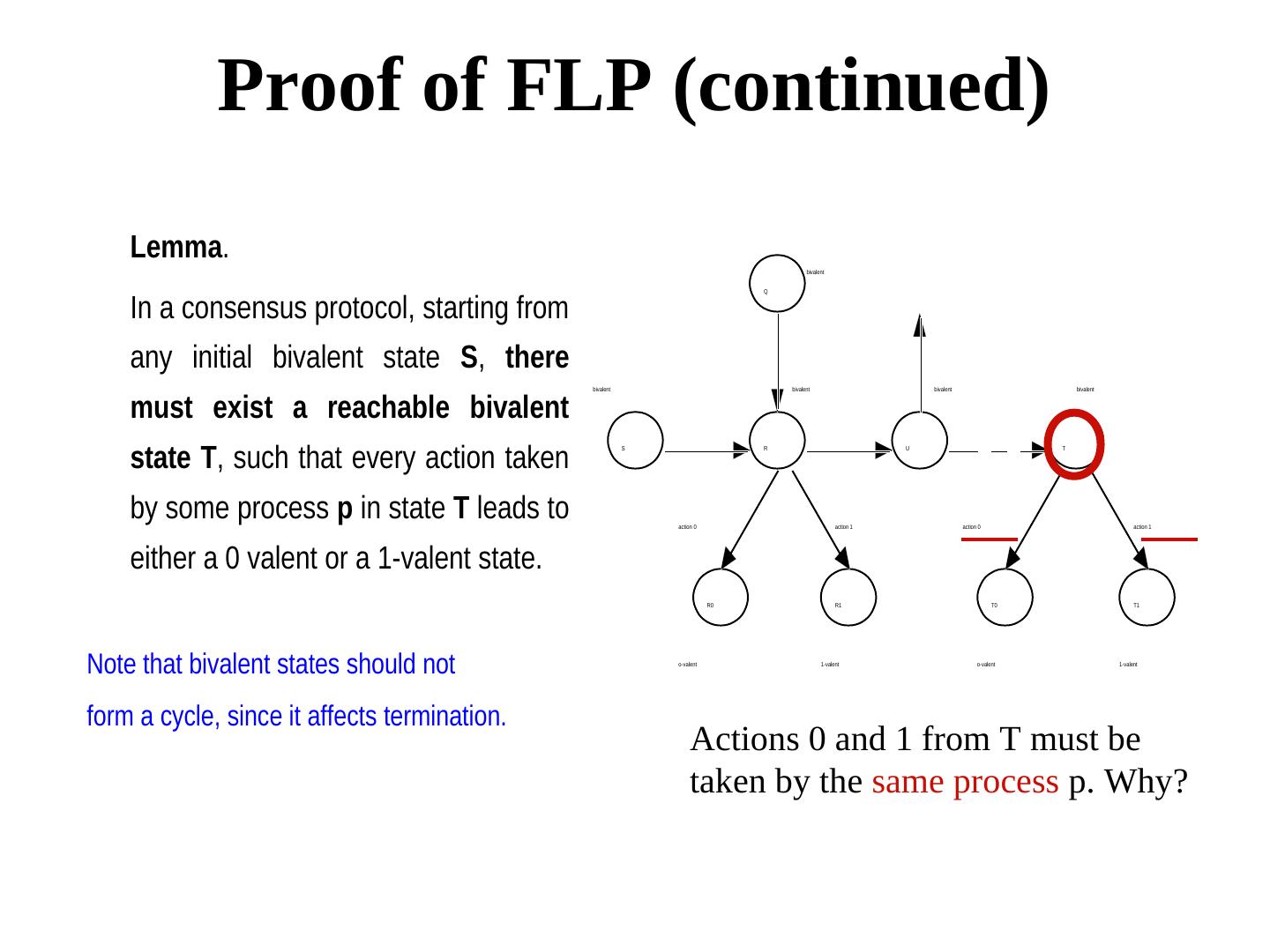
11 . Proof of FLP (continued) Lemma. bivalent In a consensus protocol, starting from Q any initial bivalent state S, there bivalent bivalent bivalent bivalent must exist a reachable bivalent state T, such that every action taken S R U T by some process p in state T leads to action 0 action 1 action 0 action 1 either a 0 valent or a 1-valent state. R0 R1 T0 T1 Note that bivalent states should not o-valent 1-valent o-valent 1-valent form a cycle, since it affects termination. Actions 0 and 1 from T must be taken by the same process p. Why?
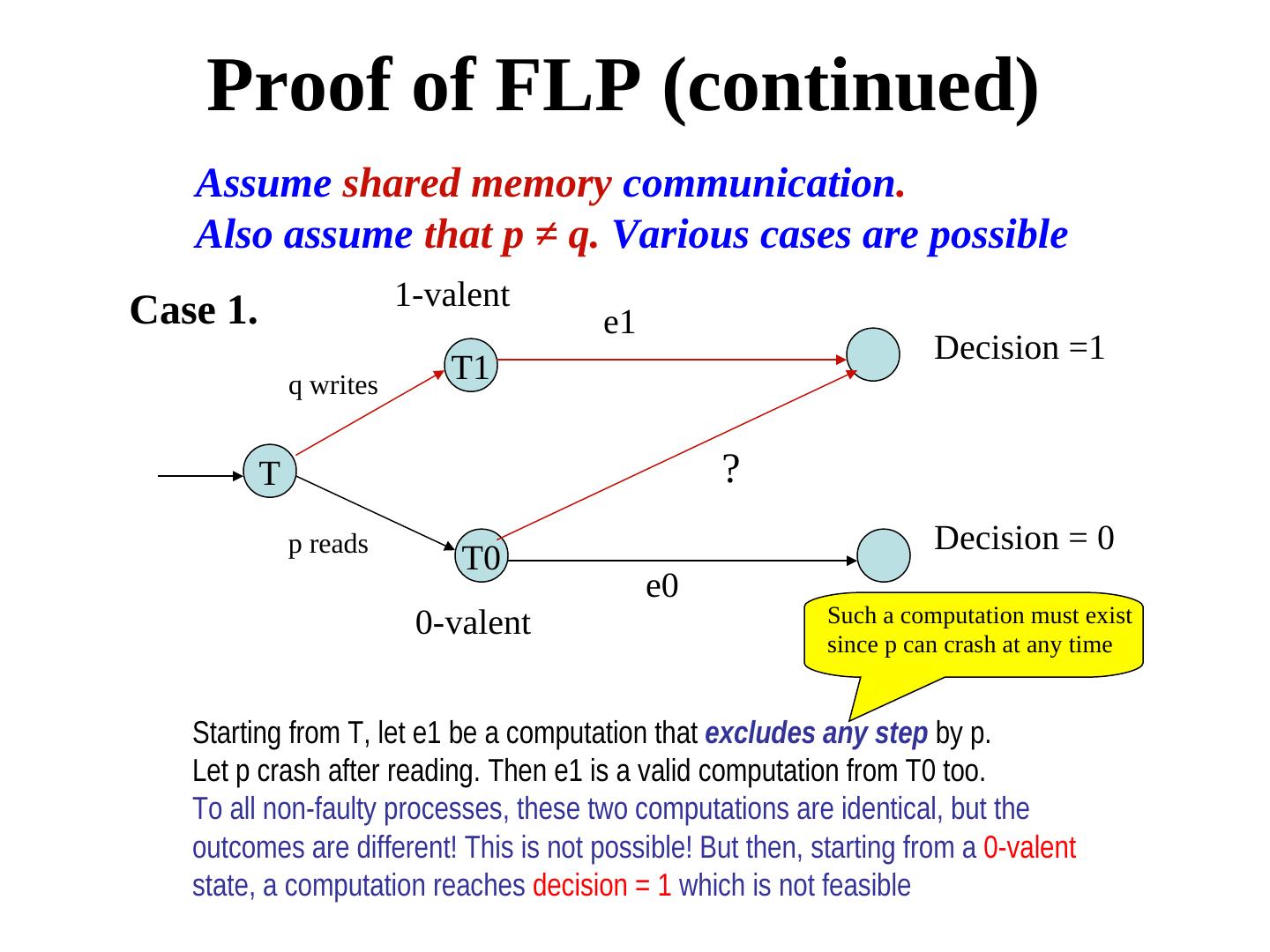
12 . Proof of FLP (continued) Assume shared memory communication. Also assume that p ≠ q. Various cases are possible 1-valent Case 1. e1 Decision =1 q writes T1 T ? p reads Decision = 0 T0 e0 0-valent Such a computation must exist since p can crash at any time Starting from T, let e1 be a computation that excludes any step by p. Let p crash after reading. Then e1 is a valid computation from T0 too. To all non-faulty processes, these two computations are identical, but the outcomes are different! This is not possible! But then, starting from a 0-valent state, a computation reaches decision = 1 which is not feasible
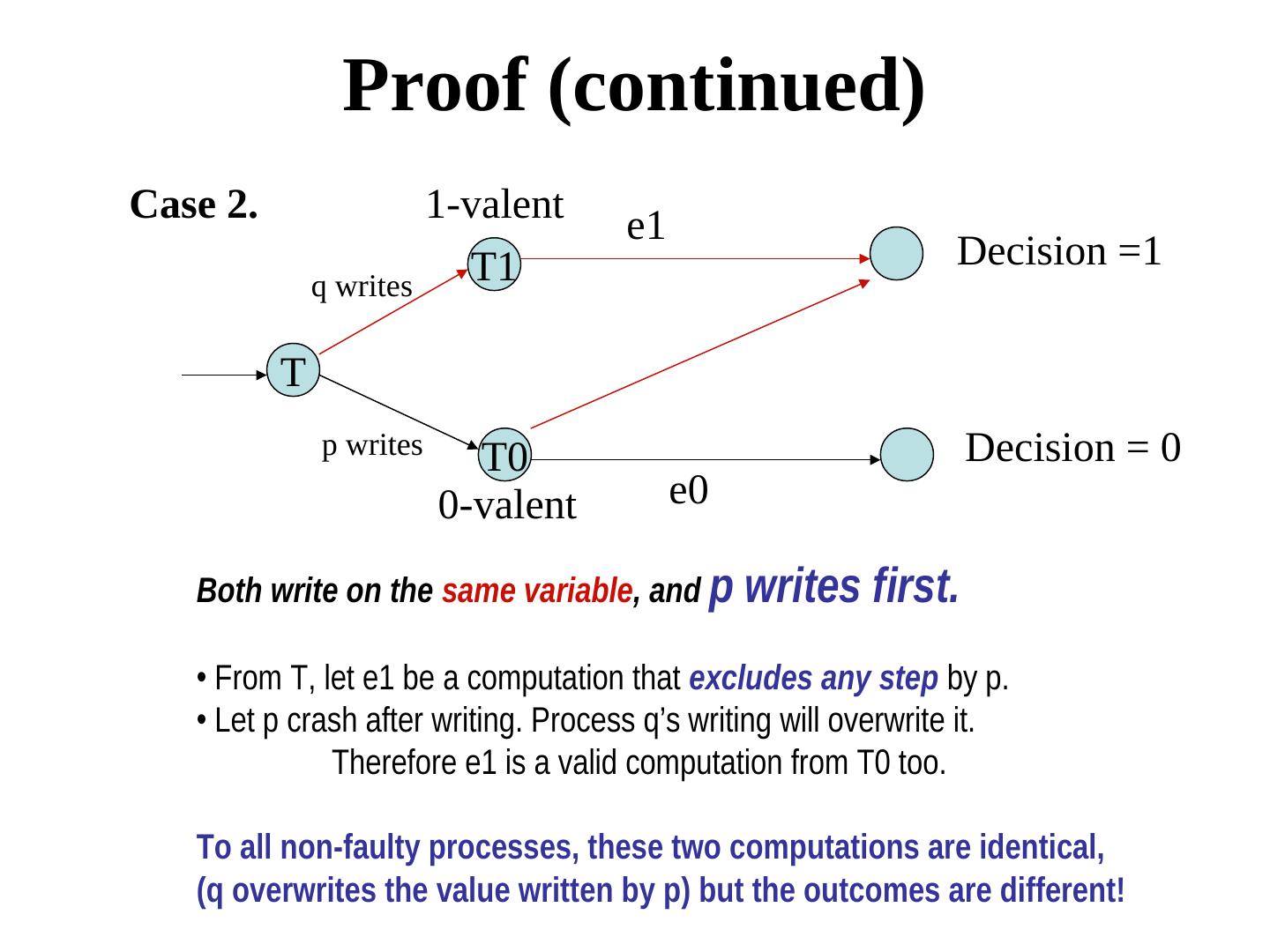
13 . Proof (continued) Case 2. 1-valent e1 T1 Decision =1 q writes T p writes T0 Decision = 0 0-valent e0 Both write on the same variable, and p writes first. • From T, let e1 be a computation that excludes any step by p. • Let p crash after writing. Process q’s writing will overwrite it. Therefore e1 is a valid computation from T0 too. To all non-faulty processes, these two computations are identical, (q overwrites the value written by p) but the outcomes are different!
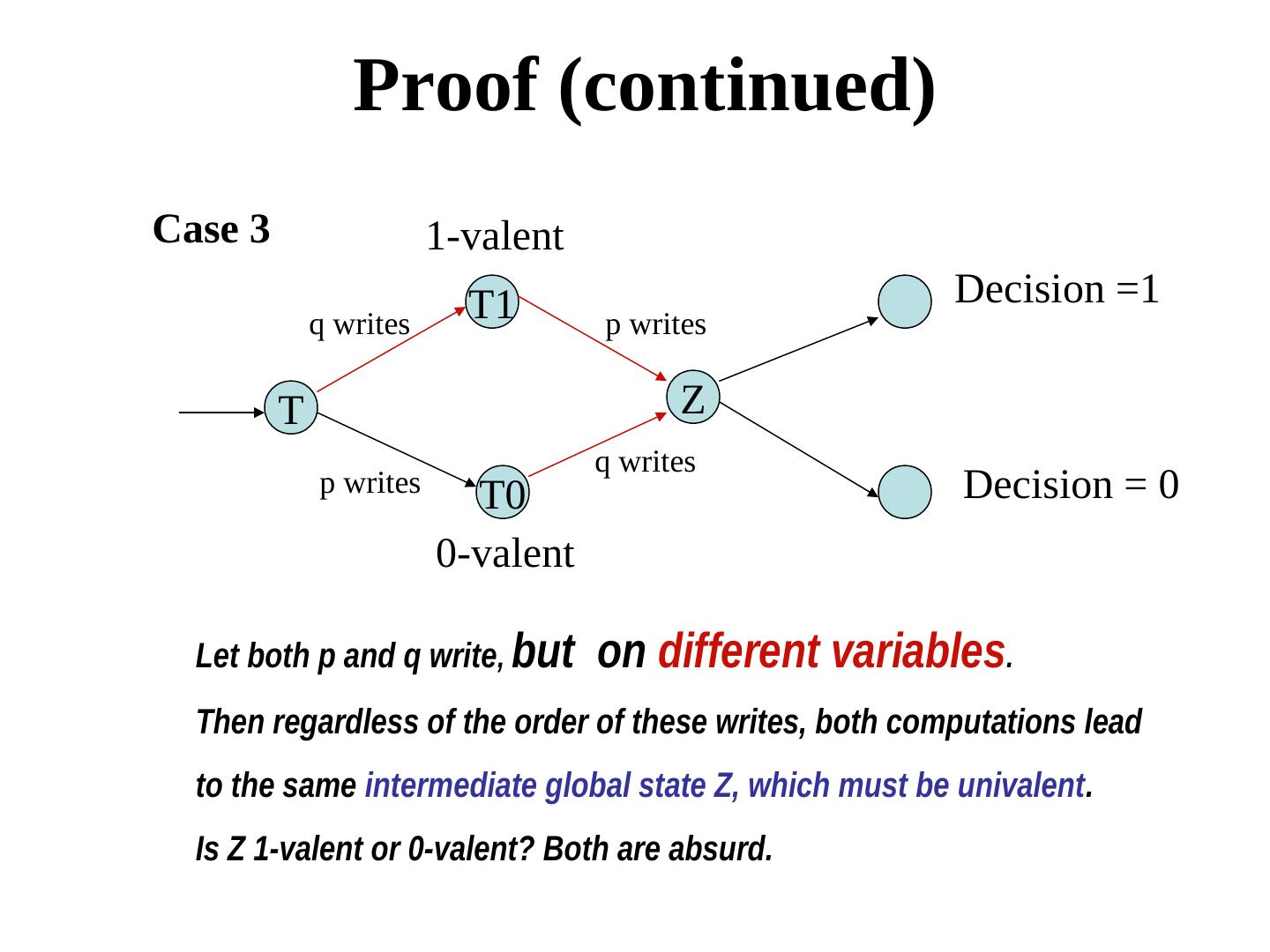
14 . Proof (continued) Case 3 1-valent T1 Decision =1 q writes p writes T Z q writes p writes T0 Decision = 0 0-valent Let both p and q write, but on different variables. Then regardless of the order of these writes, both computations lead to the same intermediate global state Z, which must be univalent. Is Z 1-valent or 0-valent? Both are absurd.
15 . Proof (continued) Similar arguments can be made for communication using the message passing model too (See Nancy Lynch’s book). These lead to the fact that p, q cannot be distinct processes, and p = q. Call p the decider process. What if p crashes in state T? No consensus is reached!
16 . Conclusion • In a purely asynchronous system, there is no solution to the consensus problem if a single process crashes.. • Note that this is true for deterministic algorithms only. Solutions do exist for the consensus problem using randomized algorithm, or using the synchronous model.
17 .Consensus in Synchronous Systems: Byzantine Generals Problem Describes and solves the consensus problem on the synchronous model of communication. Processor speeds have lower bounds and communication delays have upper bounds. - The network is completely connected - Processes undergo byzantine failures, the worst possible kind of failure
18 . Byzantine Generals Problem • n generals {0, 1, 2, ..., n-1} decide about whether to "attack" or to "retreat" during a particular phase of a war. The goal is to agree upon the same plan of action. • Some generals may be "traitors" and therefore send either no input, or send conflicting inputs to prevent the "loyal" generals from reaching an agreement. • Devise a strategy, by which every loyal general eventually agrees upon the same plan, regardless of the action of the traitors.
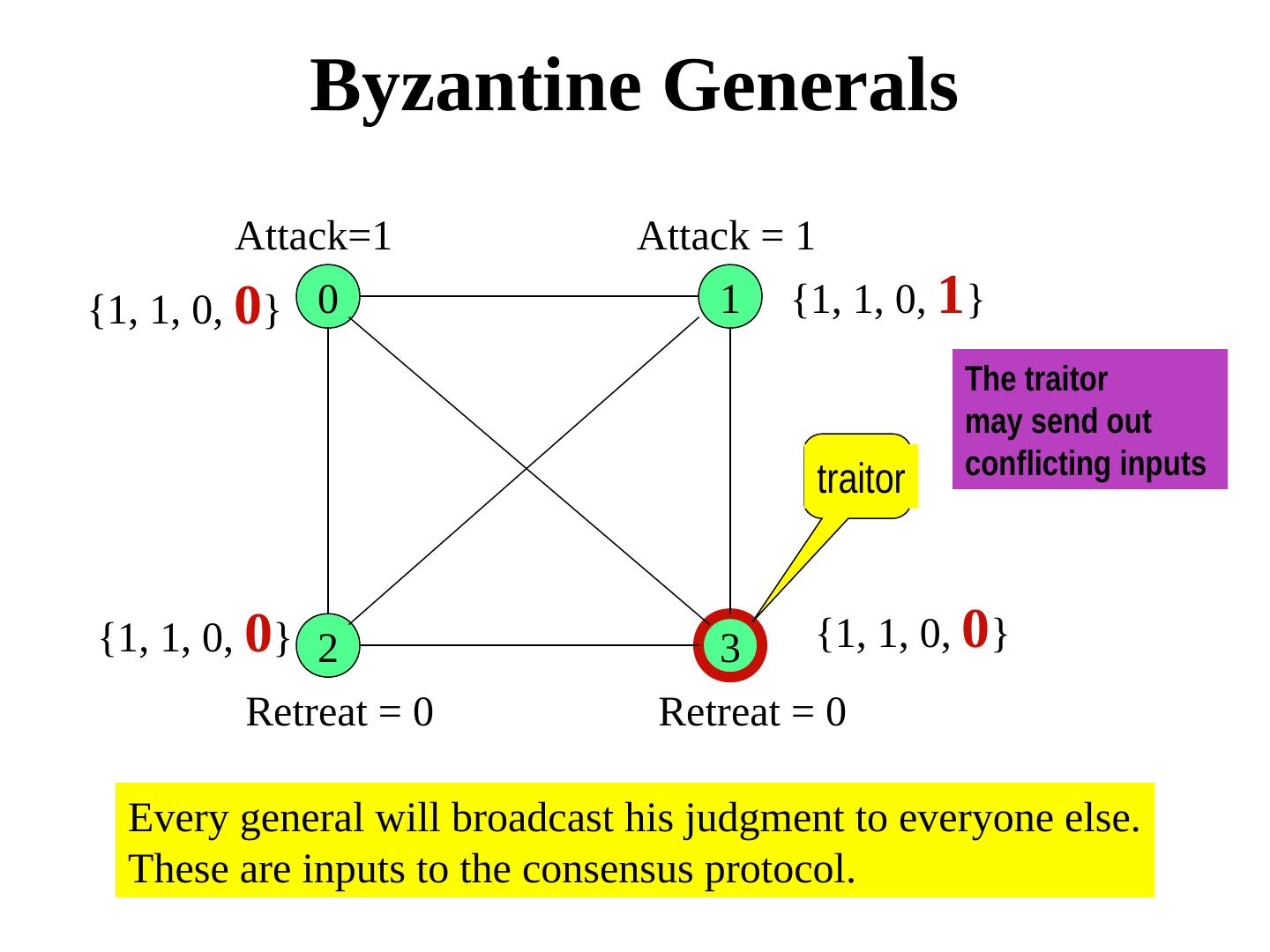
19 . Byzantine Generals Attack=1 Attack = 1 {1, 1, 0, 0} 0 1 {1, 1, 0, 1} The traitor may send out conflicting inputs traitor {1, 1, 0, 0} 2 3 {1, 1, 0, 0} Retreat = 0 Retreat = 0 Every general will broadcast his judgment to everyone else. These are inputs to the consensus protocol.
20 . Byzantine Generals We need to devise a protocol so that every peer (call it a lieutenant) receives the same value from any given general (call it a commander). Clearly, the lieutenants will have to use secondary information. Note that the roles of the commander and the lieutenants will rotate among the generals.
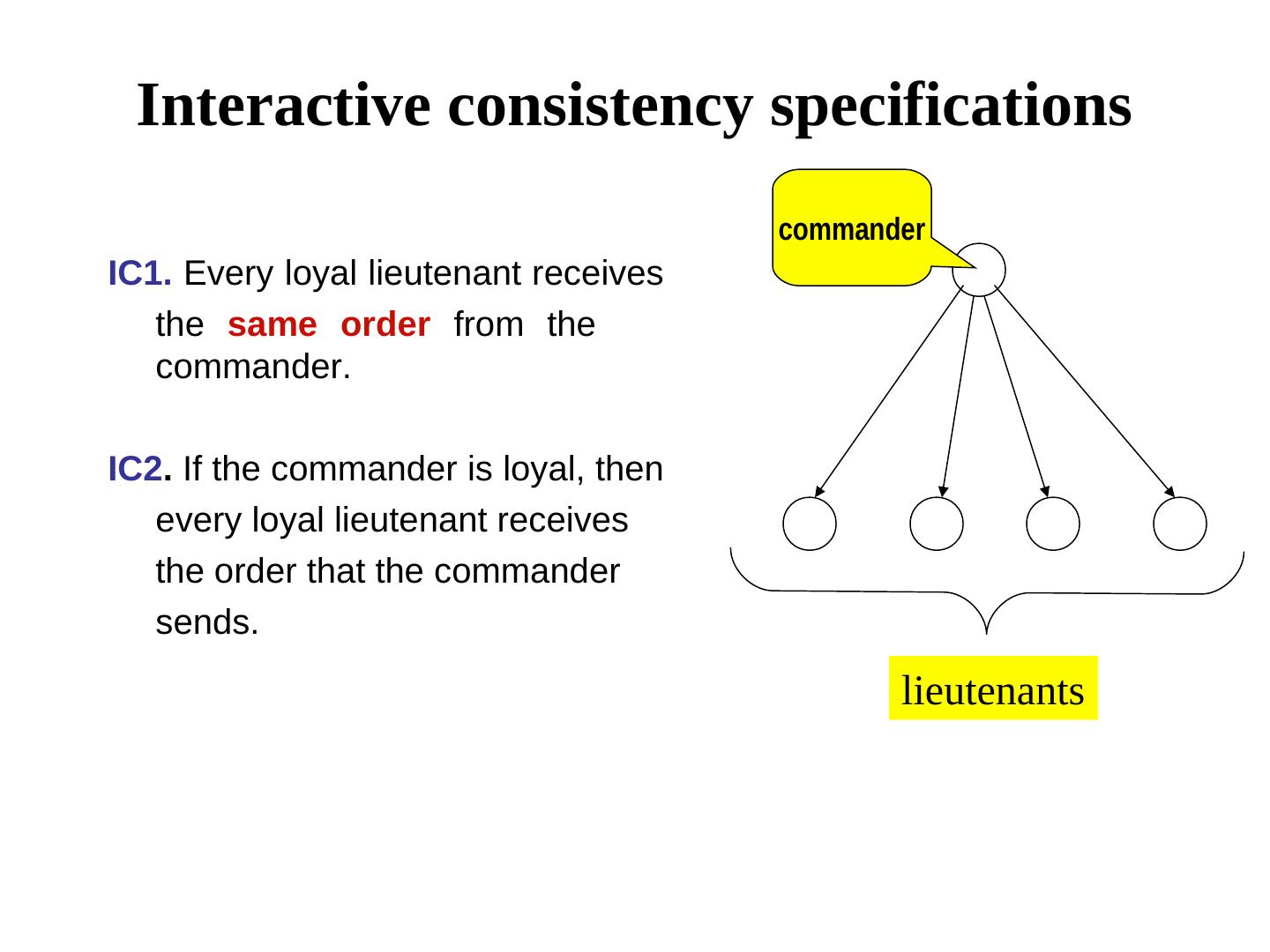
21 . Interactive consistency specifications commander IC1. Every loyal lieutenant receives the same order from the commander. IC2. If the commander is loyal, then every loyal lieutenant receives the order that the commander sends. lieutenants
22 . The Communication Model Oral Messages 1. Messages are not corrupted in transit. 2. Messages can be lost, but the absence of message can be detected. 3. When a message is received (or its absence is detected), the receiver knows the identity of the sender (or the defaulter). OM(m) represents an interactive consistency protocol in presence of at most m traitors.
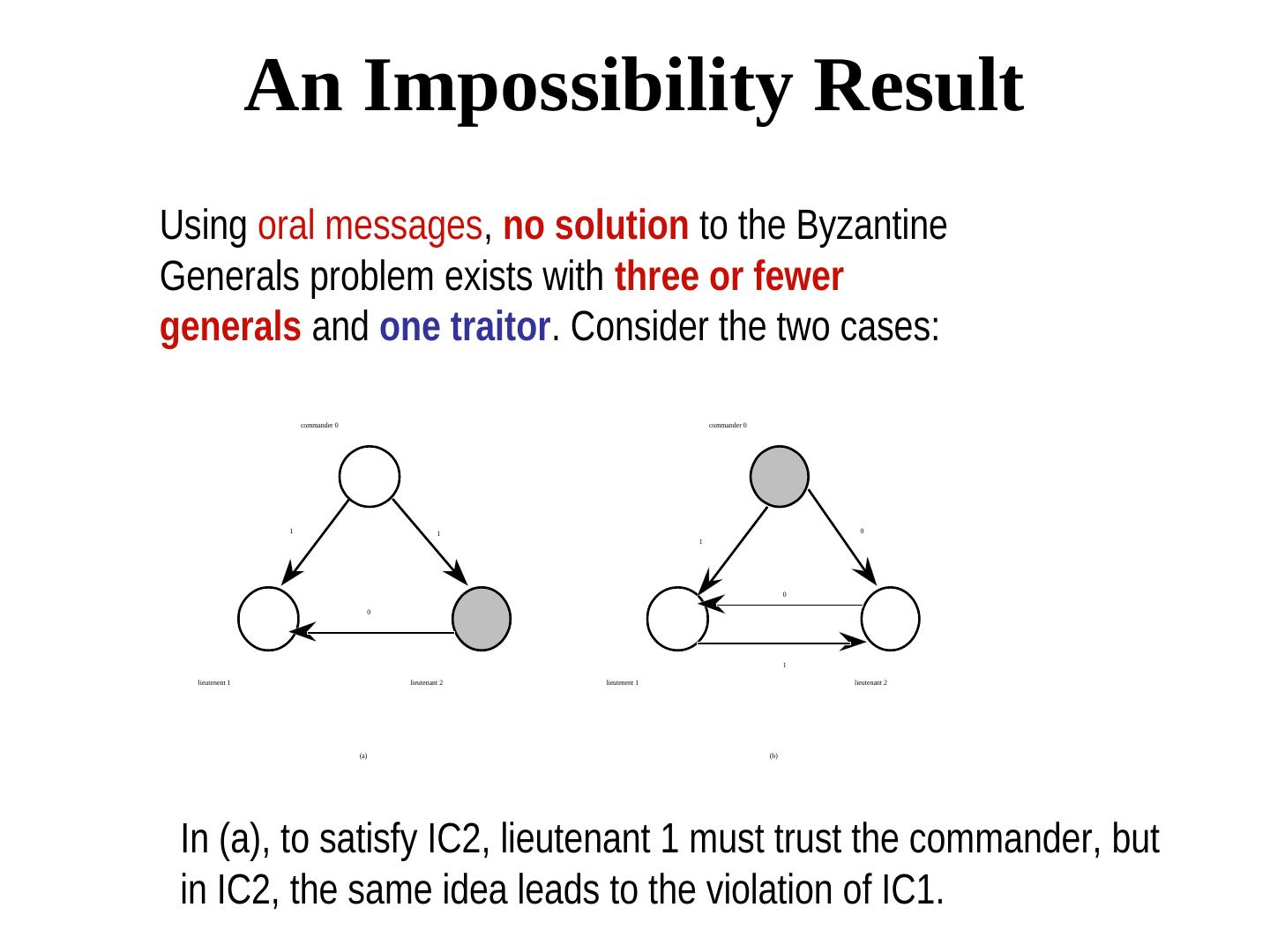
23 . An Impossibility Result Using oral messages, no solution to the Byzantine Generals problem exists with three or fewer generals and one traitor. Consider the two cases: commander 0 commander 0 1 1 0 1 0 0 1 lieutenent 1 lieutenant 2 lieutenent 1 lieutenant 2 (a) (b) In (a), to satisfy IC2, lieutenant 1 must trust the commander, but in IC2, the same idea leads to the violation of IC1.
24 . Impossibility result Using oral messages, no solution to the Byzantine Generals problem exists with 3m or fewer generals and m traitors (m > 0). The proof is by contradiction. Assume that such a solution exists. Now, divide the 3m generals into three groups of m generals each, such that all the traitors belong to one group. Let one general simulate each of these three groups. This scenario is equivalent to the case of three generals and one traitor. We already know that such a solution does not exist. Note. In the original paper, Lamport asks readers to be always suspicious about such an informal reasoning.
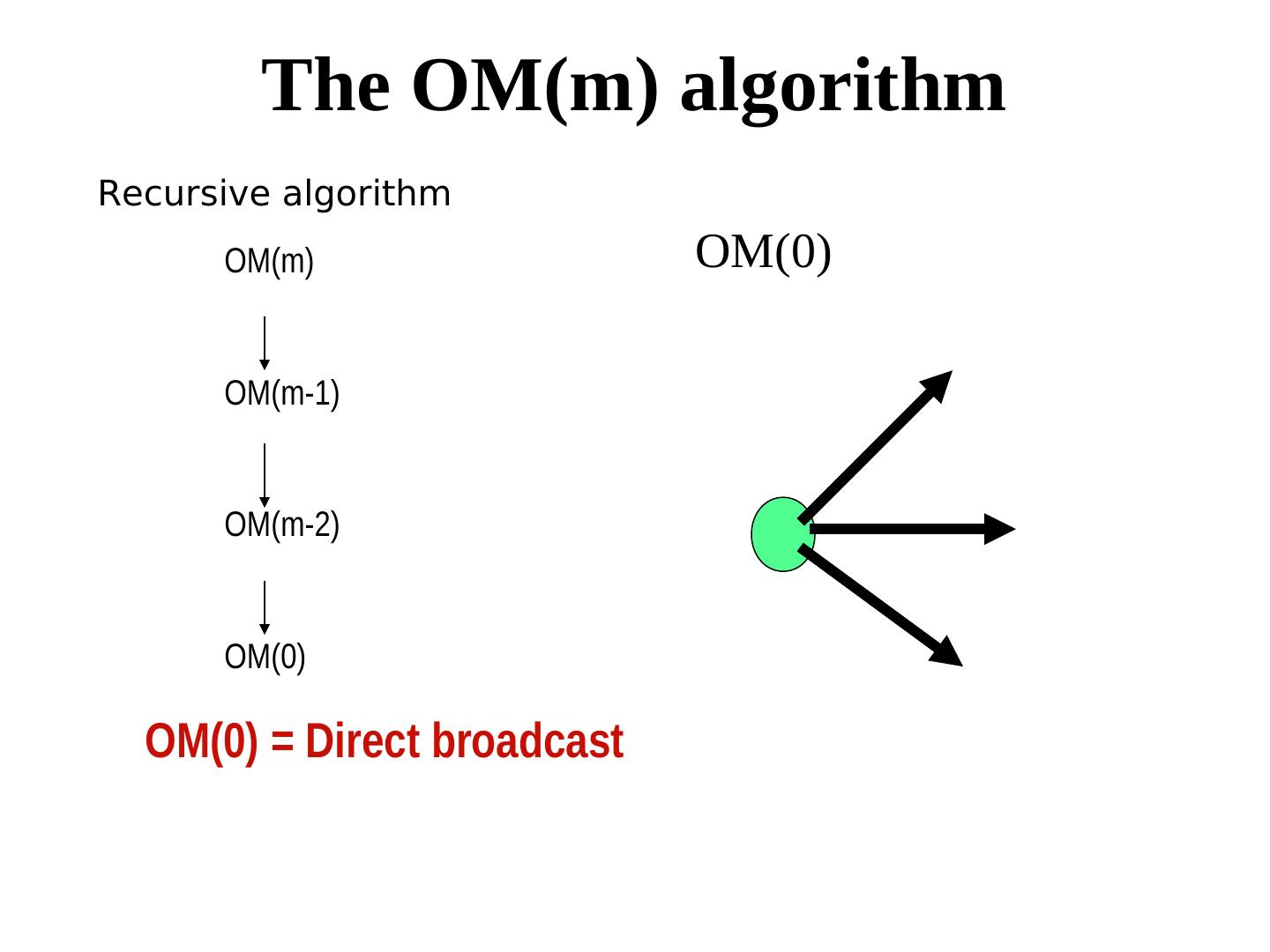
25 . The OM(m) algorithm Recursive algorithm OM(m) OM(0) OM(m-1) OM(m-2) OM(0) OM(0) = Direct broadcast
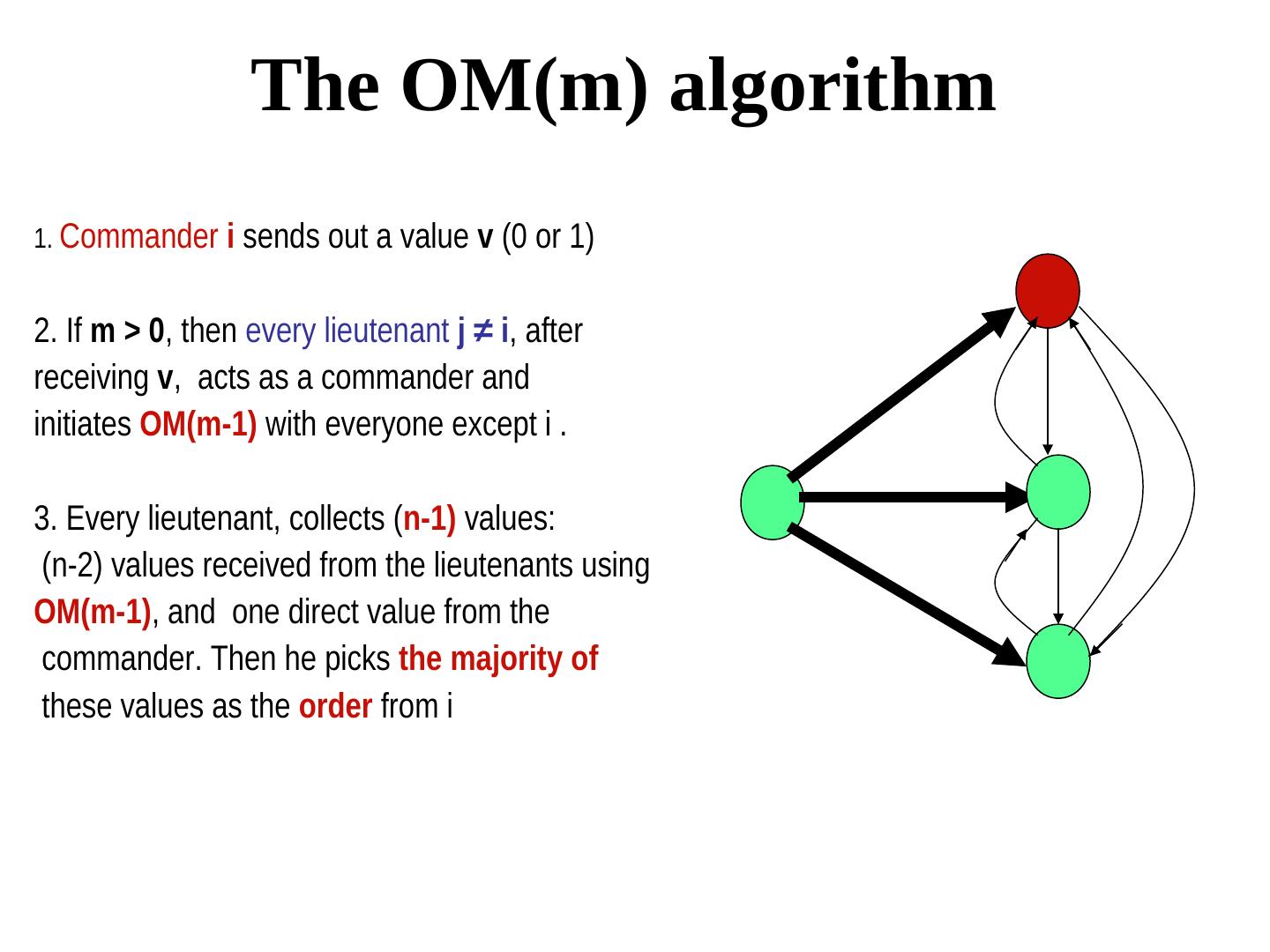
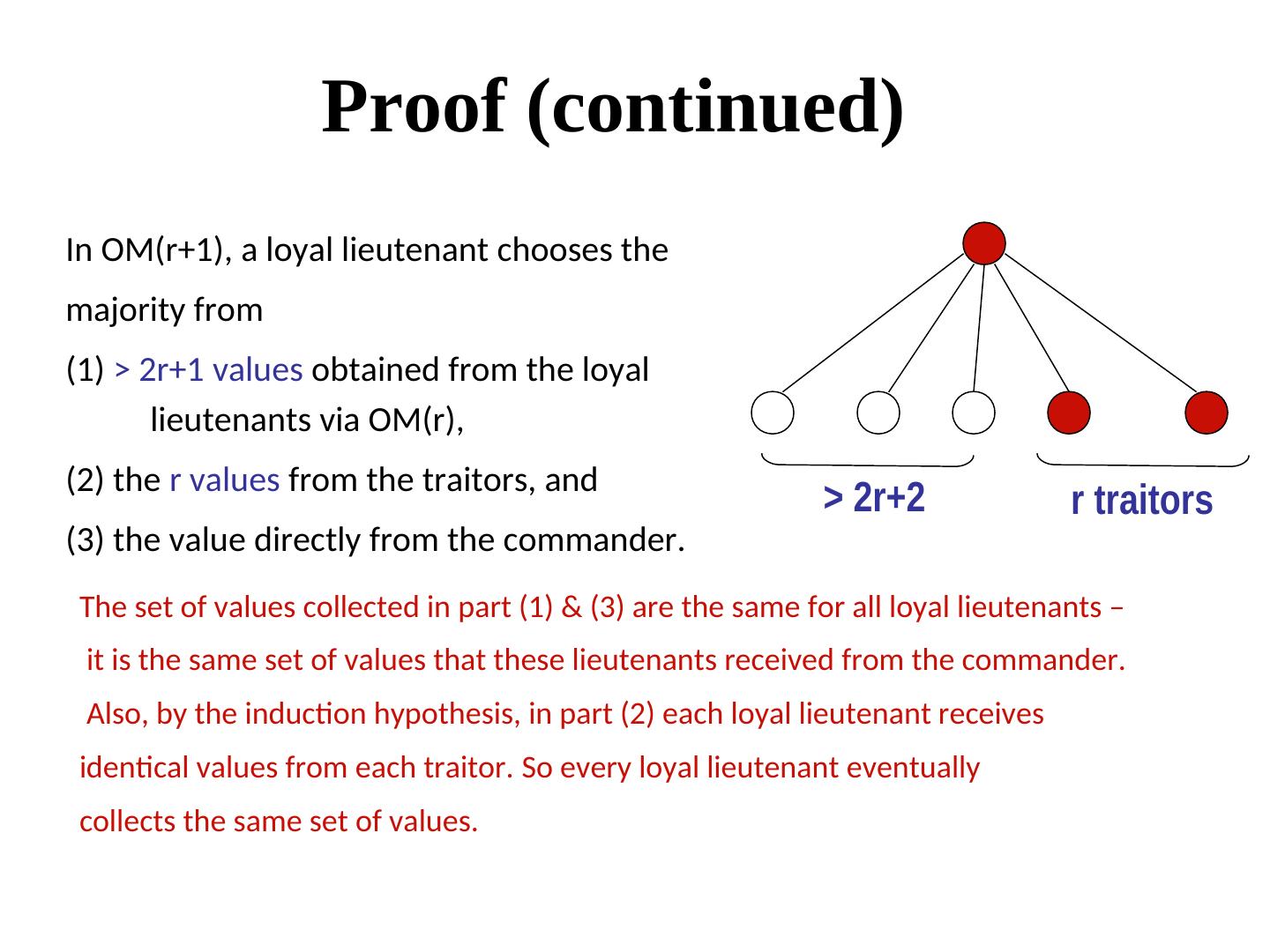
26 . The OM(m) algorithm 1. Commander i sends out a value v (0 or 1) 2. If m > 0, then every lieutenant j ≠ i, after receiving v, acts as a commander and initiates OM(m-1) with everyone except i . 3. Every lieutenant, collects (n-1) values: (n-2) values received from the lieutenants using OM(m-1), and one direct value from the commander. Then he picks the majority of these values as the order from i
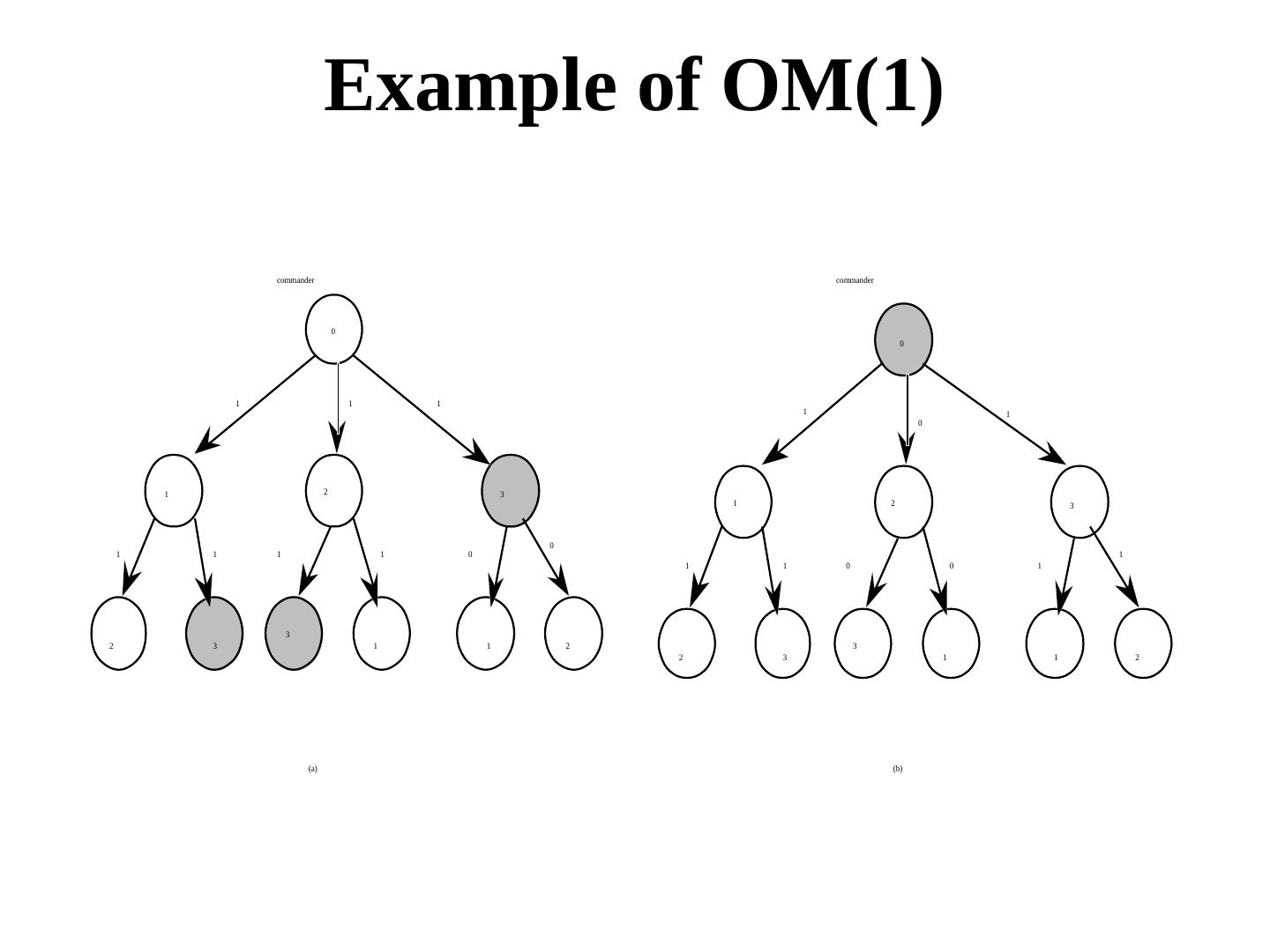
27 . Example of OM(1) commander commander 0 0 1 1 1 1 1 0 1 2 2 3 1 2 2 3 0 1 1 1 1 0 1 1 1 0 0 1 3 2 3 1 1 2 3 2 3 1 1 2 (a) (b)
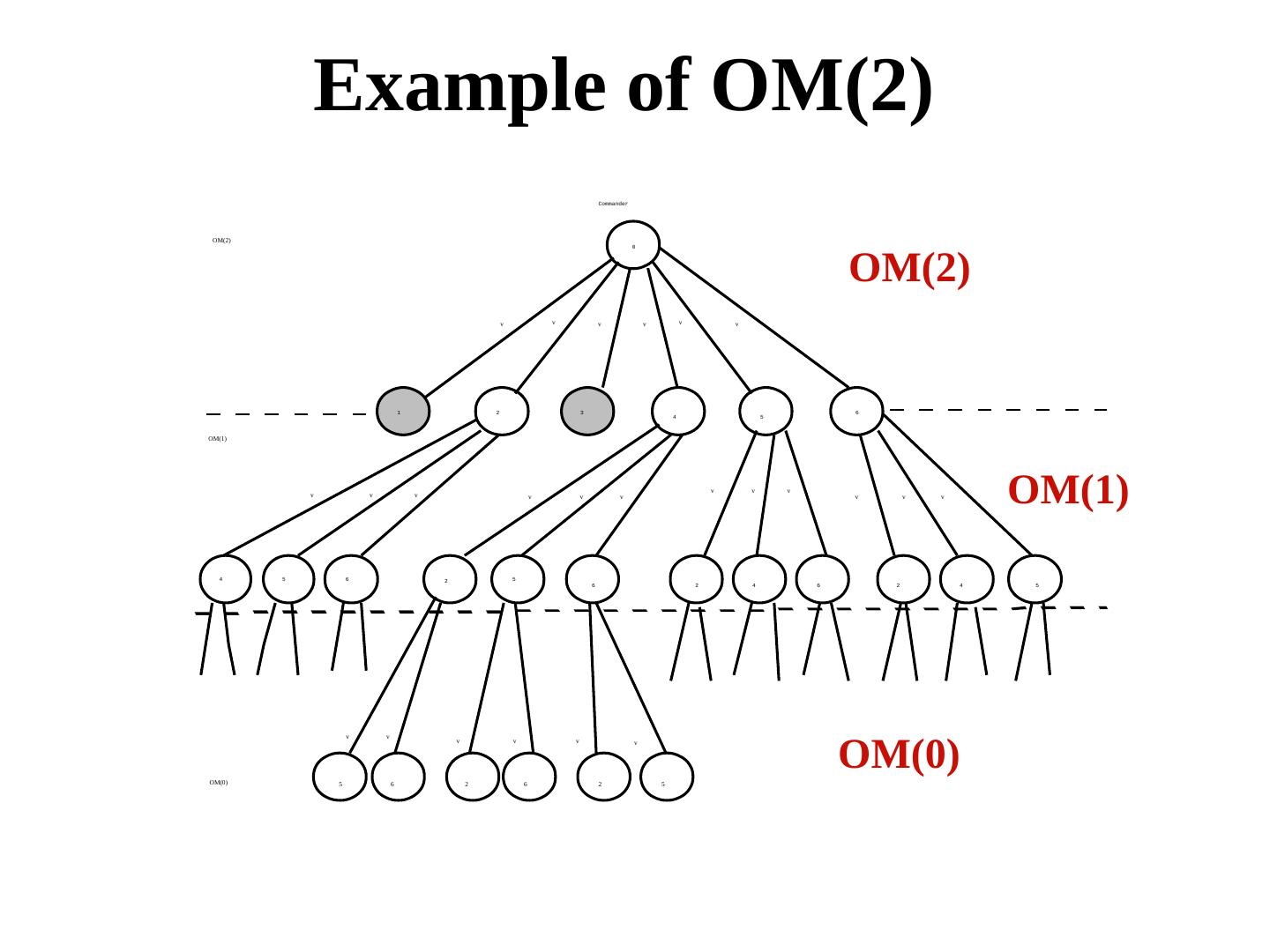
28 . Example of OM(2) Commander OM(2) OM(2) 0 v v v v v v 1 2 3 6 4 5 OM(1) v v v v v v v v v v v v OM(1) 4 5 6 2 5 6 2 4 6 2 4 5 OM(0) v v v v v v OM(0) 5 6 2 6 2 5
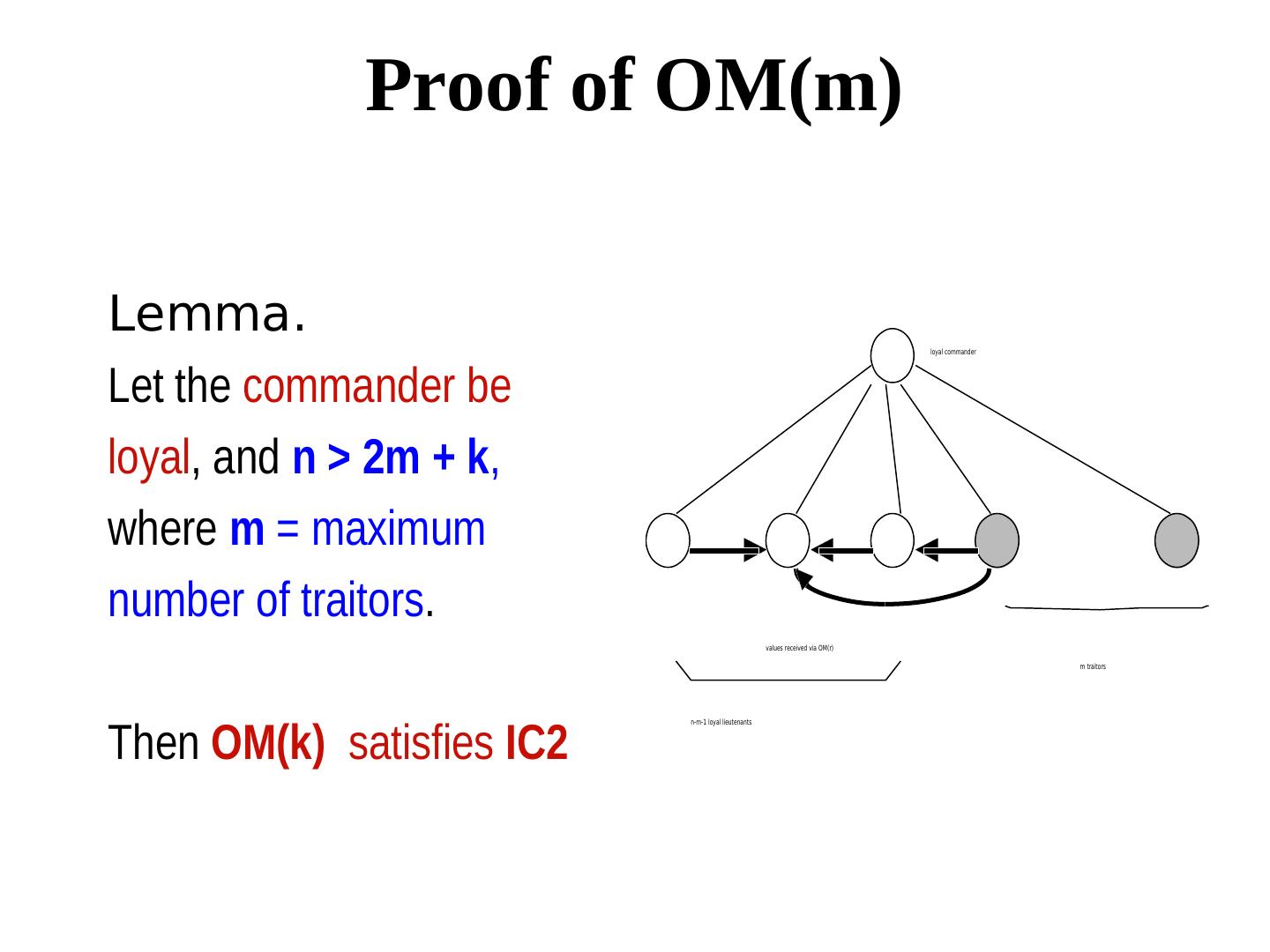
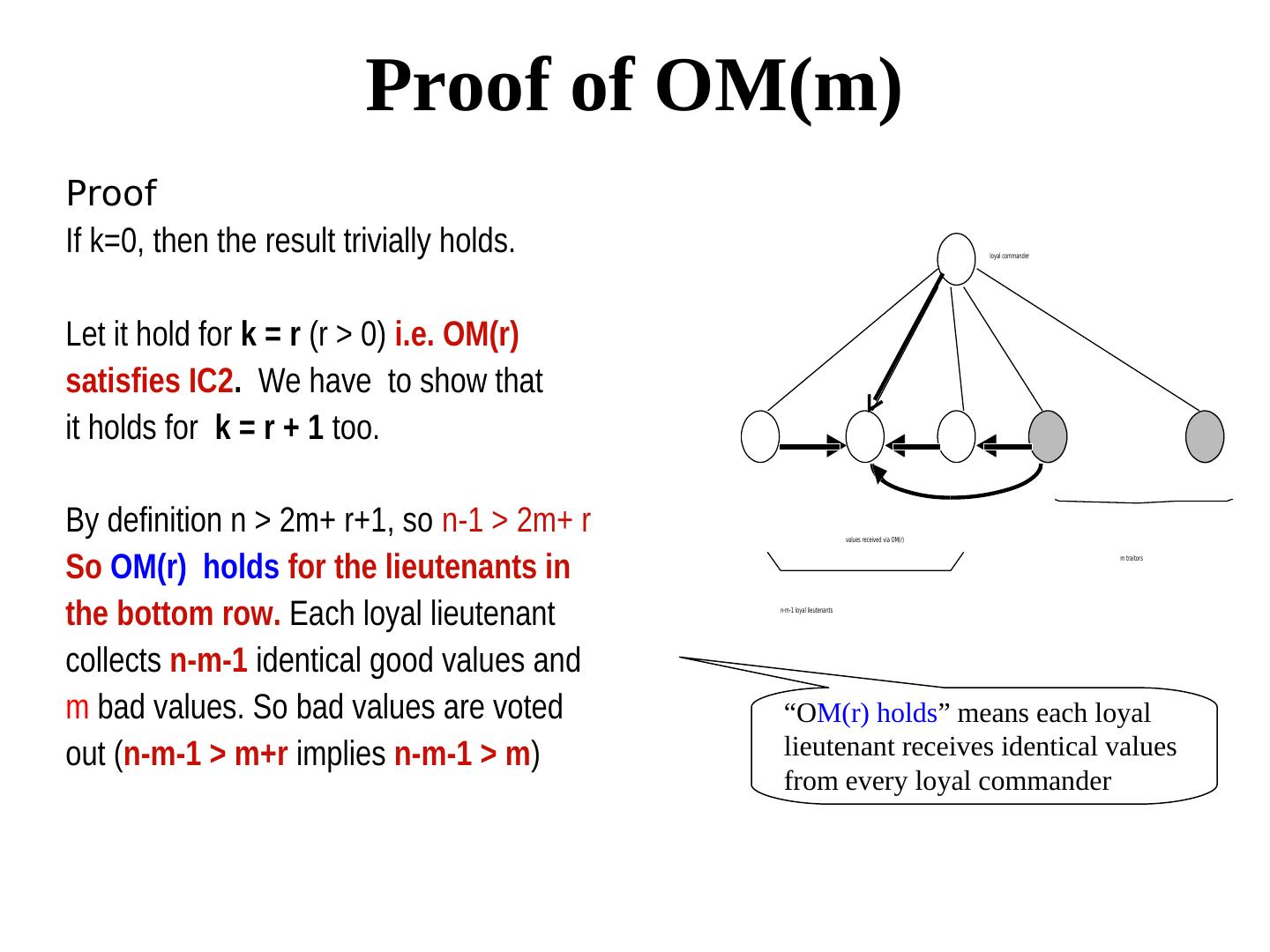
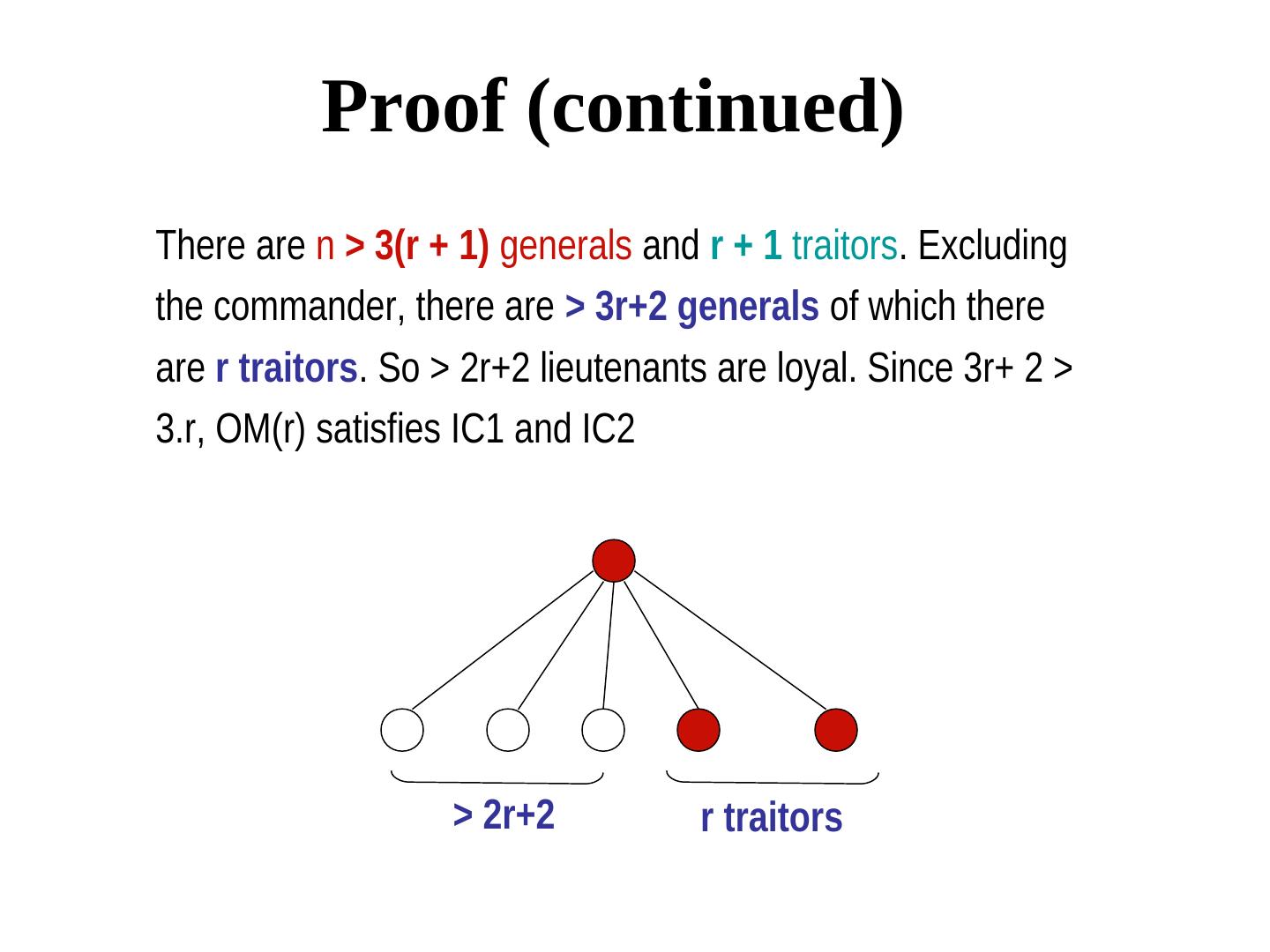
29 . Proof of OM(m) Lemma. loyal commander Let the commander be loyal, and n > 2m + k, where m = maximum number of traitors. values received via OM(r) m traitors Then OM(k) satisfies IC2 n-m-1 loyal lieutenants