- 快召唤伙伴们来围观吧
- 微博 QQ QQ空间 贴吧
- 文档嵌入链接
- 复制
- 微信扫一扫分享
- 已成功复制到剪贴板
数据通信:Internet
展开查看详情
1 .Chapter 10 The Internet
2 .Internet Today’s present Internet is a vast collection of thousands of networks and their attached devices Internet began as the Arpanet during the 1960s One high-speed backbone connected several university, government, and research sites Backbone was capable of supporting 56 kbps transmission speeds and eventually became financed by the National Science Foundation (NSF)
3 .History of Internet 1969: ARPANET started by the US Department of Defense as a network of four computers 1981: NSF funds development of CSNET access BITNET established 1983: ARPANET split into two networks (MILNET and Reduced-ARPANET) 1987: NSF funds development of new high-speed network (NSFNET) 1989: Tim Berners-Lee at CERN proposes Internet Protocols CSNET merges with BITNET 1990: NSFNET replaces ARPANET 1991: CERN releases World Wide Web 1995: NSFNET reverts to research network 1996: Work on Internet2 begins 1998: ICANN established to regulate IP addresses
4 .Protocols (I) To support the Internet and all its services, many protocols are necessary Internet Protocol (IP) Transmission Control Protocol (TCP) Address Resolution Protocol (ARP) Dynamic Host Configuration Protocol (DHCP) Network Address Translation (NAT)
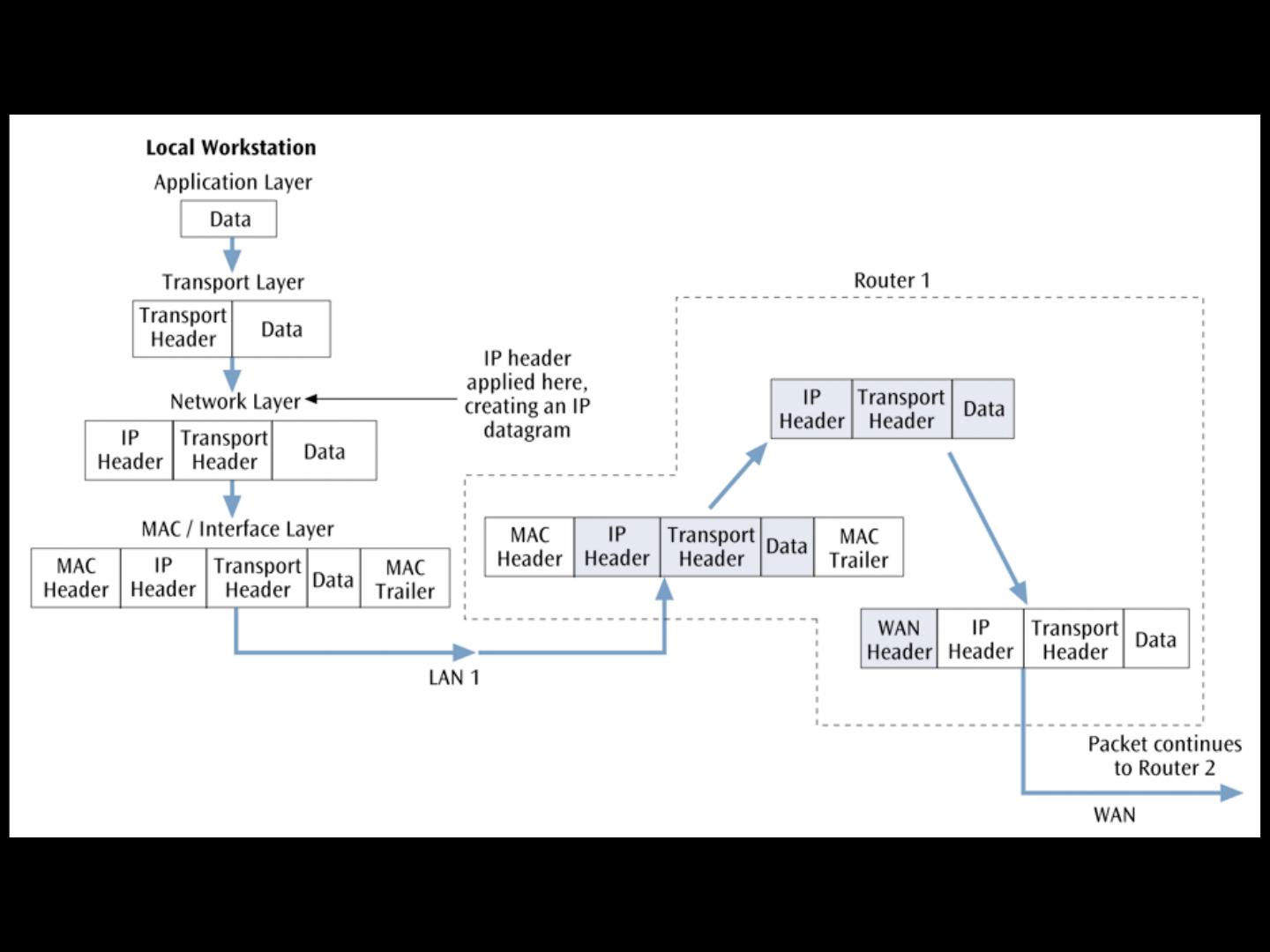
5 .Protocols (II) The Internet model An application, such as e-mail, resides at the highest layer A transport protocol, such as TCP, resides at the transport layer The Internet Protocol (IP) resides at the Internet or network layer A particular media and its framing resides at the network access (or data link) layer
6 .
7 .IP prepares a packet for transmission across the Internet The IP header is encapsulated onto a transport data packet The IP packet is then passed to the next layer where further network information is encapsulated onto it Using IP, a router: Makes routing decision based on the destination address May have to fragment the datagram into smaller datagrams (very rare) using Fragment Offset May determine that current datagram has been hopping around the network too long and delete it (Time to Live) Internet Protocol (IP)
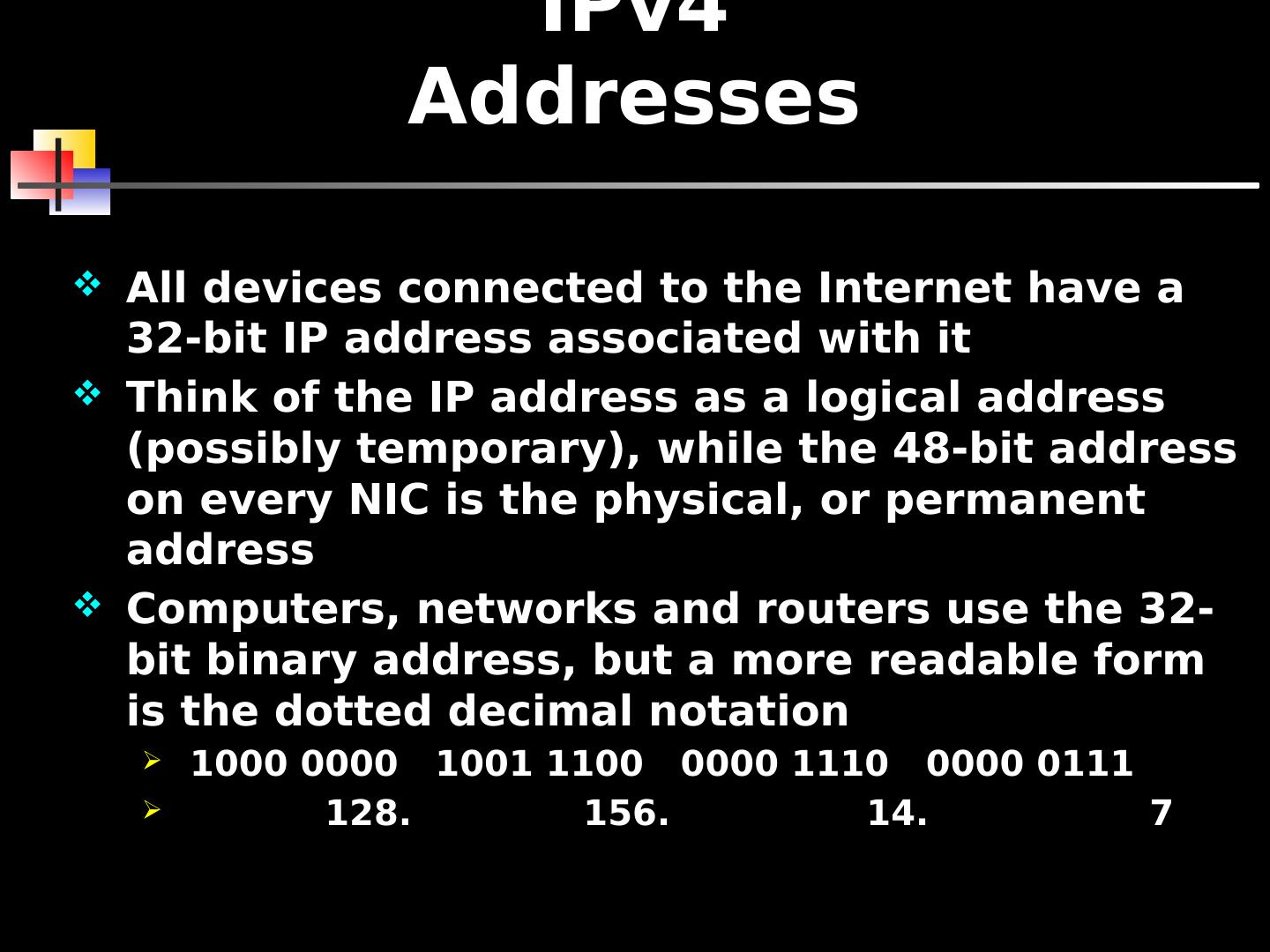
8 .All devices connected to the Internet have a 32-bit IP address associated with it Think of the IP address as a logical address (possibly temporary), while the 48-bit address on every NIC is the physical, or permanent address Computers, networks and routers use the 32-bit binary address, but a more readable form is the dotted decimal notation 1000 0000 1001 1100 0000 1110 0000 0111 128. 156. 14. 7 IPv4 Addresses
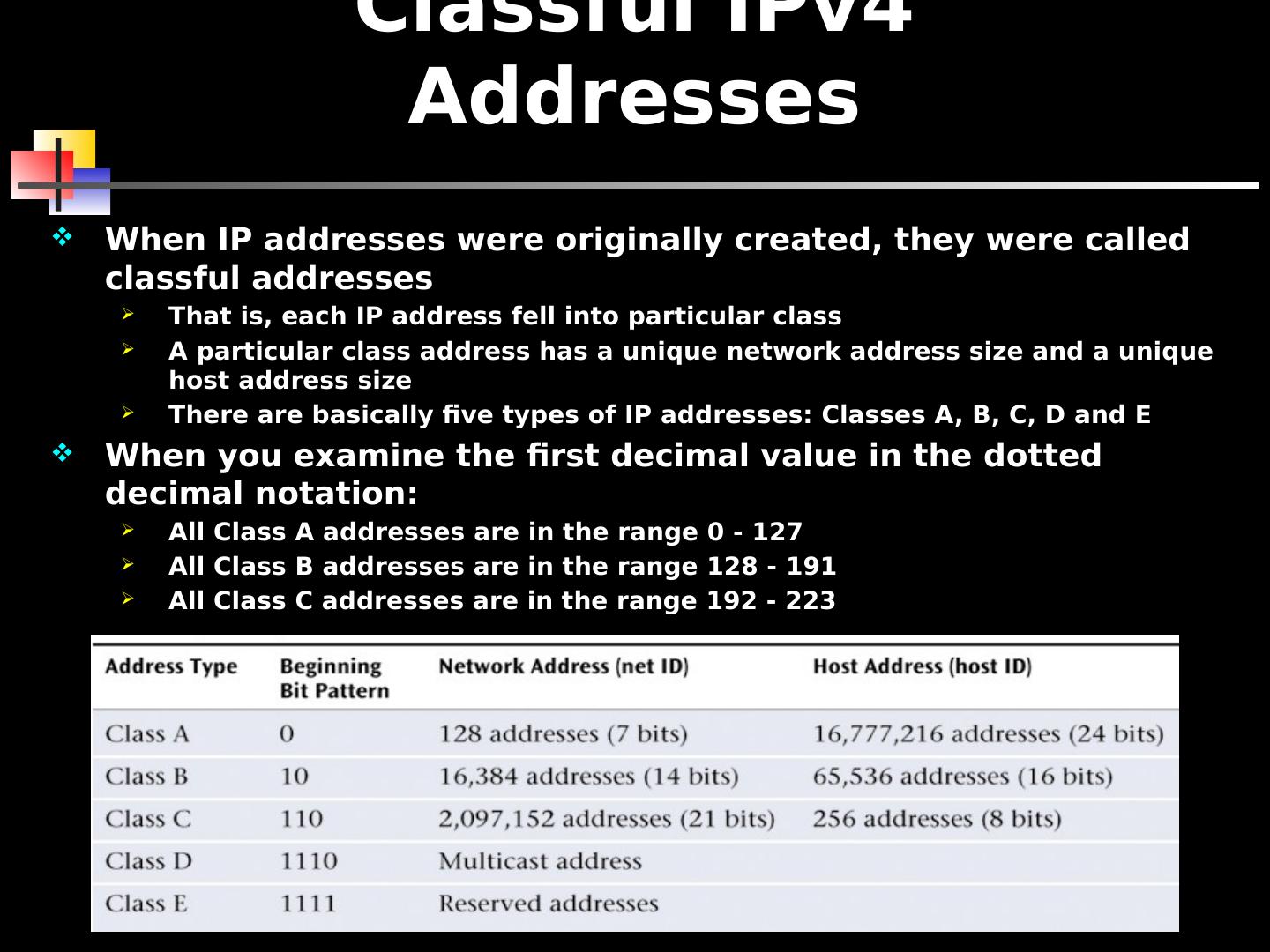
9 .Classful IPv4 Addresses When IP addresses were originally created, they were called classful addresses That is, each IP address fell into particular class A particular class address has a unique network address size and a unique host address size There are basically five types of IP addresses: Classes A, B, C, D and E When you examine the first decimal value in the dotted decimal notation: All Class A addresses are in the range 0 - 127 All Class B addresses are in the range 128 - 191 All Class C addresses are in the range 192 - 223
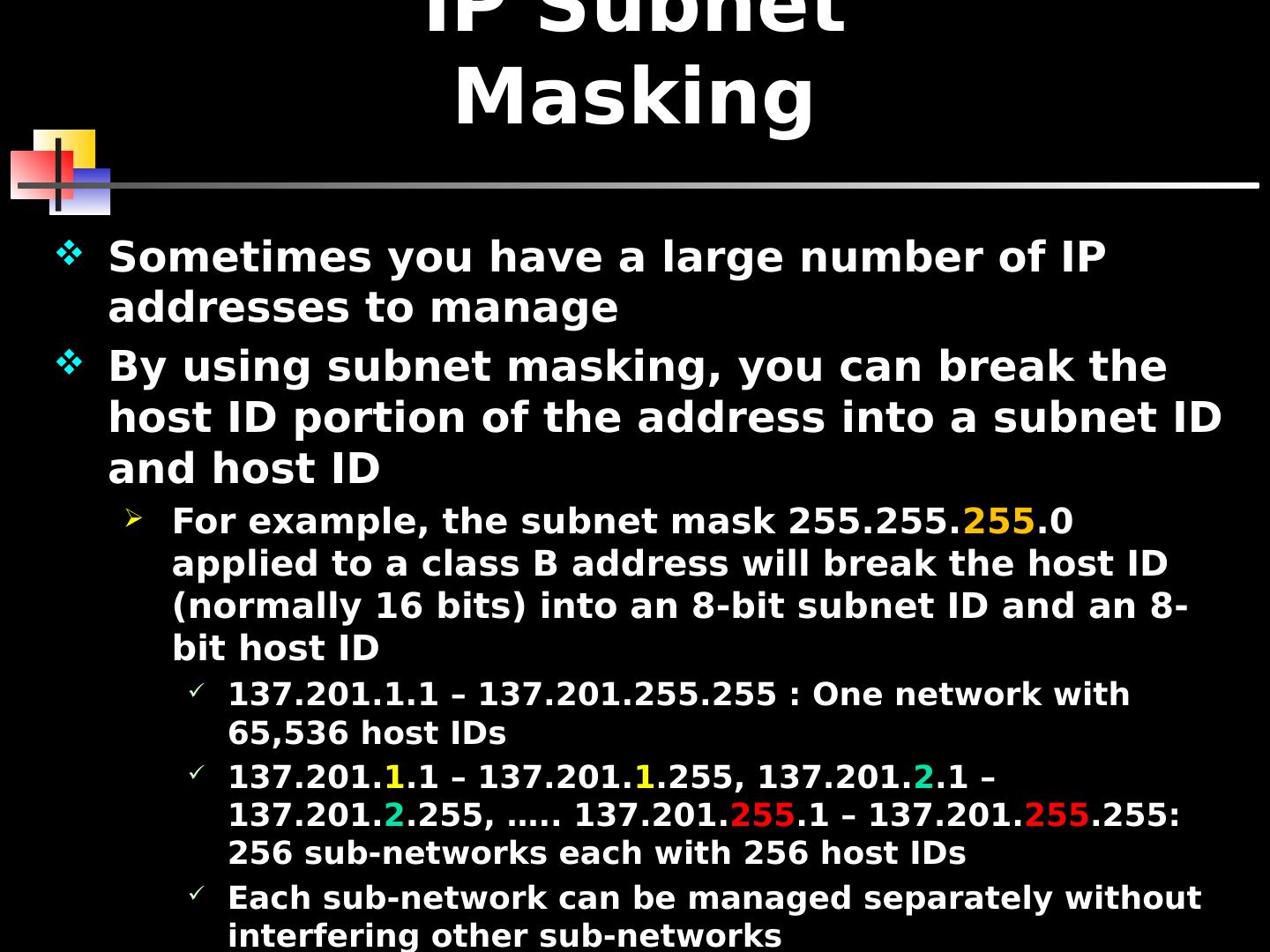
10 .Sometimes you have a large number of IP addresses to manage By using subnet masking, you can break the host ID portion of the address into a subnet ID and host ID For example, the subnet mask 255.255. 255 .0 applied to a class B address will break the host ID (normally 16 bits) into an 8-bit subnet ID and an 8-bit host ID 137.201.1.1 – 137.201.255.255 : One network with 65,536 host IDs 137.201. 1 .1 – 137.201. 1 .255, 137.201. 2 .1 – 137.201. 2 .255, ….. 137.201. 255 .1 – 137.201. 255 .255: 256 sub-networks each with 256 host IDs Each sub-network can be managed separately without interfering other sub-networks Need routers to interconnect sub-networks IP Subnet Masking
11 .Classless IP Addresses With classless addressing, companies (users) do not apply for particular class of addresses Instead, company will get its IP addresses from an Internet service provider (ISP) Most ISPs have already applied for a large number of IP addresses and are willing to lease those addresses to companies Example – instead of applying for two Class C addresses, a company could contact an ISP, which would lease 500 IP addresses to the company The addresses are not identified by any class – they are simply a contiguous block of IP addresses Classless addressing has led to a much more efficient allocation of the IP address space A company can lease only as many addresses as it needs
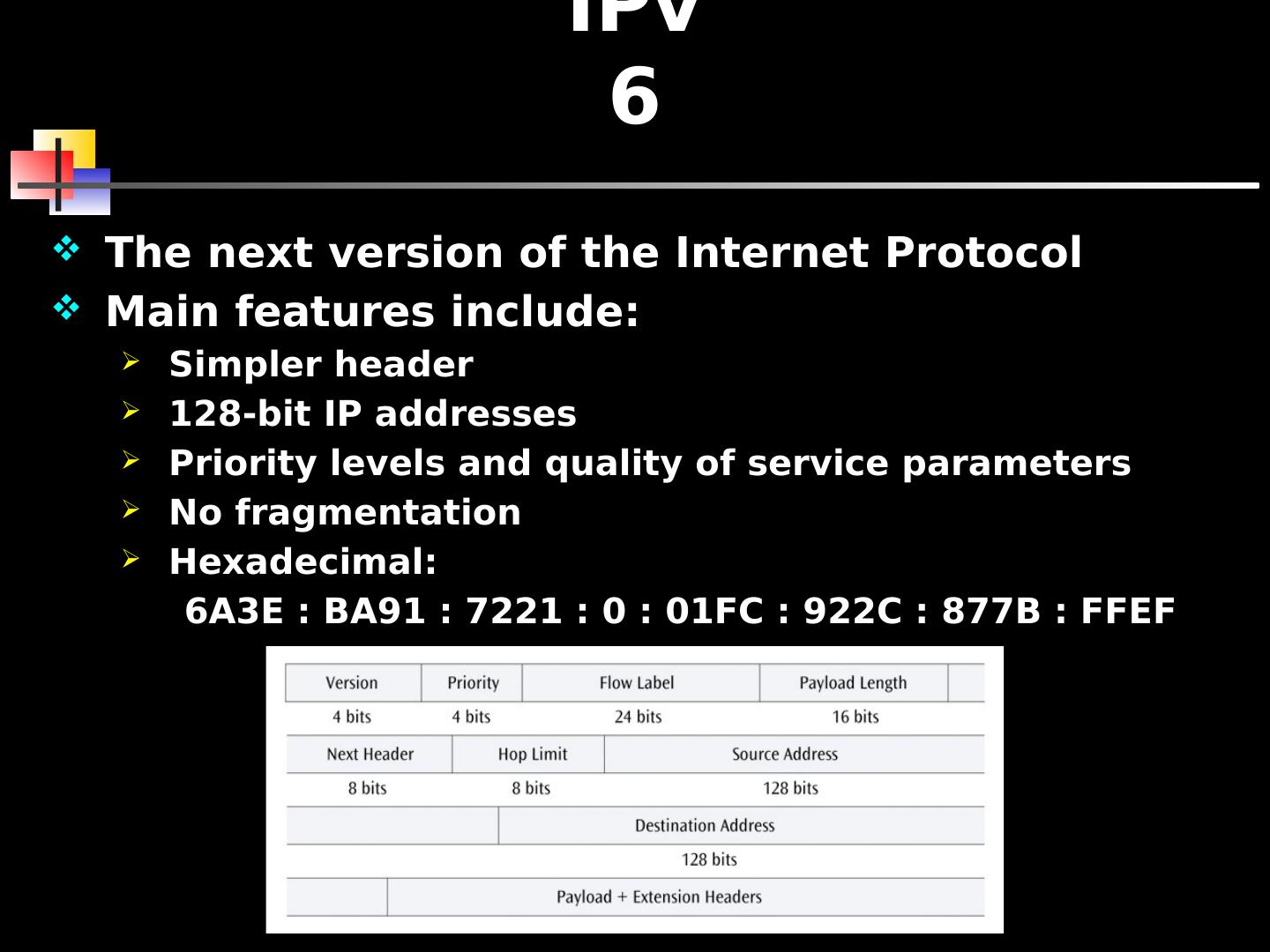
12 .IPv6 The next version of the Internet Protocol Main features include: Simpler header 128-bit IP addresses Priority levels and quality of service parameters No fragmentation Hexadecimal : 6A3E : BA91 : 7221 : 0 : 01FC : 922C : 877B : FFEF
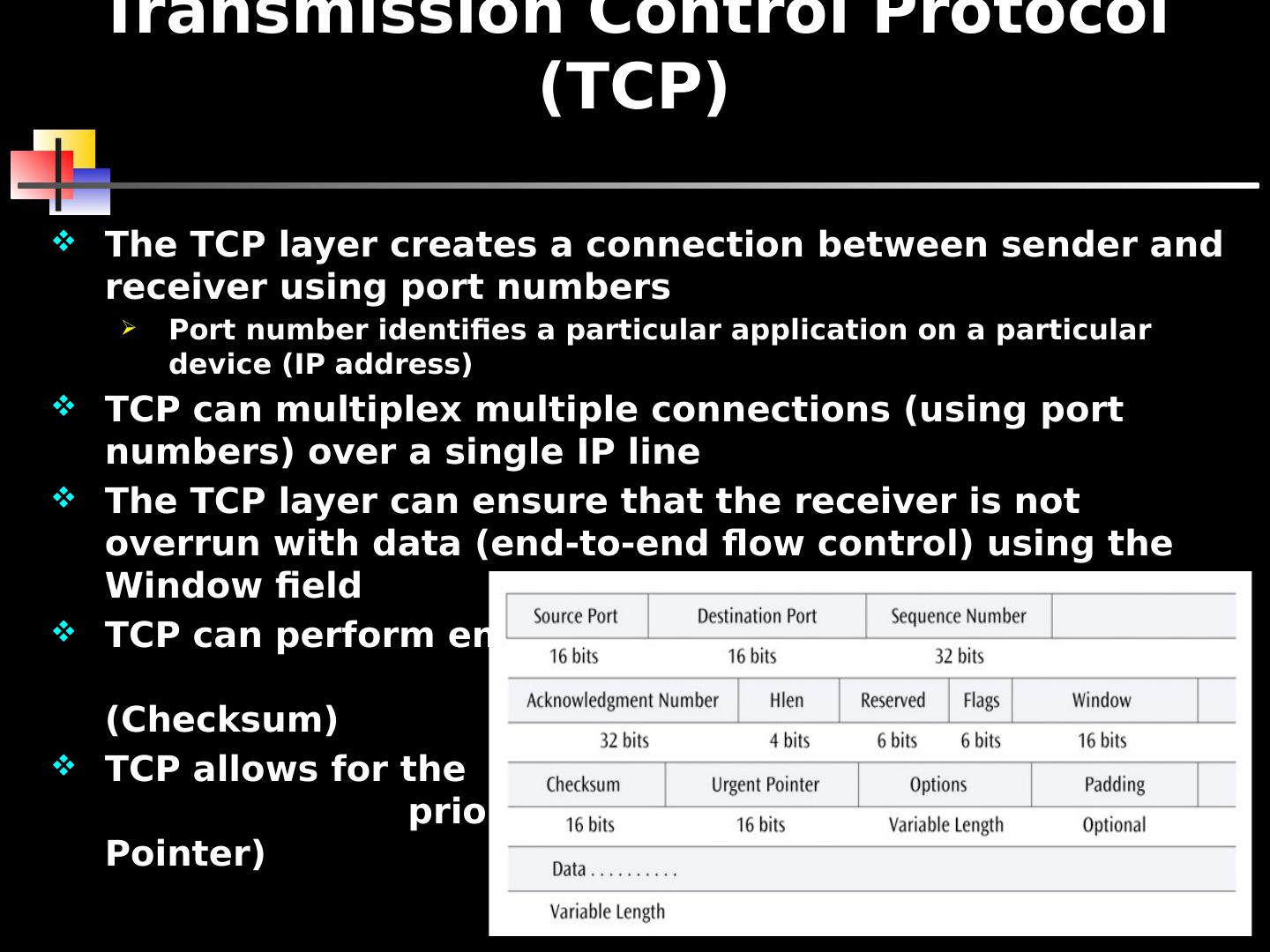
13 .The TCP layer creates a connection between sender and receiver using port numbers Port number identifies a particular application on a particular device (IP address) TCP can multiplex multiple connections (using port numbers) over a single IP line The TCP layer can ensure that the receiver is not overrun with data (end-to-end flow control) using the Window field TCP can perform end -to-end error correction (Checksum) TCP allows for the sending of high priority data (Urgent Pointer) Transmission Control Protocol (TCP)
14 .ICMP, which is used by routers and nodes, performs the error reporting for the Internet Protocol ICMP reports errors such as invalid IP address, invalid port address, and the packet has hopped too many times User Datagram Protocol A transport layer protocol used in place of TCP Where TCP supports a connection-oriented application, UDP is used with connectionless applications UDP also encapsulates a header onto an application packet but the header is much simpler than TCP Address Resolution Protocol When an IP packet has traversed the Internet and encounters the destination LAN, how does the packet find the destination workstation? Even though the destination workstation may have an IP address, a LAN does not use IP addresses to deliver frames A LAN uses the MAC layer address ARP translates an IP address into a MAC layer address so a frame can be delivered to the proper workstation ICMP, UDP, ARP
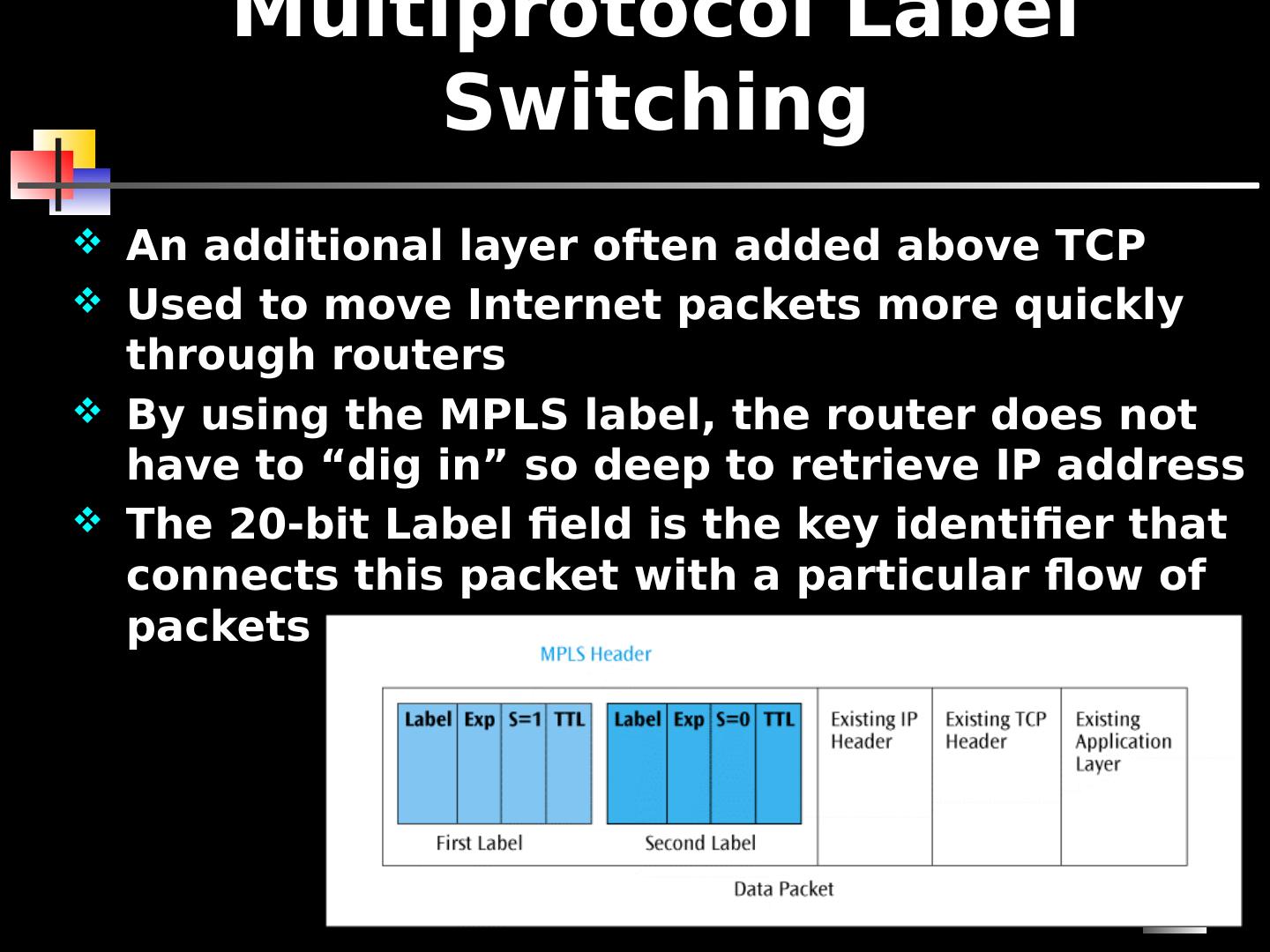
15 .15 Multiprotocol Label Switching An additional layer often added above TCP Used to move Internet packets more quickly through routers By using the MPLS label, the router does not have to “dig in” so deep to retrieve IP address The 20-bit Label field is the key identifier that connects this packet with a particular flow of packets
16 .An IP address can be assigned to a workstation permanently (static assignment) or dynamically Dynamic IP address assignment is a more efficient use of scarce IP addresses When a DHCP client issues an IP request, the DHCP server looks in its static table If no entry exists, the server selects an IP address from an available pool Address assigned by the DHCP server is temporary Part of agreement includes a specific period of time If no time period specified, the default is one hour DHCP clients may negotiate for a renewal before the time period expires DHCP
17 .NAT lets a router represent an entire local area network to the Internet as a single IP address Thus all traffic leaving this LAN appears as originating from a global IP address All traffic coming into this LAN uses this global IP address This security feature allows a LAN to hide all the workstation IP addresses from the Internet Since outside world cannot see into the LAN, you do not need to use registered IP addresses on the inside LAN We can use the following blocks of addresses for private use: 10.0.0.0 – 10.255.255.255 172.16.0.0 – 172.31.255.255 192.168.0.0 – 192.168.255.255 NAT (I)
18 .When a user on inside sends a packet to the outside, the NAT interface changes the user’s inside address to the global IP address This change is stored in a cache When the response comes back, the NAT looks in the cache and switches the addresses back No cache entry? The packet is dropped UNLESS: NAT has a service table of fixed IP address mappings This service table allows packets to originate from the outside NAT (II)
19 .Tunneling Protocols & Virtual Private Networks (VPNs) The Internet is not normally a secure system If a person wants to use the Internet to access a corporate computer system, how can a secure connection be created? One possibility: Creating a virtual private network (VPN) A VPN creates a secure connection through the Internet by using a tunneling protocol Security supported by IPsec (IP security)
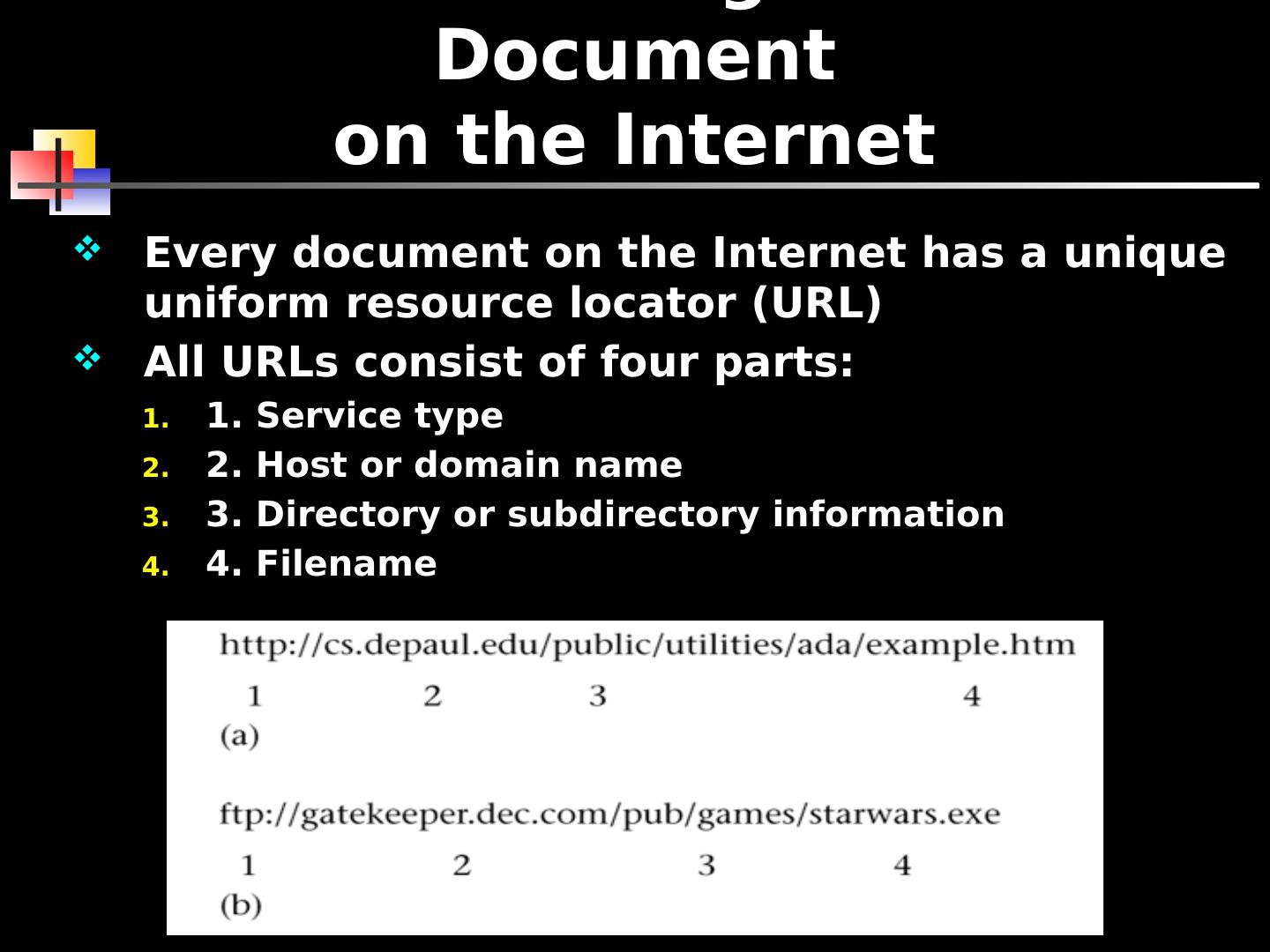
20 .Every document on the Internet has a unique uniform resource locator (URL) All URLs consist of four parts: 1. Service type 2. Host or domain name 3. Directory or subdirectory information 4. Filename Locating a Document on the Internet
21 .A large, distributed database of URLs and IP addresses The first operation performed by DNS is to query a local database for URL/IP address information If the local server does not recognize the address, the server at the next level will be queried Eventually the root server for URL/IP addresses will be queried If root server has the answer, results are returned If root server recognizes domain name but not the extension in front of the domain name, the root server will query the server at the domain name’s location When the domain’s server returns results, they are passed back through the chain of servers (and their caches) Domain Name System (DNS)
22 .Internet Services Electronic mail File transfer protocol (FTP) Remote login (Telnet) VoIP (Voice over IP) Listservs Usenet Streaming audio and video Instant messaging, Tweets, and Blogs
23 .Electronic Mail E-mail programs can create, send, receive, and store e-mails, as well as reply to, forward, and attach non-text files Multipurpose Internet Mail Extension (MIME) is used to send e-mail attachments Simple Mail Transfer Protocol (SMTP) is used to transmit e-mail messages Post Office Protocol version 3 (POP3) and Internet Message Access Protocol (IMAP) are used to hold and later retrieve e-mail messages
24 .FTP FTP used to transfer files across the Internet User can upload or download a file The URL for an FTP site begins with ftp://… Three most common ways to access an FTP site are: Through a browser Using a canned FTP program Issuing FTP commands at a text-based command prompt
25 .Telnet Allows a user to remotely login to a distant computer site User usually needs a login and password to remote computer site User saves money on long distance telephone charges
26 .Voice Over IP (I) The transfer of voice signals using a packet switched network and the IP protocol VoIP can be internal to a company (private VoIP) or can be external using the Internet VoIP consumes many resources and may not always work well, but can be cost effective in certain situations Three basic ways to make a telephone call using VoIP: PC to PC using sound cards and headsets (or speakers and microphone) PC to telephone (need a gateway to convert IP addresses to telephone numbers) Telephone to telephone (need gateways)
27 .Voice Over IP (II) Three functions necessary to support voice over IP: Voice must be digitized (PCM, 64 kbps, fairly standard) 64 kbps voice must be compressed Once the voice is compressed, the data must be transmitted How can we transport compressed voice? H.323 - Created in 1996 by ITU-T Actually, H.323 created for a wide range of applications both audio and video and not for TCP/IP networks Session Initiation Protocol (SIP) - Created by IETF specifically for supporting the transfer of voice over the Internet Many feel SIP will surpass H.323 ENUM: A protocol that supports VoIP Converts telephone numbers to fully qualified domain name addresses For example, the telephone number 312 555-1212 will be converted to 2.1.2.1.5.5.5.2.1.3.1.e164.arpa
28 .Listservs A popular software program used to create and manage Internet mailing lists When an individual sends an e-mail to a listserv, the listserv sends a copy of the message to all listserv members Listservs can be useful business tools for individuals trying to follow a particular area of study
29 .Usenet A voluntary set of rules for passing messages and maintaining newsgroups A newsgroup is the Internet equivalent of an electronic bulletin board system Thousands of Usenet groups exist on virtually any topic